A vital vulnerability in Nginx UI with Mannequin Context Protocol (MCP) help is now being exploited within the wild for full server takeover with out authentication.
The flaw, tracked as CVE-2026-33032, is attributable to nginx-ui leaving the ‘/mcp_message’ endpoint unprotected, permitting distant attackers to invoke privileged MCP actions with out credentials.
As a result of these actions contain writing and reloading nginx configuration information, a single unauthenticated request can modify server conduct and successfully take over the online server.

“[…] any community attacker can invoke all MCP instruments with out authentication, together with restarting nginx, creating/modifying/deleting nginx configuration information, and triggering automated config reloads – reaching full nginx service takeover,” reads NIST’s descripion of the flaw within the Nationwide Vulnerability Database (NVD).
NGNIX launched a repair for the flaw in model 2.3.4 on March 15, a day after researchers on the AI workflow security firm Pluto Safety AI reported it. Nonetheless, the vulnerability identifier, together with technical particulars and a proof-of-concept (PoC) exploit, emerged on the finish of the month.
Within the CVE Panorama report earlier this week, risk intelligence firm Recorded Future notes that CVE-2026-33032 is beneath lively exploitation.
Nginx UI is a web-based administration interface for the Nginx net server. The library could be very well-liked, with greater than 11,000 stars on GitHub and 430,000 Docker pulls.
Based mostly on Pluto Safety’s web scans utilizing the Shodan engine, there are presently 2,600 publicly uncovered cases doubtlessly susceptible to assaults. Most are in China, the USA, Indonesia, Germany, and Hong Kong.
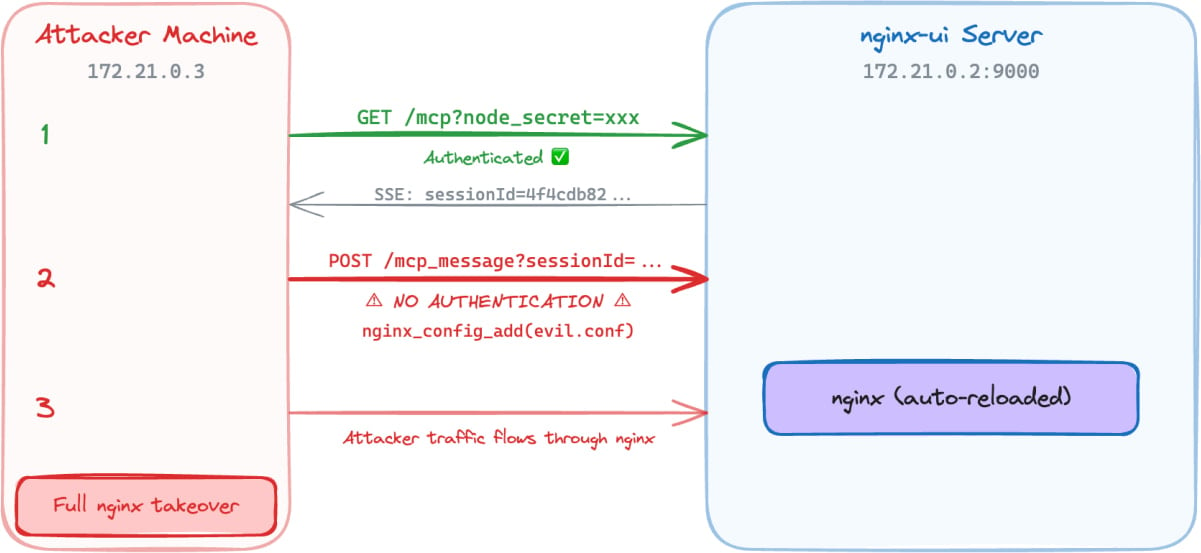
In a report at this time, Pluto Safety’s Yotam Perkal says that exploitation solely requires community entry and is achieved by establishing an SSE connection, opening an MCP session, after which utilizing the returned ‘sessionID’ to ship requests to the ‘/mcp_message’ endpoint.
Supply: Pluto Safety
From there, attackers can invoke MCP instruments with out authentication and take the next actions:
- Hook up with the goal nginx-ui occasion
- Ship requests with none authentication headers
- Acquire entry to all 12 MCP instruments (7 harmful)
- Learn nginx configuration information and exfiltrate them
- Inject a brand new nginx server block with malicious configuration
- Set off automated nginx reload
Pluto Safety’s demo exhibits that an attacker can use the unauthenticated MCP message endpoint to execute privileged nginx administration actions, carry out config injection, and in the end take management of the nginx server, all with out authentication.
Given the lively exploitation standing and the provision of public PoCs, system directors are beneficial to use the out there security updates as quickly as attainable. The most recent safe model of nginx-ui is 2.3.6, launched final week.

Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, exhibits the place protection ends, and gives practitioners with three diagnostic questions for any instrument analysis.




