Checkmarx warned over the weekend {that a} rogue model of its Jenkins Utility Safety Testing (AST) plugin had been printed on the Jenkins Market.
The compromise was claimed by the TeamPCP hacker group, which initiated a spree of supply-chain assaults that included the Shai-Hulud campaigns on npm and the Trivy vulnerability scanner breach, ensuing within the supply of credential-stealing malware.
Jenkins is likely one of the most generally used Steady Integration/Steady Deployment (CI/CD) automation options for software program constructing, testing, code scanning, software packaging, and deploying updates to servers.
The Checkmarx AST plugin on the Jenkins Market integrates security scanning into automated pipelines.
“We’re conscious {that a} modified model of the Checkmarx Jenkins AST plugin was printed to the Jenkins Market. We’re within the technique of publishing a brand new model of this plug-in,” Checkmarx alerted within the replace.
That is the third incident in a sequence of supply-chain assaults the applying security testing agency has suffered since late March.
In accordance with offensive security engineer Adnand Khan, TeamPCP gained entry to Checkmarx’s GitHub repositories and backdoored the Jenkins AST plugin to ship credential-stealing malware.
An organization spokesperson confirmed to BleepingComputer that the menace actor obtained credentials to the repositories from the Trivy supply-chain assault in March.
A message the hackers left within the about part reads: “Checkmarx fails to rotate secrets and techniques once more. With love – TeamPCP.”
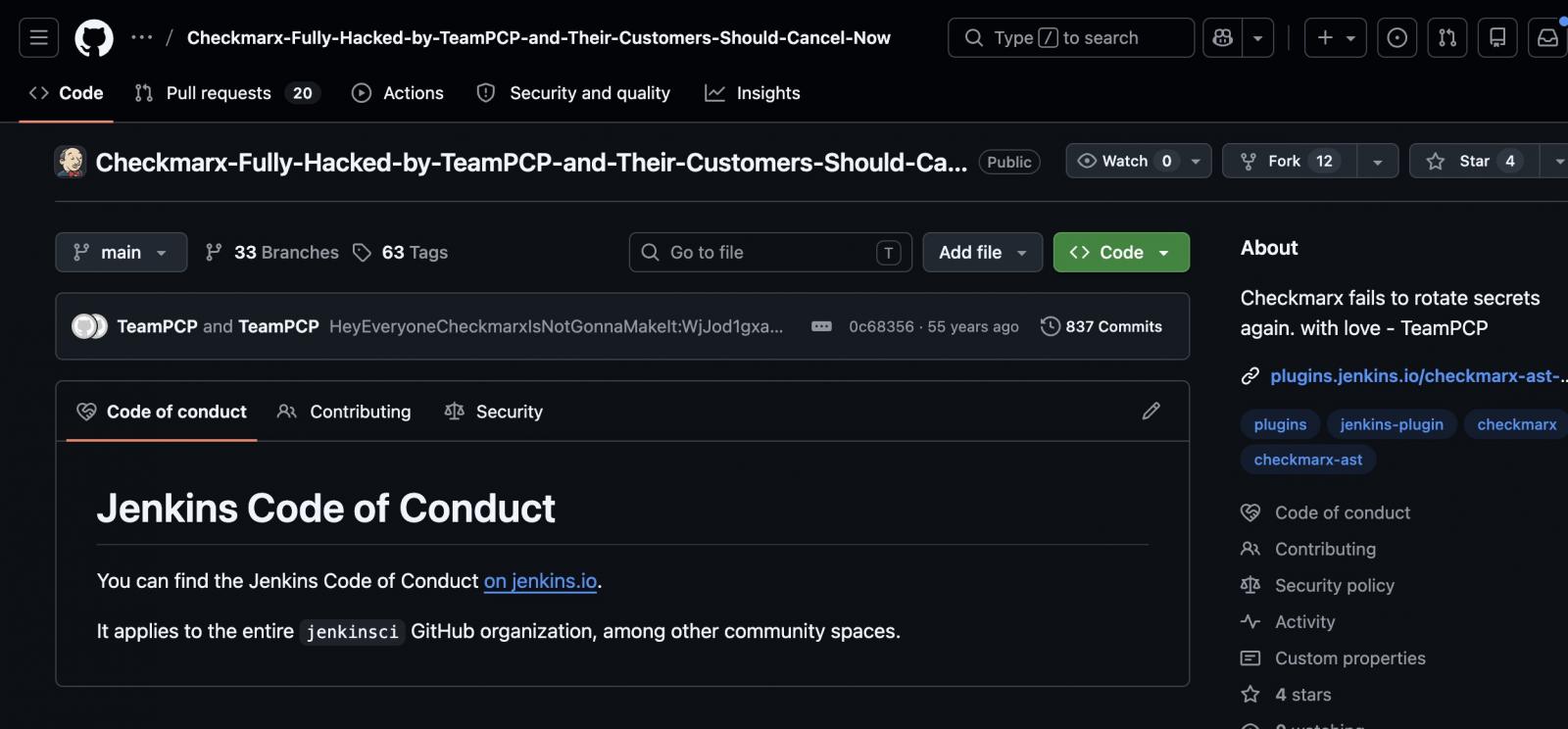
supply: Adnan Khan
“Because of that entry, the attackers have been in a position to work together with Checkmarx’s GitHub atmosphere and subsequently publish malicious code to sure artifacts,” the corporate spokesperson said.
Utilizing credentials stolen within the Trivy assault, the hackers printed modified variations of a number of developer instruments on GitHub, Docker, and VSCode that included info-stealing code.
The menace actor maintained entry for not less than a month after which printed a malicious model of the corporate’s KICS evaluation software on Docker, Open VSX, and VSCode, which harvested knowledge from developer environments.
In late April, the corporate confirmed that the LAPSUS$ menace group leaked knowledge stolen from its non-public GitHub repository.
On Saturday, Could 9, a rogue model (2026.5.09 ) of the Checkmarx Jenkins AST plugin was uploaded to repo.jenkins-ci.org. The replace was outdoors the plugin’s launch pipeline and included malicious code.
Aside from not following the official date type scheme, the malicious plugin lacked a git tag and a GitHub launch.
Checkmarx suggested customers to make sure that they’re utilizing model 2.0.13-829.vc72453fa_1c16 of the plugin printed on December 17, 2025, or an older one.
Though Checkmarx hasn’t shared any particulars about what the rogue Jenkins plugin does on programs, those that have downloaded the malicious model ought to assume that their credentials are compromised, rotate all secrets and techniques, and examine for lateral motion or persistence.
Checkmarx says that its GitHub repositories are remoted from its buyer manufacturing atmosphere, and no buyer knowledge is saved within the GitHub repository.
“Now we have communicated with our clients all through this course of and can proceed to supply related updates as extra info turns into accessible,” the cybersecurity firm stated, including that clients can discover suggestions on the Assist Portal or within the Safety Updates sections.
Checkmarx has printed a set of malicious artifacts that defenders can use as indicator of compromise (IoCs) on their envirronments.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




