Researchers have discovered that in roughly 80% of circumstances, spikes in malicious exercise like community reconnaissance, focused scanning, and brute-forcing makes an attempt focusing on edge networking gadgets are a precursor to the disclosure of recent security vulnerabilities (CVEs) inside six weeks.
This has been found by menace monitoring agency GreyNoise, which experiences these occurrences usually are not random, however are somewhat characterised by repeatable and statistically vital patterns.
GreyNoise bases this on knowledge from its ‘World Remark Grid’ (GOG) collected since September 2024, making use of goal statistical thresholds to keep away from results-skewing cherry-picking.
After eradicating noisy, ambiguous, and low-quality knowledge, the agency ended up with 216 occasions that certified as spike occasions, tied to eight enterprise edge distributors.
“Throughout all 216 spike occasions we studied, 50 p.c have been adopted by a brand new CVE inside three weeks, and 80 p.c inside six weeks,” clarify the researchers.
The correlation was notably stronger for Ivanti, SonicWall, Palo Alto Networks, and Fortinet merchandise, and weaker for MikroTik, Citrix, and Cisco. State-sponsored actors have repeatedly focused such programs for preliminary entry and persistence.
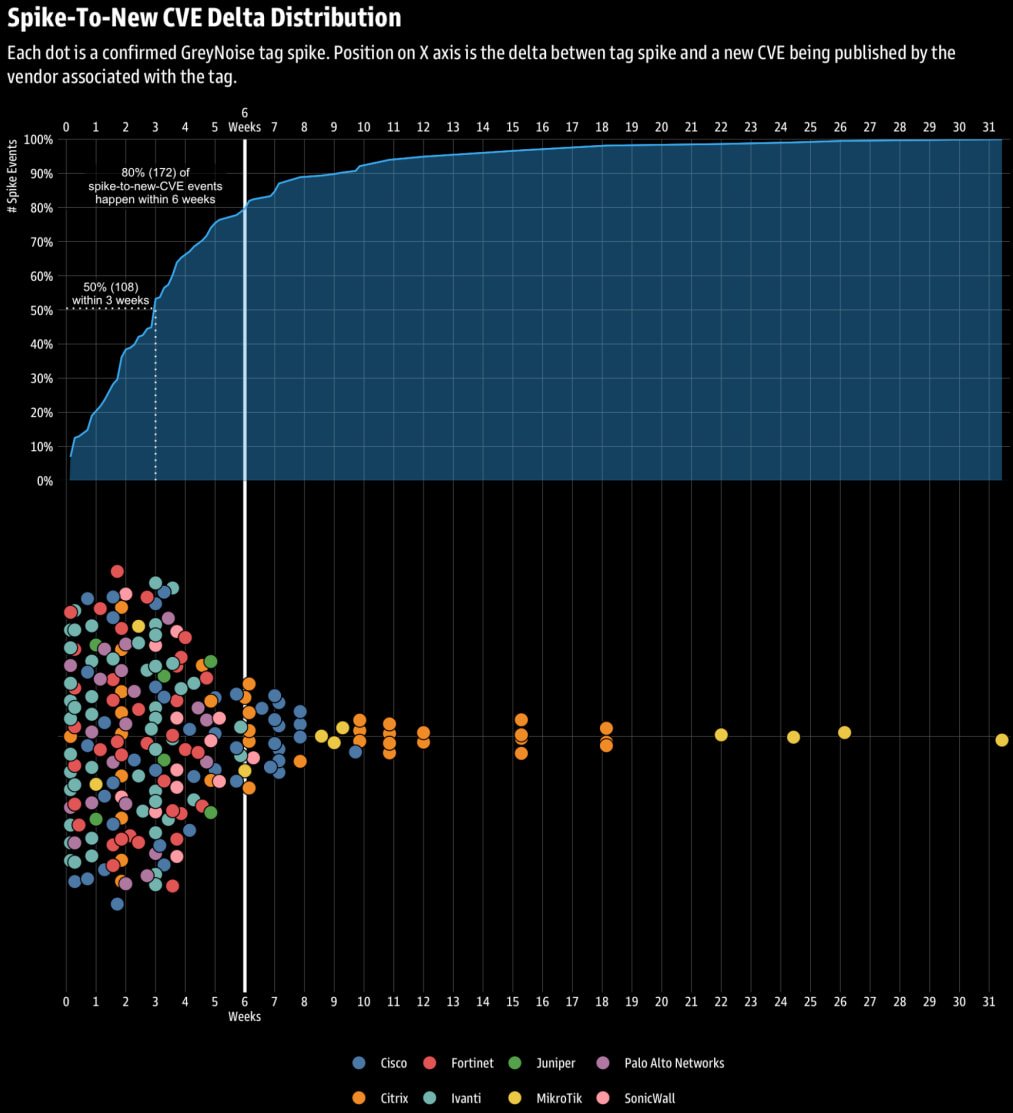
Supply: GreyNoise
GreyNoise notes that within the majority of the circumstances underlying these spikes, the attackers carry out exploit makes an attempt in opposition to older, recognized flaws.
The researchers consider that this both facilitates the invention of recent weaknesses or the invention of internet-exposed endpoints that may be focused within the subsequent section of the assault, which leverages novel exploits.
A “Mine Canary”
Historically, defenders reply after a CVE is revealed, however GreyNoise’s findings present that attacker habits could be a main indicator and a instrument for organizing proactive defenses.
These pre-disclosure spikes give defenders a window to arrange, improve monitoring, and harden programs in opposition to a possible assault, even when a security replace doesn’t defend them they usually aren’t conscious of which system part or perform is definitely focused.
GreyNoise recommends that scanning exercise be intently monitored and origin IPs promptly blocked, as this excludes them from reconnaissance that sometimes results in precise assaults afterward.
The researchers underline that scans for older flaws are to be anticipated in these circumstances, as attackers intention to catalog uncovered belongings. Therefore, these should not be disregarded as failed makes an attempt to breach fully-patched endpoints.
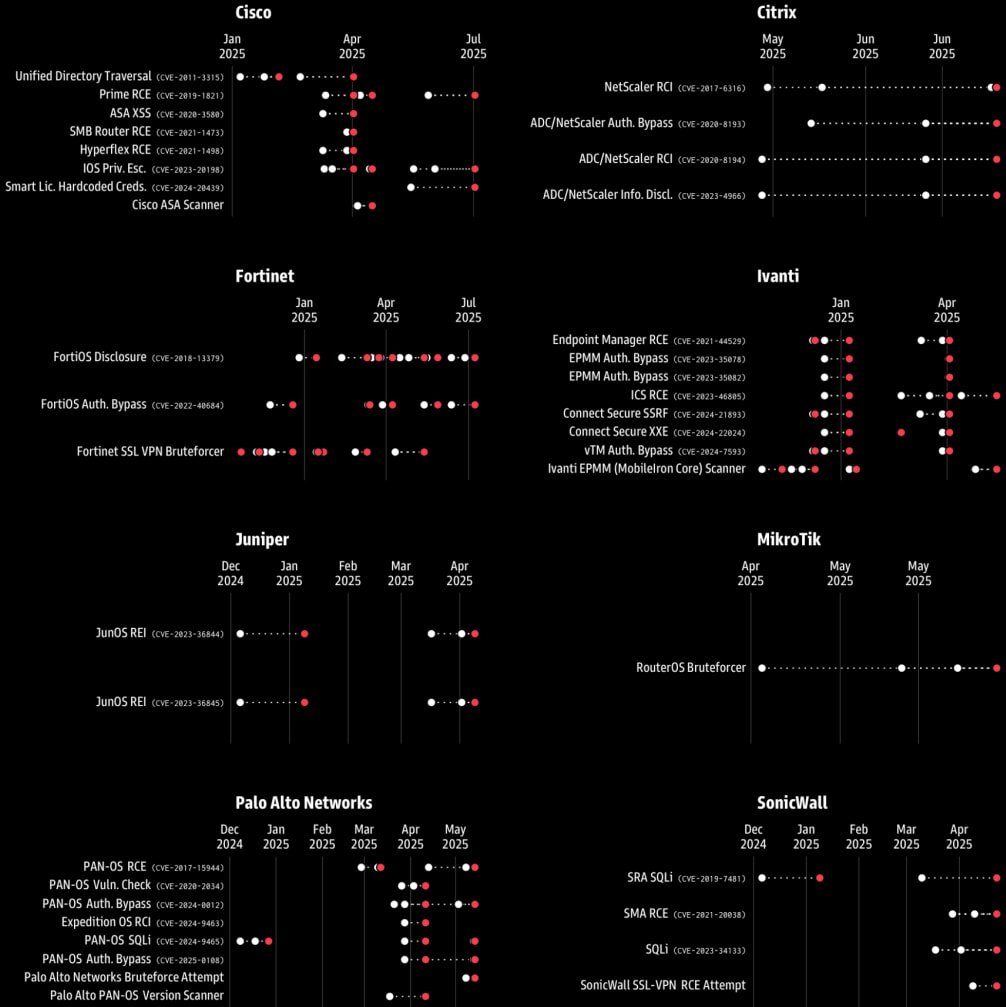
Supply: GreyNoise
On a associated improvement, Google’s Mission Zero introduced that it’s going to start informing the general public {that a} vulnerability has been found inside every week, serving to system admins bolster their defenses whereas distributors work on growing a patch.
Mission Zero will now share the seller/venture and product impacted by the brand new flaw, the invention time, and disclosure deadline (nonetheless at 90 days).
Missing technical particulars, proof-of-concept exploits, or another data that would tip attackers, Google expects this transformation to don’t have any opposed impact on security whereas on the similar time serving to scale back the “patch hole.”

Comprise rising threats in actual time – earlier than they impression your enterprise.
Learn the way cloud detection and response (CDR) provides security groups the sting they want on this sensible, no-nonsense information.




