The ShinyHunters extortion group stole the private info of 5.5 million people after breaching the programs of dwelling security big ADT earlier this month, in line with data breach notification service Have I Been Pwned.
Based in 1874 as American District Telegraph, ADT is the oldest and largest dwelling security firm in the USA, at present offering monitored security and good dwelling options to over 6 million residential and small-business prospects.
ADT has beforehand disclosed two different data breaches in August 2024 and October 2024 that uncovered worker and buyer info.

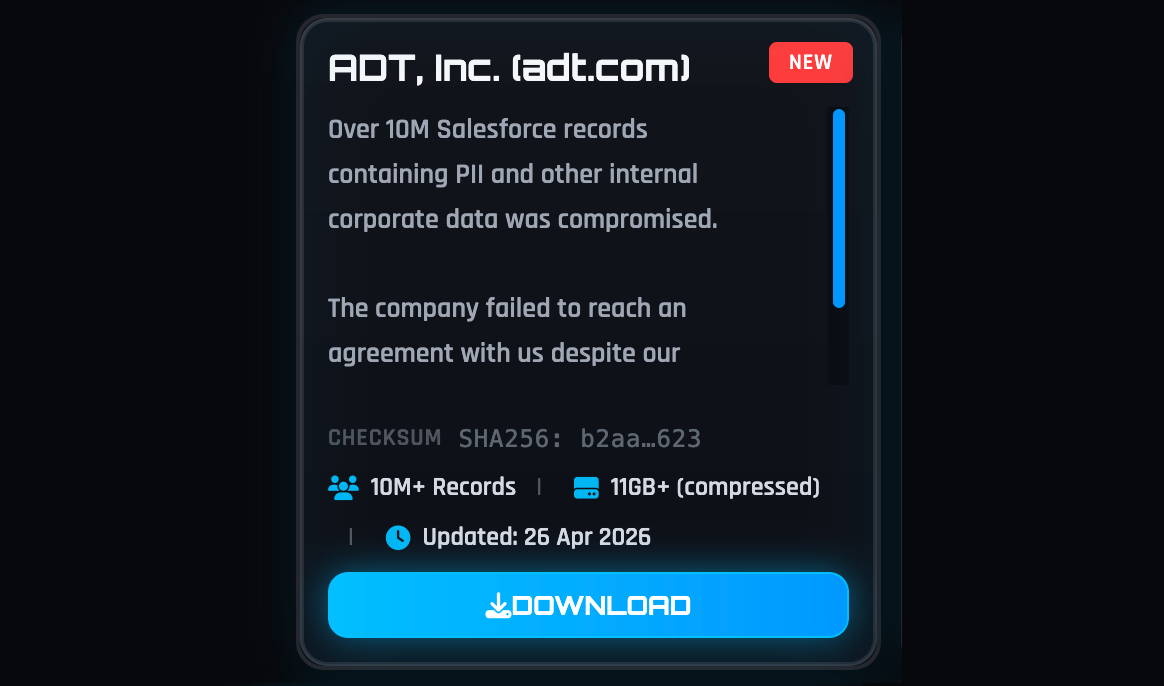
Have I Been Pwned’s report comes after ShinyHunters claimed final week that they’d stolen over 10 million data containing personally identifiable info (PII) and ADT company knowledge.
When requested to verify the cybercrime group’s claims, ADT advised BleepingComputer that it detected the breach on April 20 and {that a} follow-up investigation discovered the intrusion was restricted however allowed the attackers to entry some people’ private info.
“The investigation confirmed that the knowledge concerned was restricted to names, telephone numbers, and addresses. In a small proportion of instances, dates of start and the final 4 digits of Social Safety numbers or Tax IDs had been included,” ADT advised BleepingComputer.
“Critically, no fee info — together with financial institution accounts or bank cards — was accessed, and buyer security programs weren’t affected or compromised in any approach.”
The cybercrime group has since leaked an 11GB archive of stolen knowledge on its darkish internet leak web site after failing to extort the corporate.
Whereas ADT has but to reveal the overall variety of affected people, Have I Been Pwned analyzed the stolen knowledge and stated the breach uncovered the info of 5.5 million folks, together with distinctive e mail addresses, names, dates of start, telephone numbers, bodily addresses, and partial government-issued IDs.
The extortion group advised BleepingComputer that they’d allegedly breached the corporate after compromising an worker’s Okta single sign-on (SSO) account in a voice phishing (vishing) assault. Utilizing this worker account, the attackers stated they gained entry and stole knowledge from the corporate’s Salesforce occasion.
ShinyHunters has been behind widespread vishing campaigns that started final yr and goal staff’ and Enterprise Course of Outsourcing (BPO) brokers’ Microsoft Entra, Okta, and Google SSO accounts.
After breaching company SSO accounts, they steal knowledge from related SaaS purposes corresponding to Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and others.
Final week, ShinyHunters additionally claimed to have stolen greater than 9 million data from Medtronic, the world’s largest medical system maker by income, with operations in 150 international locations.
Different corporations that the extortion claimed to have breached in current weeks embody the European Fee, Rockstar Video games, edtech big McGraw Hill, and, extra not too long ago, comfort retailer chain 7-Eleven, cruise line operator Carnival, quick vogue retailer Zara, and on-line coaching firm Udemy.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




