Google on Thursday introduced an enhanced model of Secure Searching to supply real-time, privacy-preserving URL safety and safeguard customers from visiting doubtlessly malicious websites.
“The Customary safety mode for Chrome on desktop and iOS will verify websites in opposition to Google’s server-side checklist of identified unhealthy websites in real-time,” Google’s Jonathan Li and Jasika Bawa stated.
“If we suspect a website poses a danger to you or your gadget, you may see a warning with extra info. By checking websites in actual time, we anticipate to dam 25% extra phishing makes an attempt.”
Up till now, the Chrome browser used a locally-stored checklist of identified unsafe websites that is up to date each 30 to 60 minutes, after which leveraging a hash-based strategy to check each website visited in opposition to the database.
Google first revealed its plans to modify to real-time server-side checks with out sharing customers’ looking historical past with the corporate in September 2023.
The rationale for the change, the search large stated, is motivated by the truth that the checklist of dangerous web sites is rising at a speedy tempo and that 60% of the phishing domains exist for lower than 10 minutes, making it tough to dam.
“Not all gadgets have the sources obligatory to take care of this rising checklist, nor are they at all times in a position to obtain and apply updates to the checklist on the frequency obligatory to profit from full safety,” it added.
Thus, with the brand new structure, each time a consumer makes an attempt to go to an internet site, the URL is checked in opposition to the browser’s world and native caches containing identified protected URLs and the outcomes of earlier Secure Searching checks with a view to decide the positioning’s standing.
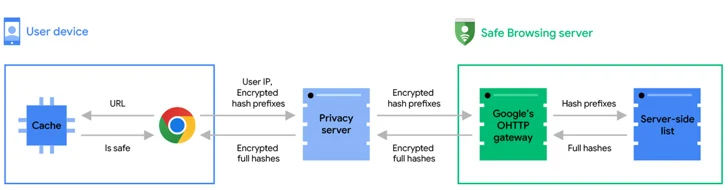
Ought to the visited URL be absent from the caches, a real-time verify is carried out by obfuscating the URL into 32-byte full hashes, that are then truncated into 4-byte lengthy hash prefixes, encrypted, and despatched to a privateness server.
“The privateness server removes potential consumer identifiers and forwards the encrypted hash prefixes to the Secure Searching server through a TLS connection that mixes requests with many different Chrome customers,” Google defined.
The Secure Searching server subsequently decrypts the hash prefixes and matches them in opposition to the server-side database to return full hashes of all unsafe URLs that match one of many hash prefixes despatched by the browser.
Lastly, on the consumer facet, the complete hashes are in contrast in opposition to the complete hashes of the visited URL, and a warning message is displayed if a match is discovered.
Google additionally confirmed that the privateness server is nothing however an Oblivious HTTP (OHTTP) relay operated by Fastly that sits between Chrome and the Secure Searching server to stop the latter from entry customers’ IP addresses, thereby stopping it from correlating the URL checks with a consumer’s web looking historical past.
“Finally, Secure Searching sees the hash prefixes of your URL however not your IP handle, and the privateness server sees your IP handle however not the hash prefixes,” the corporate emphasised. “No single social gathering has entry to each your identification and the hash prefixes. As such, your looking exercise stays non-public.”




