The ShinyHunters extortion gang has claimed accountability for breaching Dutch telecommunications supplier Odido and stealing hundreds of thousands of person data from its compromised programs.
Odido is without doubt one of the largest telecommunications firms within the Netherlands and affords cell, broadband, and tv providers to hundreds of thousands of shoppers nationwide.
The corporate disclosed the breach on February 12, revealing that attackers downloaded the non-public information of a lot of its customers after having access to its buyer contact system on February 7. Nevertheless, Odido added that no Mijn Odido passwords, name particulars, location, information, billing information, or scans of id paperwork have been uncovered in the course of the incident.

In response to the telecom agency, the uncovered data varies per buyer and should embody a mix of full title, tackle and metropolis of residence, cell quantity, buyer quantity, e mail tackle, IBAN (checking account quantity), date of start, and a few identification particulars (passport or driver’s license quantity and validity).
It additionally advised native media on the time that the data breach affected 6.2 million clients and that the menace actors reached out to say they’d stolen hundreds of thousands of person data.
After discovering the incident, Odido has reported the breach to the Dutch Data Safety Authority, blocked the attackers’ entry to its programs, and employed exterior cybersecurity specialists to help with incident response and mitigation.
An Odido spokesperson did not present additional data on the incident when requested about which menace group was behind the assault and whether or not they demanded a ransom “as a result of ongoing investigations.”
Whereas Odido has but to attribute the assault, the ShinyHunters extortion gang has now added the corporate to its darkish internet leak web site, claiming they’ve stolen practically 21 million data containing information the corporate already revealed as uncovered within the breach.
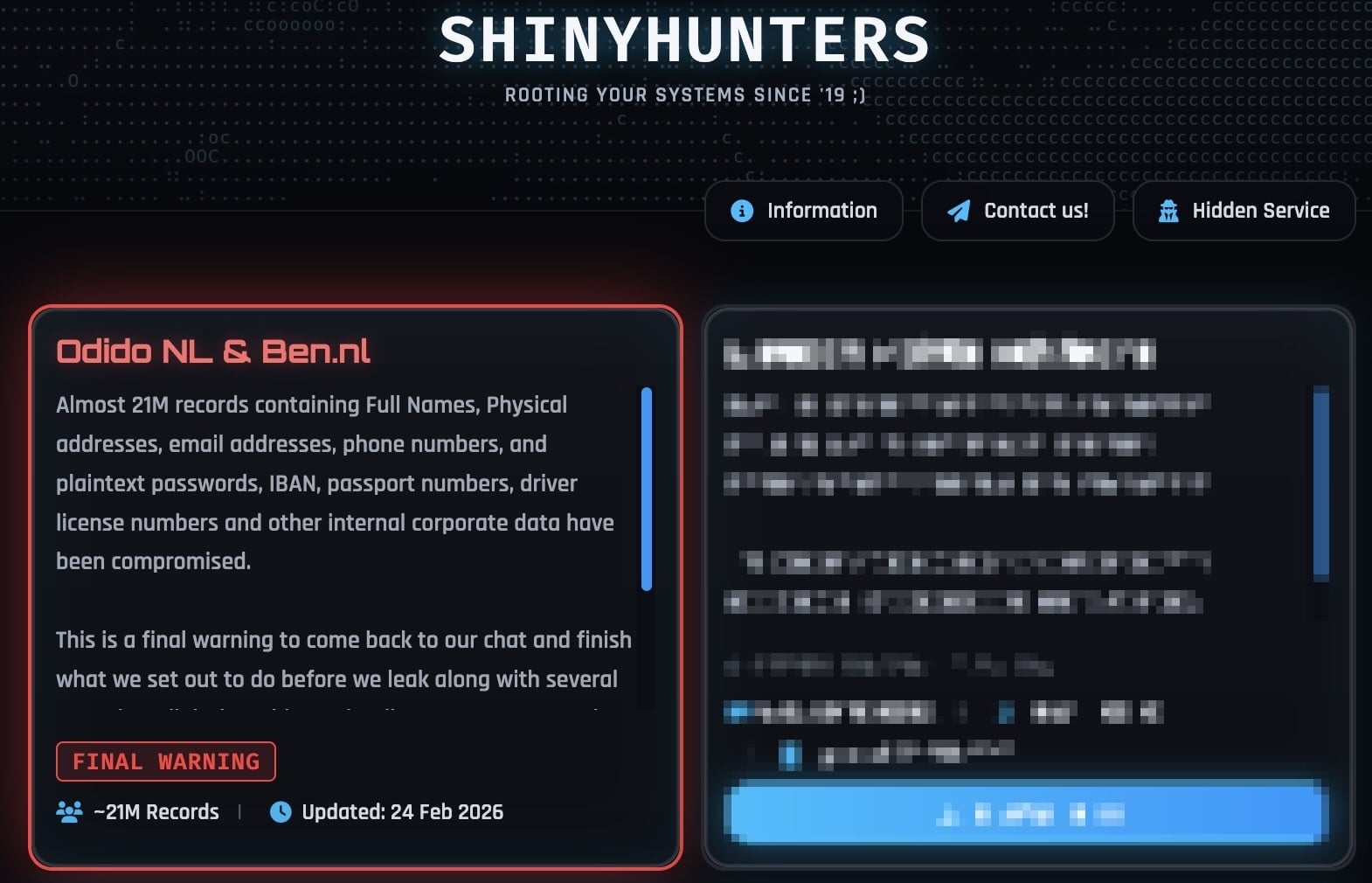
ShinyHunters additionally advised BleepingComputer on Monday that the stolen information additionally accommodates inner company information and plaintext passwords.
“It is a last warning to come back again to our chat and end what we got down to do earlier than we leak together with a number of annoying (digital) issues that’ll come your means,” the extortion gang says on the leak web site. “Make the fitting choice, do not be the following headline. You understand the place to search out us.”
Nevertheless, an Odido spokesperson denied their claims in a press release to BleepingComputer, reiterating that “no passwords, name particulars, social security numbers, or billing information are concerned.”
In current weeks, ShinyHunters has claimed accountability for a wave of different security breaches, together with Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and on-line courting big Match Group (which owns the Tinder, Hinge, Meetic, Match.com, and OkCupid courting platforms).
A few of their victims had their programs compromised in voice phishing (vishing) assaults focusing on single sign-on (SSO) accounts at Google, Microsoft, and Okta, the place the menace actors name staff whereas impersonating IT assist workers and trick them into coming into credentials and multi-factor authentication (MFA) codes on phishing websites that mimic their firms’ login portals.
As BleepingComputer first reported, the ShinyHunters group has additionally not too long ago adopted gadget code vishing, abusing the OAuth 2.0 gadget authorization grant move to acquire Microsoft Entra authentication tokens.
After stealing their targets’ credentials and auth codes, the menace actors hijack the victims’ SSO accounts to breach linked enterprise providers like Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and lots of others.

Fashionable IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, find out how your group can cut back hidden handbook delays, enhance reliability by means of automated response, and construct and scale clever workflows on prime of instruments you already use.




