The ShinyHunters hacking group claims it breached the programs of cybersecurity agency Resecurity and stole inner information, whereas Resecurity says the attackers solely accessed a intentionally deployed honeypot containing pretend info used to observe their exercise.
Right now, the risk actors printed screenshots on Telegram of the alleged breach, claiming to have stolen worker information, inner communications, risk intelligence stories, and shopper info.
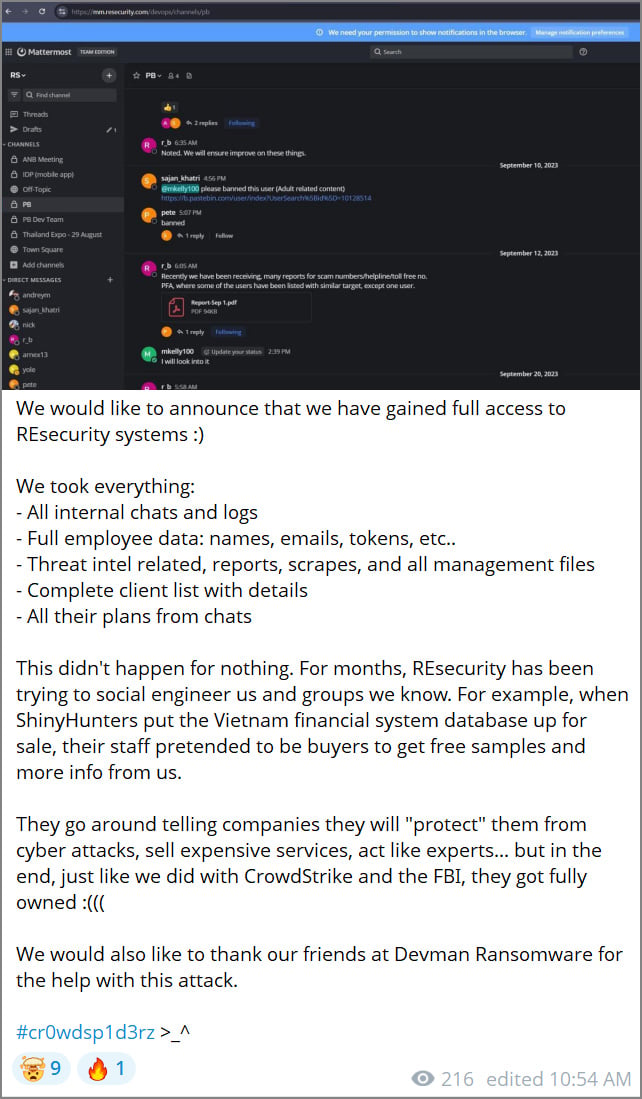
“We wish to announce that we have now gained full entry to REsecurity programs,” the group wrote on Telegram, claiming to have stolen “all inner chats and logs”, “full worker information”, “risk intel associated stories”, and a “full shopper listing with particulars.”

Supply: BleepingComputer
As proof of their claims, the risk actors printed screenshots they allege had been stolen from Resecurity, together with what seems to be a Mattermost collaboration occasion displaying communications between Resecurity staff and Pastebin personnel concerning malicious content material hosted on the text-sharing platform.
The risk actors, who discuss with themselves as “Scattered Lapsus$ Hunters” because of the alleged overlap between ShinyHunters, Lapsus$, and Scattered Spider risk actors, mentioned the assault was retaliation for what they declare are ongoing makes an attempt by Resecurity to socially engineer the group and study extra about its operations.
ShinyHunters says Resecurity staff pretended to be patrons throughout the sale of an alleged Vietnam monetary system database, looking for free samples and extra info.
If in case you have any info concerning this incident or different undisclosed assaults, you’ll be able to contact us confidentially by way of Sign at 646-961-3731 or at suggestions@bleepingcomputer.com.
Resecurity says it was a honeypot
Resecurity disputes ShinyHunters’ claims, stating that the allegedly breached programs should not a part of its authentic manufacturing infrastructure however had been as an alternative a honeypot designed to draw and monitor the risk actors.
After BleepingComputer contacted Resecurity concerning the declare, they shared a report printed on December 24, the place the corporate says it first detected a risk actor probing their publicly uncovered programs on November 21, 2025.
The corporate says its DFIR workforce recognized reconnaissance indicators early and logged a number of IP addresses linked to the actor, together with these originating from Egypt and Mullvad VPN companies.
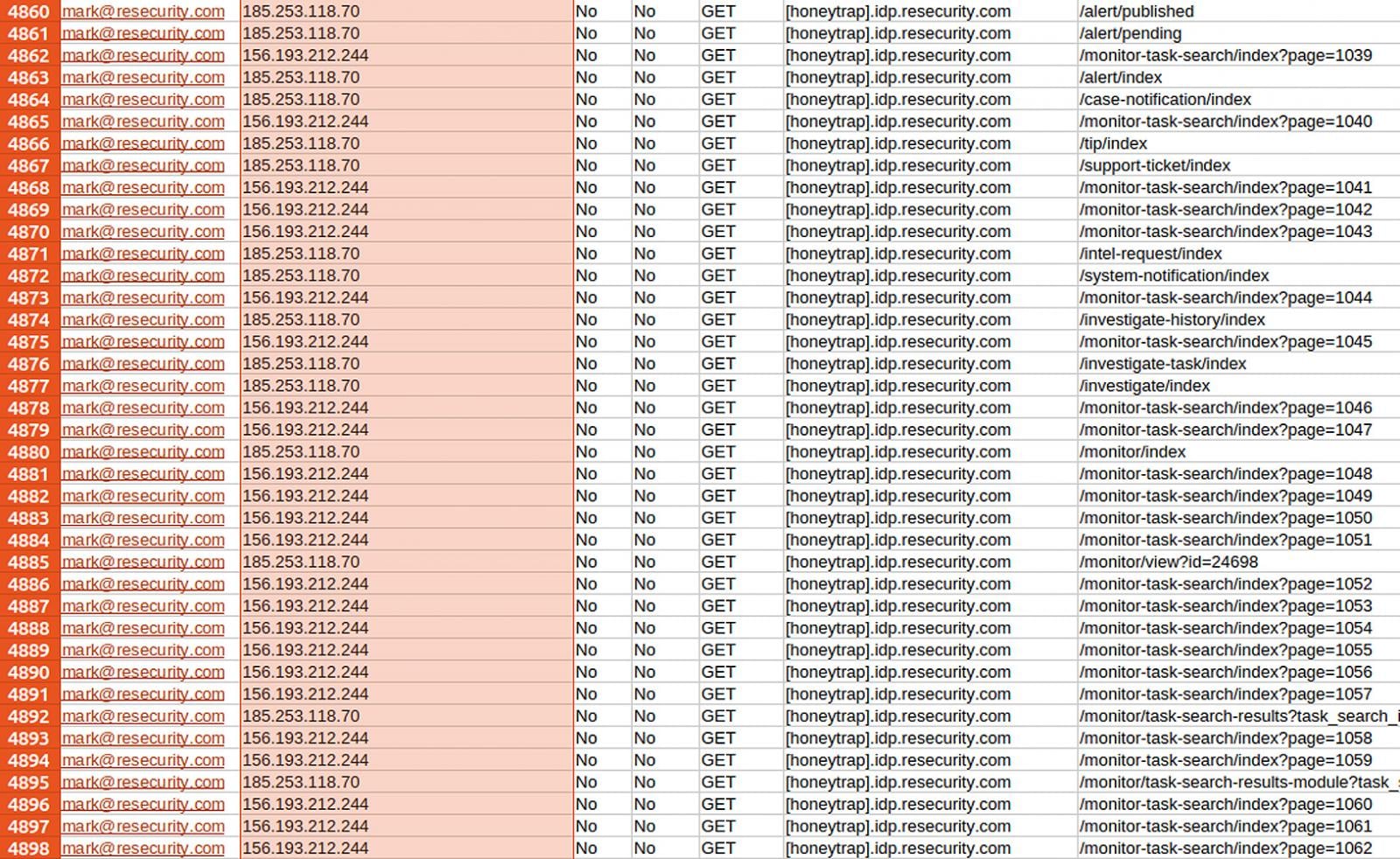
Resecurity mentioned it responded by deploying a “honeypot” account inside an remoted atmosphere that allowed the risk actor to log in and work together with programs containing pretend worker, buyer, and fee information whereas it was being monitored by the researchers.
A honeypot is a intentionally uncovered, monitored system or account designed to lure attackers, permitting them to be noticed and analyzed and to assemble intelligence on their exercise with out risking actual information or infrastructure.
The corporate says it populated the honeypot with artificial datasets designed to intently resemble real-world enterprise information. These included greater than 28,000 artificial shopper information and over 190,000 artificial fee transaction information, each generated from Stripe’s official API format.
In keeping with Resecurity, the risk actor started making an attempt to automate information exfiltration in December, producing greater than 188,000 requests between December 12 and December 24 whereas utilizing massive numbers of residential proxy IP addresses.
Throughout this exercise, the corporate says it collected telemetry on the attacker’s ways, methods, and infrastructure.
Supply: Resecurity
Resecurity claims that the attacker briefly uncovered confirmed IP addresses on a number of events as a result of proxy connection failures, and that the intel was reported to regulation enforcement.
After observing extra exercise, Resecurity says it added additional pretend datasets to review the attacker’s habits, which led to extra OPSEC failures and helped slim down the risk actor’s infrastructure.
The agency says it later recognized servers used to automate the assault by way of residential proxies and shared the intelligence with regulation enforcement as effectively.
“As soon as the actor was positioned utilizing out there community intelligence and timestamps, a overseas regulation enforcement group, a accomplice of Resecurity, issued a subpoena request concerning the risk actor,” says Resecurity.
On the time of writing, ShinyHunters has not supplied any additional proof, solely issuing a brand new Telegram submit stating that extra info will probably be coming quickly.
“Good harm management Resecurity. Extra info coming quickly!,” posted the risk actors.

Whether or not you are cleansing up previous keys or setting guardrails for AI-generated code, this information helps your workforce construct securely from the beginning.
Get the cheat sheet and take the guesswork out of secrets and techniques administration.




