Russian organizations are on the receiving finish of cyber assaults which were discovered to ship a Home windows model of a malware known as Decoy Canine.
Cybersecurity firm Constructive Applied sciences is monitoring the exercise cluster underneath the identify Operation Lahat, attributing it to a sophisticated persistent risk (APT) group known as HellHounds.
“The Hellhounds group compromises organizations they choose and acquire a foothold on their networks, remaining undetected for years,” security researchers Aleksandr Grigorian and Stanislav Pyzhov mentioned. “In doing so, the group leverages major compromise vectors, from weak internet providers to trusted relationships.”

HellHounds was first documented by the agency in late November 2023 following the compromise of an unnamed energy firm with the Decoy Canine trojan. It is confirmed to have compromised 48 victims in Russia up to now, together with IT corporations, governments, house trade corporations, and telecom suppliers.
There’s proof indicating that the risk actor has been concentrating on Russian corporations since no less than 2021, with the event of the malware underway way back to November 2019.
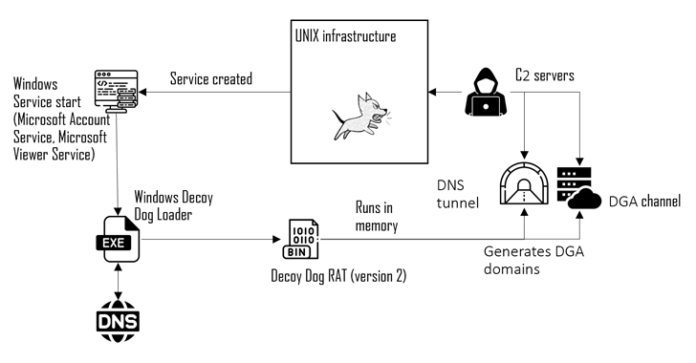
Particulars about Decoy Canine, a customized variant of the open-source Pupy RAT, emerged in April 2023, when Infoblox uncovered the malware’s use of DNS tunneling for communications with its command-and-control (C2) server to remotely management contaminated hosts.
A notable characteristic of the malware is its capacity to maneuver victims from one controller to a different, permitting the risk actors to keep up communication with compromised machines and stay hidden for prolonged intervals of time.
Attacks involving the subtle toolkit have been primarily confined to Russia and Jap Europe, to not point out completely single out Linux methods, though Infoblox hinted at the potential for a Home windows model.
“References to Home windows within the code trace towards the existence of an up to date Home windows shopper that features the brand new Decoy Canine capabilities, though all the present samples are concentrating on Linux,” Infoblox famous again in July 2023.
The most recent findings from Constructive Applied sciences all however verify the presence of an similar model of Decoy Canine for Home windows, which is delivered to mission-critical hosts via a loader that employs devoted infrastructure to get the important thing for decrypting the payload.
Additional evaluation has uncovered HellHounds’ use of a modified model of one other open-source program often called 3snake to acquire credentials on hosts operating Linux.

Constructive Applied sciences mentioned that in no less than two incidents, the adversary managed to realize preliminary entry to victims’ infrastructure by way of a contractor utilizing compromised Safe Shell (SSH) login credentials.
“The attackers have lengthy been capable of preserve their presence inside essential organizations positioned in Russia,” the researchers mentioned.
“Though nearly all the Hellhounds toolkit is predicated on open-source tasks, the attackers have completed a reasonably good job modifying it to bypass malware defenses and guarantee extended covert presence inside compromised organizations.”