Instructure, the edtech big behind the extensively common Canvas studying administration system (LMS), has reached an “settlement” with the ShinyHunters extortion group to stop the info stolen in a current breach from being leaked on-line.
The corporate says over 30 million educators and college students use its Canvas platform throughout greater than 8,000 faculties and universities worldwide.
In a Tuesday assertion, Instructure mentioned the cybercrime gang additionally returned the stolen knowledge and supplied shred logs confirming its destruction.
“We perceive how unsettling conditions like this may be, and defending our neighborhood stays our high precedence. With that accountability in thoughts, Instructure reached an settlement with the unauthorized actor concerned on this incident,” it mentioned.
“We have now been knowledgeable that no Instructure clients might be extorted because of this incident, publicly or in any other case. This settlement covers all impacted Instructure clients, and there’s no want for particular person clients to try to interact with the unauthorized actor.”
Nevertheless, because the FBI has repeatedly warned, paying a ransom doesn’t assure that menace actors won’t additionally promote the stolen knowledge to different cybercriminals or try and extort the victims once more.
Instructure added that its management will share extra info relating to the incident and the measures it has taken to safe its methods towards future breach makes an attempt in a Might 13 webinar.
ShinyHunters claimed accountability for the breach and mentioned they stole greater than 3.6TB of uncompressed knowledge, after the corporate confirmed that knowledge had been stolen within the cyberattack.
Instructure confirmed to BleepingComputer that ShinyHunters exploited a security challenge in the Free-for-Instructor atmosphere, a free, restricted model of Canvas LMS for particular person educators, to steal the info.
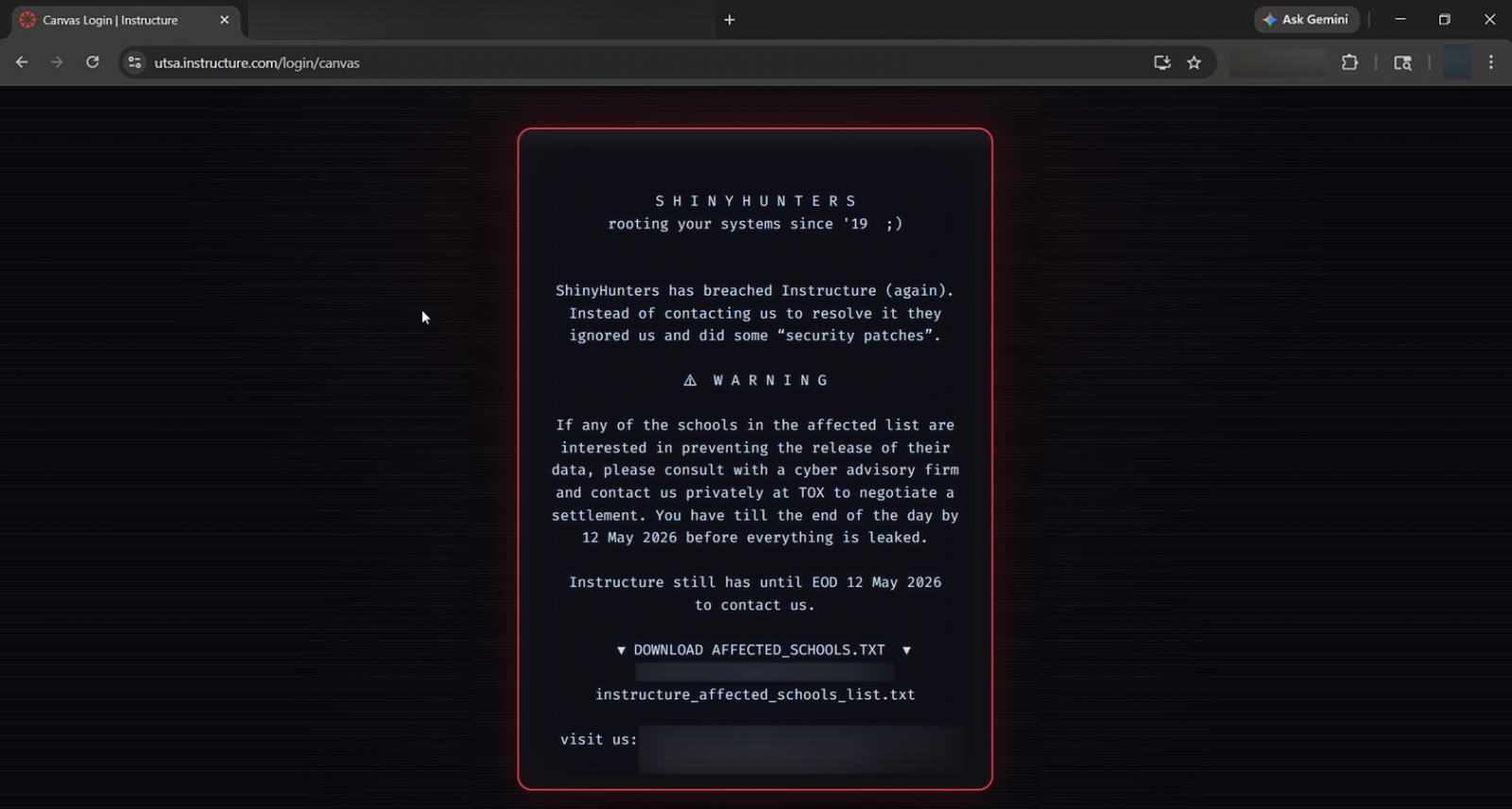
The cybercrime group additionally hacked Instructure once more on Might 7, utilizing the identical vulnerability as within the preliminary intrusion, to deface Canvas login portals and go away an extortion message, warning that the corporate and its clients had till Might 12 to enter negotiations to pay a ransom.
Though the corporate did not share additional particulars on the breach and defacements, BleepingComputer has realized that the attacker exploited a number of cross-site scripting (XSS) vulnerabilities.
ShinyHunters injected malicious JavaScript to exploit Canvas XSS flaws in user-generated content material options, which allowed them to acquire authenticated admin periods and carry out privileged actions.
“The unauthorized actor made modifications to the pages that appeared when some college students and academics had been logged in by way of Canvas,” Instructure mentioned. “Canvas has been restored and is absolutely again on-line and out there to be used. [..] We advocate that clients proceed regular monitoring of their Canvas environments, integrations, and administrative exercise.”
Since then, the corporate has briefly shut down Free-For-Instructor accounts and mentioned that it is working to resolve these security points to stop future incidents.
In September 2025, Instructure disclosed one other breach, additionally claimed by ShinyHunters, that allowed attackers to entry knowledge within the edtech big’s Salesforce occasion.
Different breaches just lately claimed by ShinyHunters embody Google, Cisco, PornHub, the European Fee, on-line relationship big Match Group, Rockstar Video games, residence security big ADT, video service Vimeo, edtech big McGraw-Hill, medical system maker Medtronic, and Spanish fast-fashion retailer Zara.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot





