An extortion group has launched a brand new information leak website to publicly extort dozens of firms impacted by a wave of Salesforce breaches, leaking samples of knowledge stolen within the assaults.
The risk actors chargeable for these assaults declare to be a part of the ShinyHunters, Scattered Spider, and Lapsus$ teams, collectively referring to themselves as “Scattered Lapsus$ Hunters.”
Right this moment, they launched a brand new information leak website containing 39 firms impacted by the assaults. Every entry contains samples of knowledge allegedly stolen from victims’ Salesforce situations, and warns the victims to achieve out to “forestall public disclosure” of their information earlier than the October 10 deadline is reached.
The businesses being extorted on the info leak website embrace well-known manufacturers and organizations, together with FedEx, Disney/Hulu, Residence Depot, Marriott, Google, Cisco, Toyota, Hole, McDonald’s, Walgreens, Instacart, Cartier, Adidas, Sake Fifth Avenue, Air France & KLM, Transunion, HBO MAX, UPS, Chanel, and IKEA.
“All of them have been contacted way back, they noticed the e-mail as a result of I noticed them obtain the samples a number of instances. Most of them selected to not disclose and ignore,” ShinyHunters advised BleepingComputer.
“We extremely advise you proceed into the fitting resolution, your organisation can forestall the discharge of this information, regain management over the scenario and all operations stay secure as at all times. We extremely suggest a decision-maker to get entangled as we’re presenting a transparent and mutually helpful alternative to resolve this matter,” they warned on the leak website.
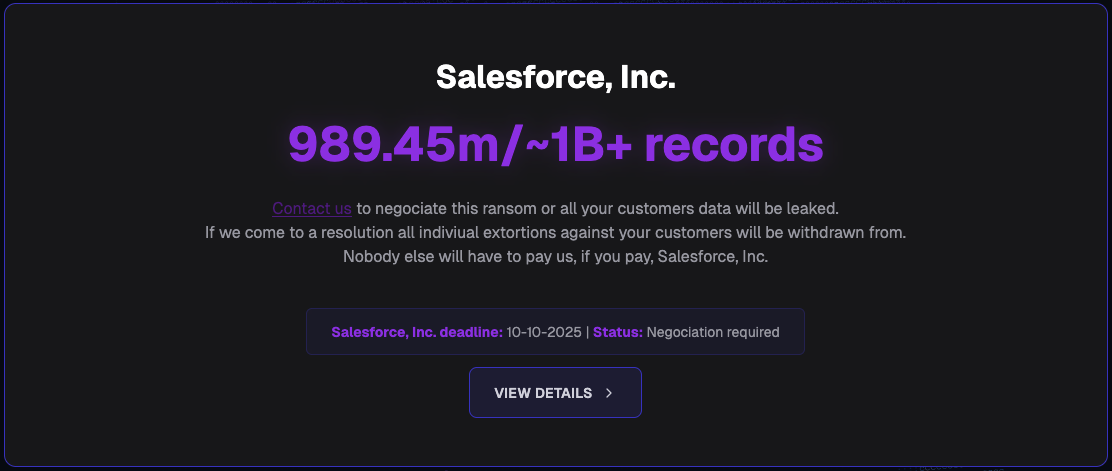
The risk actors additionally added a separate entry requesting that Salesforce pay a ransom to stop all impacted clients’ information (roughly 1 billion data containing private data) from being leaked.
“Must you comply, we are going to withdraw from any lively or pending negotiation indiviually out of your clients. Your clients won’t be attacked once more nor will they face a ransom from us once more, must you pay,” they added.
The extortion group additionally threatened the corporate, stating that it could assist regulation companies pursue civil and industrial lawsuits in opposition to Salesforce following the data breaches and warned that the corporate had additionally failed to guard clients’ information as required by the European Basic Data Safety Regulation (GDPR).
Scattered Lapsus$ Hunters have been focusing on Salesforce clients with voice phishing assaults for the reason that starting of the 12 months, resulting in breaches that have impacted firms resembling Google, Cisco, Qantas, Adidas, Allianz Life, Farmers Insurance coverage, Workday, in addition to LVMH subsidiaries, together with Dior, Louis Vuitton, and Tiffany & Co.
In these assaults, the risk actors tricked staff into linking a malicious OAuth app to their firm’s Salesforce occasion. As soon as related, the attackers stole firm databases and used the info to extort victims by way of e mail.
These extortion emails had been signed by ShinyHunters, a infamous extortion group linked to a protracted string of high-profile breaches in recent times, together with the Snowflake assaults and people in opposition to AT&T and PowerSchool.
ShinyHunters additionally claimed to have used stolen OAuth tokens for Salesloft’s Drift AI chat integration with Salesforce to steal delicate data, together with passwords, AWS entry keys, and Snowflake tokens, from clients’ Salesforce situations.
These assaults had been tracked by Mandiant below a separate risk cluster named “UNC6395” as they’ve been unable to formally hyperlink the breaches to this group.
On a Telegram channel related to the extortion group, the risk actors declare that they may start extorting firms affected by the Salesloft Drift assaults on a separate information leak website launching on October tenth.
ShinyHunters beforehand advised BleepingComputer that the Salesloft information theft assaults impacted roughly 760 firms and resulted in the theft of 1.5 billion Salesforce data.
The Salesloft assaults are identified to have impacted Google, Palo Alto Networks, CyberArk, Cloudflare, Rubrik, Elastic, BeyondTrust, Proofpoint, JFrog, Zscaler, Tenable, Nutanix, Qualys, Cato Networks, and plenty of extra.

Be a part of the Breach and Attack Simulation Summit and expertise the way forward for security validation. Hear from prime specialists and see how AI-powered BAS is remodeling breach and assault simulation.
Do not miss the occasion that may form the way forward for your security technique




