Main worldwide occasions appeal to not simply international audiences but additionally distributed denial-of-service (DDoS) assaults. The Milano Cortina 2026 Winter Video games proved no exception: DDoS assault quantity towards Italian infrastructure within the nation surged 181 % over 2025 ranges, which had been themselves elevated by sustained NoName057(16) campaigns. Attackers handled the Winter Video games calendar as an operational playbook, escalating two weeks earlier than opening ceremonies and terminating abruptly after the occasion’s closing.
Key Findings
- Attack volumes 6–10x historic ranges through the Winter Video games interval (February 6–23, 2026)
- Peak assault rely reached greater than 2,200 assaults on February 23
- NoName057(16) dominated public DDoS hacktivist claims with 47, though ransomware teams (Qilin, LockBit 5.0) additionally claimed success in varied assaults
- Tactical shift from pre-Winter Video games high-bandwidth assaults (412.89Gbps peak) to Winter Video games-period high-throughput assaults
- Geographic focus on Milan (Winter Video games cohost), Cortina infrastructure (resorts, ski websites), and symbolic targets (consulates, protection)
Temporal Evaluation
Attack exercise in Italy might be divided into three distinct durations:
Pre-Winter Video games (January 20–February 5): 4,963 assaults, averaging 300 day by day. The primary escalation occurred January 22, with triple the 2024 and 2025 ranges for comparable dates. January 25 recorded most site visitors depth of 412.89Gbps, with common bandwidth per assault starting from 0.74 to five.45Gbps. These high-magnitude assaults counsel testing community capability limits and defensive responses.
Winter Video games interval (February 6–23): 12,963 assaults, averaging 720 day by day. This era accounted for 56 % of whole assault quantity and 6x instances larger assault exercise in contrast with 2024 and 2025. Exercise escalated from 191 assaults on February 16 to 1,890 on February 23. Throughout the Winter Video games, we will see tactical shifts in assault sorts to packet price–intensive patterns to maintain stress by way of amount over bandwidth knockouts.
Publish-Winter Video games (February 24–March 3): 5,315 assaults, peaking at 2,281 on February 24—a record-breaking single-day rely representing the very best assault quantity noticed towards Italy previously three years. Exercise declined 88 % to 272 assaults by February 26.
NETSCOUT
Determine 1: Yr-over-year DDoS assault comparability throughout Milano Cortina 2026
The temporal sample with the Winter Video games calendar proven in Determine 1 illustrates the dramatic escalation in assault frequency throughout 2026 in contrast with prior years. Notably, the 5 highest single-day assault counts recorded towards Italy previously three years all occurred through the February 17–25 interval: February 24 (2,281 assaults), February 23 (1,890 assaults), February 21 (1,865 assaults), February 22 (1,828 assaults), and February 20 (1,684 assaults). Past assault quantity, the depth of particular person assaults additionally confirmed vital variation all through the statement interval.
Attack Vector Evaluation
Attackers mixed a number of strategies concurrently, averaging greater than two vectors per assault; UDP flooding was dominant, displaying up in 85 % of assaults, whereas further DDoS assault vectors confirmed up in 87 %, that means most assaults combined direct UDP flooding with amplified site visitors from gadgets inclined to reflection/amplification.
NETSCOUT
Determine 2: Attack vector distribution throughout Milano Cortina 2026
UDP flooding led assaults at 85 %, adopted by DNS amplification (19 %), and memcached amplification (11.8 %). The amplification toolkit prolonged to NTP (7.5 %), STUN (6.6 %), SSDP (5.9 %), and SNMP (5 %).
Risk Actor Declare Evaluation
Between February 4 and February 24, 2026, risk actors publicly claimed accountability for assaults focusing on Italian infrastructure by way of social media and Telegram channels. These claims characterize self-reported attribution and haven’t been independently validated towards noticed DDoS telemetry.
NoName057(16) dominated claims exercise with 47 assaults claimed towards Italy throughout this era, representing 40 % of all of the attribution. This represents notable focus of NoName exercise: The group claimed a complete of 488 assaults globally throughout similar timeframe, that means Italy accounted for 10 % of NoName’s international focusing on. Historic evaluation exhibits that between December 1 and February 3, NoName057(16) claimed just one assault towards Italy and made no claims towards Italy after February 28, 2026, indicating the Winter Video games interval attracting the risk actor.
Secondary actors generated 60 % of the remaining claims, however in considerably decrease declare volumes through the Winter Video games interval: Server Killers (8 claims), Z-Pentest Alliance (4 claims), Darkish Storm Crew (3 claims). The remaining 47 attacker claims had been distributed amongst ransomware teams, particular person actors, and varied entities.
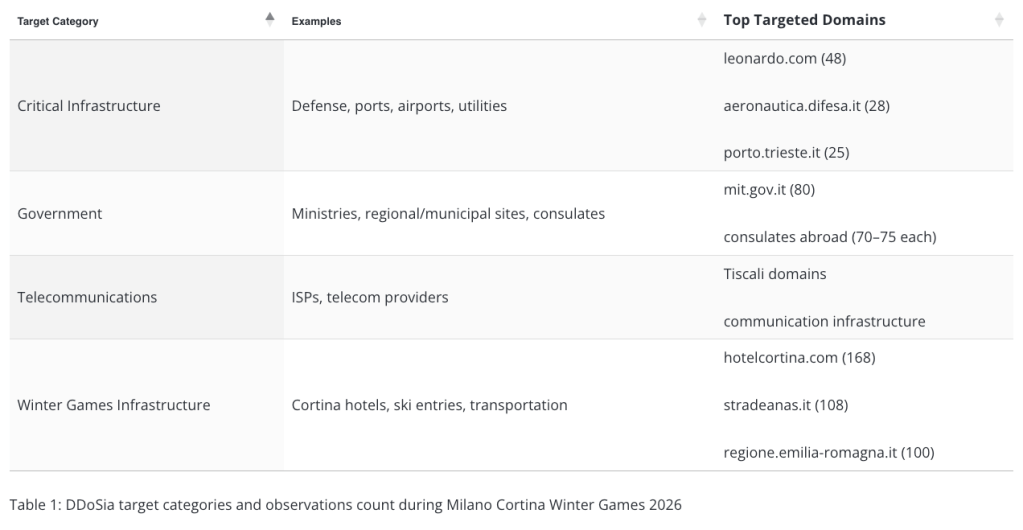
DDoSia Evaluation
DDoSia is a homegrown DDoS platform developed by NoName057(16) working since early 2022. DDoSia detection occasions by the NETSCOUT ASERT workforce recorded 3,491 assaults towards 74 distinctive Italian domains throughout pre-Winter Video games and Winter Video games durations, aimed toward disrupting the Winter Video games infrastructure, authorities operations, and important providers. The first vectors embody HTTP/HTTPS/HTTP2 floods; TCP floods on port 80, 443, 2222, 8080; and slowloris-style useful resource exhaustion assaults.
Desk 1: DDoSia goal classes and observations rely throughout Milano Cortina Winter Video games 2026
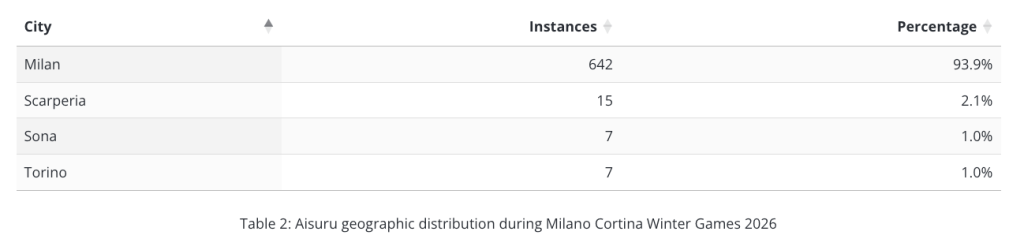
Aisuru IoT Botnet Evaluation
Aisuru operates as a Mirai-derivative Web of Issues (IoT) botnet first disclosed in August 2024, comprising of greater than 1 million compromised client routers, cameras, and IoT methods. (Word: This evaluation interval is previous to the current law-enforcement takedown motion impacting the Aisuru botnet.) The botnet capabilities as DDoS-for-hire providers, with assaults of as much as 31Tbps purported. After observing dominance of direct-path UDP flooding—the commonest Aisuru assault sort—NETSCOUT’s ASERT workforce tracked greater than 683 Aisuru-tagged cases towards Italian cities, with Milan absorbing 94 % of exercise (642 cases).
NETSCOUT
Desk 2: Aisuru geographic distribution throughout Milano Cortina Winter Video games 2026
Conclusion
The DDoS marketing campaign focusing on Italy through the Milano Cortina 2026 Winter Video games demonstrated how main worldwide occasions create predictable home windows for coordinated cyberthreat exercise. The assault exercise noticed towards Italy between January and March 2026 demonstrates an elevated DDoS risk panorama as in contrast with international DDoS traits throughout the identical durations in prior years. The assaults represented a 181 % frequency improve in contrast with 2025, when Italy was the goal of NoName057 as a result of international geopolitical tensions reported by the ASERT workforce within the “Italy within the Crosshairs” marketing campaign.
International visibility by way of NETSCOUT ATLAS risk intelligence and adaptive DDoS safety by way of NETSCOUT Arbor merchandise equip organizations with sturdy and proactive protection methods, guaranteeing the supporting infrastructure of main worldwide occasions stays undisrupted.
To study extra, go to us right here.