The Midnight Blizzard and Cloudflare-Atlassian cybersecurity incidents raised alarms in regards to the vulnerabilities inherent in main SaaS platforms. These incidents illustrate the stakes concerned in SaaS breaches — safeguarding the integrity of SaaS apps and their delicate information is essential however just isn’t simple. Widespread risk vectors similar to subtle spear-phishing, misconfigurations and vulnerabilities in third-party app integrations show the advanced security challenges going through IT methods.
Within the case of Midnight Blizzard, password spraying towards a take a look at setting was the preliminary assault vector. For Cloudflare-Atlassian, risk actors initiated the assault through compromised OAuth tokens from a previous breach at Okta, a SaaS identification security supplier.
What Precisely Occurred?
Microsoft Midnight Blizzard Breach
Microsoft was focused by the Russian “Midnight Blizzard” hackers (also called Nobelium, APT29, or Cozy Bear) who’re linked to the SVR, the Kremlin’s international intelligence service unit.
Within the Microsoft breach, the risk actors:
- Used a password spray technique on a legacy account and historic take a look at accounts that didn’t have multi-factor authentication (MFA) enabled. In line with Microsoft, the risk actors “[used] a low variety of makes an attempt to evade detection and keep away from account blocks primarily based on the amount of failures.”
- Leveraged the compromised legacy account as an preliminary entry level to then hijack a legacy take a look at OAuth app. This legacy OAuth app had high-level permissions to entry Microsoft’s company setting.
- Created malicious OAuth apps by exploiting the legacy OAuth app’s permissions. As a result of the risk actors managed the legacy OAuth app, they may preserve entry to the functions even when they misplaced entry to the initially compromised account.
- Granted admin Change permissions and admin credentials to themselves.
- Escalated privileges from OAuth to a brand new person, which they managed.
- Consented to the malicious OAuth functions utilizing their newly created person account.
- Escalated the legacy utility’s entry additional by granting it full entry to M365 Change On-line mailboxes. With this entry, Midnight Blizzard might view M365 electronic mail accounts belonging to senior employees members and exfiltrate company emails and attachments.
 |
| Recreation of illustration by Amitai Cohen |
Cloudflare-Atlassian Breach
On Thanksgiving Day, November 23, 2023, Cloudflare’s Atlassian methods had been additionally compromised by a nation-state assault.
- This breach, which began on November 15, 2023, was made potential by using compromised credentials that had not been modified following a earlier breach at Okta in October 2023.
- Attackers accessed Cloudflare’s inside wiki and bug database, enabling them to view 120 code repositories in Cloudflare’s Atlassian occasion.
- 76 supply code repositories associated to key operational applied sciences had been doubtlessly exfiltrated.
- Cloudflare detected the risk actor on November 23 as a result of the risk actor linked a Smartsheet service account to an admin group in Atlassian.
Risk Actors More and more Goal SaaS
These breaches are a part of a broader sample of nation-state actors concentrating on SaaS service suppliers, together with however not restricted to espionage and intelligence gathering. Midnight Blizzard beforehand engaged in vital cyber operations, together with the 2021 SolarWinds assault.
These incidents underscore the significance of steady monitoring of your SaaS environments and the continuing danger posed by subtle cyber adversaries concentrating on essential infrastructure and operational tech stack. Additionally they spotlight vital vulnerabilities associated to SaaS identification administration and the need for stringent Third-party app danger administration practices.
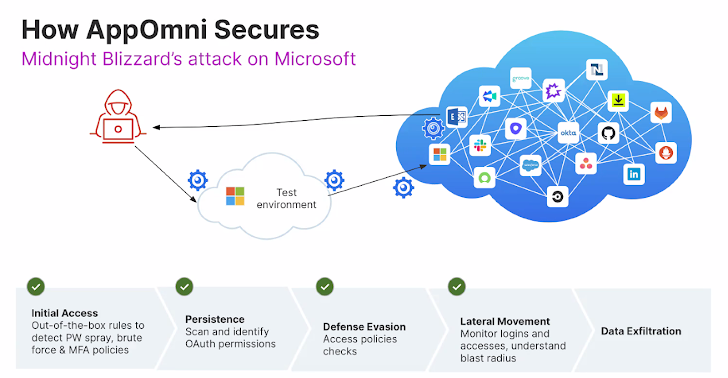
Attackers use frequent techniques, methods and procedures (TTPs) to breach SaaS suppliers by the next kill chain:
- Preliminary entry: Password spray, hijacking OAuth
- Persistence: Impersonates admin, creates further OAuth
- Protection Evasion: Extremely privileged OAuth, no MFA
- Lateral Motion: Broader compromise of linked apps
- Data Exfiltration: Seize privileged and delicate information out of apps
Breaking the SaaS Kill Chain
One efficient solution to break the kill chain early is with steady monitoring, granular coverage enforcement, and proactive lifecycle administration over your SaaS environments. A SaaS Safety Posture Administration (SSPM) platform like AppOmni might help with detecting and alerting on:
- Preliminary Entry: Out-of-the-box guidelines to detect credential compromise, together with password spraying, brute drive assaults, and unenforced MFA insurance policies
- Persistence: Scan and establish OAuth permissions and detect OAuth hijacking
- Protection Evasion: Entry coverage checks, detect if a brand new identification supplier (IdP) is created, detect permission modifications.
- Lateral Motion: Monitor logins and privileged entry, detect poisonous mixtures, and perceive the blast radius of a doubtlessly compromised account
Be aware: This expertly contributed article is written by Beverly Nevalga, AppOmni.




