Software security firm Checkmarx has confirmed that the LAPSUS$ menace group leaked knowledge stolen from its non-public GitHub repository.
Though the investigation is ongoing, Checkmarx believes that the entry vector was the Trivy supply-chain assault attributed to the hacker group often known as TeamPCP. which supplied entry to credentials from downstream customers.
Utilizing stolen credentials obtained from the Trivy incident, the menace actor was in a position to entry Checkmarx’s GitHub repositories and publish malicious code on March 23.

“Because of that entry, the attackers have been in a position to work together with Checkmarx’s GitHub surroundings and subsequently publish malicious code to sure artifacts,” the corporate explains.
On April 22, on account of their renewed entry or month-long persistence, the attacker printed malicious Docker pictures, VSCode and Open VSX extensions for Checkmarx’s KICS security scanner, which stole credentials, keys, tokens, and config recordsdata.
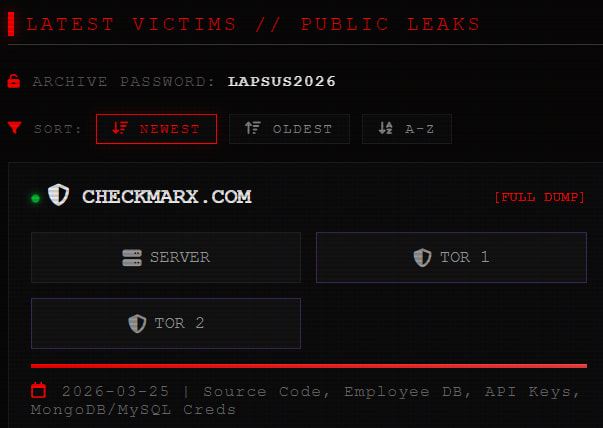
In an replace yesterday, the corporate confirmed that the information that the LAPSUS$ group printed on their extortion portal belonged to Checkmarx and originated from the March 23 compromise.
“Our investigation, carried out with assist from a number one third-party forensic agency, signifies {that a} cybercriminal group has printed knowledge associated to Checkmarx to the darkish net,” reads the replace.
“Based mostly on present proof, we consider this knowledge originated from Checkmarx’s GitHub repository, and that entry to that repository was facilitated by way of the preliminary provide chain assault of March 23, 2026.”
Though Checkmarx and different media retailers reported that this knowledge was leaked on the darkish net, BleepingComputer has discovered that LAPSUS$ has additionally made the 96GB knowledge pack out there by way of clearnet portals.
Supply: BleepingComputer
BleepingComputer has not examined the content material of the leaked knowledge, however Checkmarx assured that it doesn’t comprise buyer data, as this isn’t saved within the firm’s GitHub repository.
A forensic investigation is underway to find out the precise kind of knowledge that has been uncovered.
The corporate states that, if buyer data is discovered within the leaked knowledge, affected people will likely be notified instantly.
Entry to the affected GitHub repository has been blocked till the investigation is full. Checkmarx estimates that it will likely be in a position to share extra particulars inside the subsequent 24 hours.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




