Menace actors are more and more utilizing a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy to tug off account takeover assaults geared toward high-ranking executives at outstanding firms.
In response to Proofpoint, an ongoing hybrid marketing campaign has leveraged the service to focus on 1000’s of Microsoft 365 person accounts, sending roughly 120,000 phishing emails to a whole lot of organizations worldwide between March and June 2023.
Practically 39% of the a whole lot of compromised customers are mentioned to be C-level executives, together with CEOs (9%) and CFOs (17%). The assaults have additionally singled out personnel with entry to monetary property or delicate info. At the very least 35% of all compromised customers had further account protections enabled.
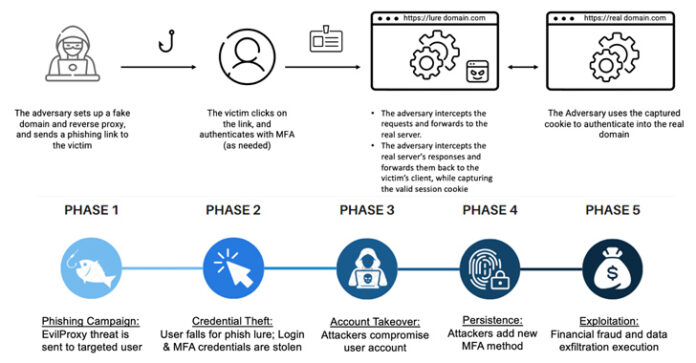
The campaigns are seen as a response to the elevated adoption of multi-factor authentication (MFA) in enterprises, prompting risk actors to evolve their techniques to bypass new security layers by incorporating adversary-in-the-middle (AitM) phishing kits to siphon credentials, session cookies, and one-time passwords.
“Attackers use new superior automation to precisely decide in real-time whether or not a phished person is a high-level profile, and instantly receive entry to the account, whereas ignoring much less profitable phished profiles,” the enterprise security agency mentioned.
EvilProxy was first documented by Resecurity in September 2022, detailing its capability to compromise person accounts related to Apple iCloud, Fb, GoDaddy, GitHub, Google, Dropbox, Instagram, Microsoft, NPM, PyPI, RubyGems, Twitter, Yahoo, and Yandex, amongst others.
It is bought as a subscription for $400 a month, a determine that may climb as much as $600 for Google accounts.
PhaaS toolkits are an evolution of the cybercrime financial system, reducing the barrier for criminals with decrease technical expertise to hold out subtle phishing assaults at scale in a seamless and cost-effective method.
“These days, all an attacker wants is to arrange a marketing campaign utilizing a point-and-click interface with customizable choices, akin to bot detection, proxy detection, and geofencing,” security researchers Shachar Gritzman, Moshe Avraham, Tim Kromphardt, Jake Gionet, and Eilon Bendet mentioned.
“This comparatively easy and low-cost interface has opened a floodgate of profitable MFA phishing exercise.”
The most recent wave of assaults commences with phishing emails that masquerade as trusted companies like Adobe and DocuSign to trick recipients into clicking on malicious URLs that activate a multi-stage redirection chain to take them to a lookalike Microsoft 365 login web page, which capabilities as a reverse proxy to stealthily seize the data entered within the kind.
However in a curious twist, the assaults intentionally skip person site visitors originating from Turkish IP addresses by redirecting them to official web sites, indicating that the marketing campaign operators may very well be primarily based overseas.
A profitable account takeover is adopted by the risk actor taking steps to “cement their foothold” within the group’s cloud surroundings by including their very own MFA technique, akin to a two-factor authenticator app, in order to acquire persistent distant entry and conduct lateral motion and malware proliferation.
The entry is additional monetized to both conduct monetary fraud, exfiltrate confidential information, or promote the compromised person accounts to different attackers.
“Reverse proxy threats (and EvilProxy particularly) are a potent risk in at present’s dynamic panorama and are outcompeting the much less succesful phish kits of the previous,” the researchers mentioned, declaring that “not even MFA is a silver bullet towards subtle cloud-based threats.”
“Though these assaults’ preliminary risk vector is email-based, their closing objective is to compromise and exploit beneficial cloud person accounts, property, and information.”
The event comes as Imperva revealed particulars of an ongoing Russian-origin phishing marketing campaign that goals to deceive potential targets and steal their bank card and financial institution info since at the least Might 2022 through booby-trapped hyperlinks shared through WhatsApp messages.
The exercise spans 800 completely different rip-off domains, impersonating greater than 340 firms throughout 48 languages. This includes well-known banks, postal companies, package deal supply companies, social media, and e-commerce websites.
“By leveraging a high-quality, single-page utility, the scammers have been capable of dynamically create a convincing web site that impersonated a official website, fooling customers right into a false sense of security,” Imperva mentioned.
In one more variation of a social engineering assault recognized by eSentire, malicious actors have been noticed contacting advertising professionals on LinkedIn in an try to distribute a .NET-based loader malware codenamed HawkEyes that, in flip, is used to launch Ducktail, an info stealer with a selected deal with gathering Fb Enterprise account info.
“Ducktail is understood to focus on Fb Advert and Enterprise accounts,” eSentire researchers mentioned. “Operators will use stolen login information so as to add electronic mail addresses to Fb Enterprise accounts. When emails are added, a registration hyperlink is generated by which the risk actor can grant themselves entry.”