Cybersecurity researchers have discovered that it is attainable for menace actors to use a widely known utility referred to as command-not-found to suggest their very own rogue packages and compromise methods working Ubuntu working system.
“Whereas ‘command-not-found’ serves as a handy device for suggesting installations for uninstalled instructions, it may be inadvertently manipulated by attackers by the snap repository, resulting in misleading suggestions of malicious packages,” cloud security agency Aqua mentioned in a report shared with The Hacker Information.
Put in by default on Ubuntu methods, command-not-found suggests packages to put in in interactive bash classes when trying to run instructions that aren’t out there. The strategies embody each the Superior Packaging Instrument (APT) and snap packages.
When the device makes use of an inside database (“/var/lib/command-not-found/instructions.db”) to counsel APT packages, it depends on the “advise-snap” command to counsel snaps that present the given command.
Thus, ought to an attacker have the ability to recreation this technique and have their malicious package deal advisable by the command-not-found package deal, it may pave the way in which for software program provide chain assaults.
Aqua mentioned it discovered a possible loophole whereby the alias mechanism could be exploited by the menace actor to probably register the corresponding snap title related to an alias and trick customers into putting in the malicious package deal.
What’s extra, an attacker may declare the snap title associated to an APT package deal and add a malicious snap, which then finally ends up being advised when a consumer varieties within the command on their terminal.

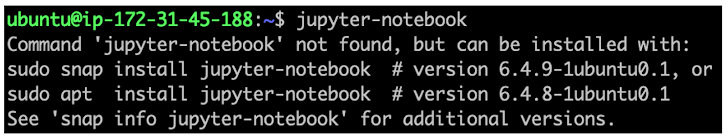
“The maintainers of the ‘jupyter-notebook’ APT package deal had not claimed the corresponding snap title,” Aqua mentioned. “This oversight left a window of alternative for an attacker to assert it and add a malicious snap named ‘jupyter-notebook.'”
To make issues worse, the command-not-found utility suggests the snap package deal above the authentic APT package deal for jupyter-notebook, deceptive customers into putting in the pretend snap package deal.
As many as 26% of the APT package deal instructions are weak to impersonation by malicious actors, Aqua famous, presenting a considerable security threat, as they might be registered below an attacker’s account.
A 3rd class entails typosquatting assaults during which typographical errors made by customers (e.g., ifconfigg as an alternative of ifconfig) are leveraged to counsel bogus snap packages by registering a fraudulent package deal with the title “ifconfigg.”
In such a case, command-not-found “would mistakenly match it to this incorrect command and suggest the malicious snap, bypassing the suggestion for ‘net-tools’ altogether,” Aqua researchers defined.
Describing the abuse of the command-not-found utility to suggest counterfeit packages as a urgent concern, the corporate is urging customers to confirm the supply of a package deal earlier than set up and test the maintainers’ credibility.
Builders of APT and snap packages have additionally been suggested to register the related snap title for his or her instructions to stop them from being misused.
“It stays unsure how extensively these capabilities have been exploited, underscoring the urgency for heightened vigilance and proactive protection methods,” Aqua mentioned.