The China-based cybercrime group often called Silver Fox has been linked to a brand new marketing campaign concentrating on organizations in Russia and India with a brand new malware referred to as ABCDoor.
The exercise concerned utilizing phishing emails that mimic correspondence from the Revenue Tax Division of India in December 2025, adopted by the same marketing campaign geared toward Russian entities.
“Each waves adopted a virtually an identical construction: phishing emails had been styled as official notices relating to tax audits or prompted customers to obtain an archive containing a ‘checklist of tax violations,'” Kaspersky mentioned. “Contained in the archive was a modified Rust-based loader pulled from a public repository. This loader would obtain and execute the well-known ValleyRAT backdoor.”
The marketing campaign is estimated to have impacted organizations throughout the commercial, consulting, retail, and transportation sectors. Greater than 1,600 phishing emails had been flagged between early January and early February.
What’s notable about these phishing waves is the supply of a brand new ValleyRAT plugin that features as a loader for a beforehand undocumented Python-based backdoor codenamed ABCDoor. The backdoor, per the Russian cybersecurity firm, has been a part of the risk actor’s arsenal since at the very least December 19, 2024, and was put to make use of in cyber assaults starting February or March 2025.
The start line of the assault chain is a phishing electronic mail containing a PDF file, which options two clickable hyperlinks that result in the obtain of a ZIP or RAR archive hosted on “abc.haijing88[.]com.” Within the marketing campaign detected in December 2025, the malicious code is claimed to have been embedded straight inside the recordsdata hooked up to the e-mail.
Current inside the archive is an executable that mimics a PDF file. The binary is a modified model of an open-source shellcode loader and antivirus bypass framework referred to as RustSL. Silver Fox’s first recorded use of RustSL dates again to late December 2025.
The top aim of the Silver Fox RustSL variant is to unpack the encrypted malicious payload, whereas implementing country-based geofencing and setting checks to detect digital machines and sandboxes. Whereas the GitHub variant solely consists of China in its nation checklist, the bespoke model options India, Indonesia, South Africa, Russia, and Cambodia.
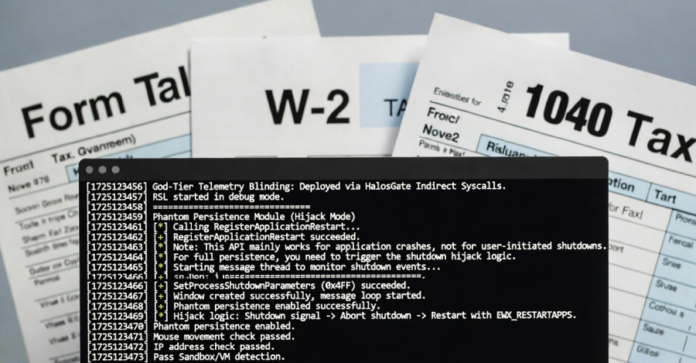
One variant of the loader has been discovered to make use of a novel referred to as Phantom Persistence to ascertain persistence on the compromised host. It was first documented in June 2025.

“This methodology abuses performance designed to permit functions requiring a reboot for updates to finish the set up course of correctly,” Kaspersky defined. “The attackers intercept the system shutdown sign, halt the traditional shutdown sequence, and set off a reboot underneath the guise of an replace for the malware. Consequently, the loader forces the system to execute it upon OS startup.”
The encrypted payload loaded by RustSL ends in the obtain of the encrypted ValleyRAT (aka Winos 4.0) malware, with the core element (“login-module.dll_bin”) liable for command-and-control (C2) communications, command execution, and retrieval and execution of extra modules.
One of many customized modules deployed as a part of the assault following a second geofencing test is ABCDoor, which contacts an exterior server by way of HTTPS and processes incoming messages to facilitate persistence, deal with backdoor updates and removing, acquire knowledge resembling screenshots, allow distant mouse and keyboard management, carry out file system operations, handle system processes, and exfiltrate clipboard contents.
As just lately as November 2025, Silver Fox has been noticed utilizing a JavaScript loader to ship ABCDoor, with the loader distributed by way of self-extracting (SFX) archives that had been packaged inside ZIP archives doubtless despatched by way of phishing emails. Newer variations of RustSL have since expanded the geographic focus to incorporate Japan.
The best variety of assaults has been detected in India, Russia, and Indonesia, adopted by South Africa and Japan. The vast majority of loader samples found have employed tax-themed lures to mimic the an infection sequence.
“Since 2024, [Silver Fox] has advanced right into a dual-track operational mannequin that concurrently conducts worthwhile in depth opportunistic actions and espionage actions,” S2W mentioned. “Within the early levels, the group focused China for assaults, however later expanded its operational scope to Taiwan and Japan.”
“The Silver Fox group primarily makes use of extremely personalized spear phishing methods for preliminary infiltration, deploying subtle and diversified assault situations tailor-made to the seasonal problems with the goal nation and the goal’s work traits.”