UK-based telecommunications firm Colt Know-how Companies confirms that buyer documentation was stolen as Warlock ransomware gang auctions recordsdata.
The British telecommunications and community providers supplier beforehand disclosed it suffered an assault on August 12, however that is the primary time they confirmed information had been stolen.
“A prison group has accessed sure recordsdata from our techniques which will include data associated to our clients and posted the doc titles on the darkish net,” reads an up to date security incident advisory on Colt’s web site.
“We perceive that that is regarding for you.”
“Prospects are in a position to request a listing of filenames posted on the darkish net from the devoted name centre.”
This assertion comes after the Warlock Group started promoting on the Ramp cybercrime discussion board what they declare is 1 million paperwork stolen from Colt. The paperwork are being bought for $200,000 and allegedly include monetary data, community structure information, and buyer data.
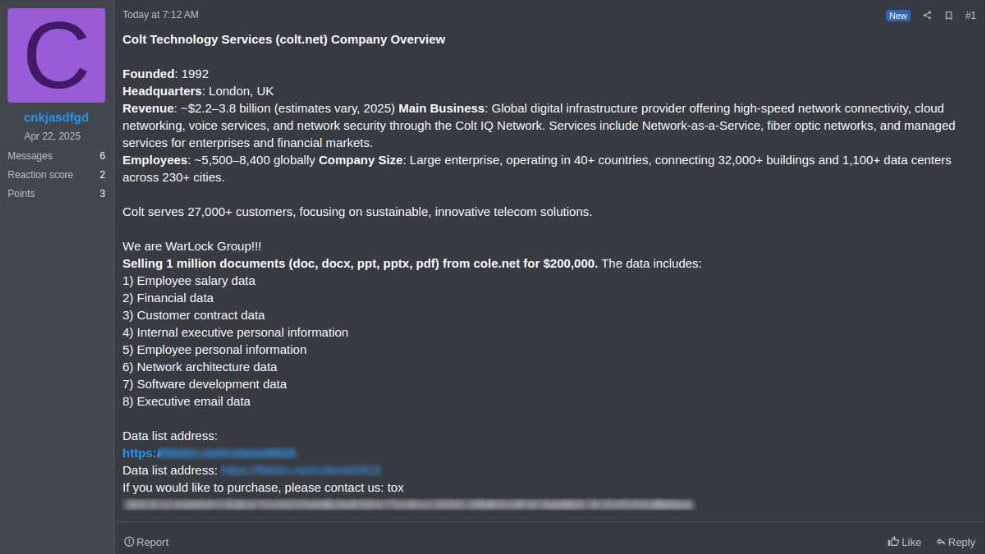
Supply: KELA
BleepingComputer can verify that the Tox ID listed within the discussion board put up matches an ID utilized in earlier variations of the ransomware gang’s ransom notes.
The Warlock Group (aka Storm-2603) is a ransomware gang attributed to Chinese language risk actors who make the most of the leaked LockBit Home windows and Babuk VMware ESXi encryptors in assaults.
When the ransomware gang launched in March 2025, they used LockBit ransomware notes of their assaults, custom-made to incorporate a Tox ID for ransom negotiations.
In June, the ransomware gang branded itself because the “Warlock Group,” with custom-made ransom notes and darkish net negotiation and information leak websites.
Final month, Microsoft reported that the risk actors have been exploiting a SharePoint vulnerability to breach company networks and deploy ransomware.
In negotiations seen by BleepingComputer, the ransomware gang calls for ransom ranging between $450,000 and hundreds of thousands of {dollars}.

46% of environments had passwords cracked, almost doubling from 25% final 12 months.
Get the Picus Blue Report 2025 now for a complete have a look at extra findings on prevention, detection, and information exfiltration developments.




