Between crossovers – Do menace actors play soiled or determined?
In our dataset of over 11,000 sufferer organizations which have skilled a Cyber Extortion / Ransomware assault, we seen that some victims re-occur. Consequently, the query arises why we observe a re-victimization and whether or not or not that is an precise second assault, an affiliate crossover (that means an affiliate has gone to a different Cyber Extortion operation with the identical sufferer) or stolen information that has been travelling and re-(mis-)used. Both method, for the victims neither is sweet information.
However very first thing’s first, let’s discover the present menace panorama, dive into one in every of our most up-to-date analysis focuses on the dynamics of this ecosystem; after which discover our dataset on Legislation Enforcement actions on this area. May the re-occurrence that we observe be foul play by menace actors and thus present how desperately they’re attempting to regain the belief of their co-offenders after disruption efforts by Legislation Enforcement? Or are they only enjoying soiled after receiving no funds from the sufferer?
What we’re observing within the Cy-X menace panorama
Cyber Extortion (Cy-X) or Ransomware, because it’s extra generally recognized, is a subject that has garnered plenty of consideration over the previous three to 4 years. Orange Cyberdefense has lined this menace extensively since 2020.
Within the newest annual security report, the Safety Navigator 2024 (SN24), analysis confirmed a rise of 46% between 2022 and 2023 (interval of This fall 2022 to Q3 2023). Updating our dataset, we discover that the precise enhance is even greater with just below 51% enhance. The up to date quantity is as a result of dynamic nature of the dataset; the ecosystem constantly adjustments and so we solely turned conscious of sure leak websites and their victims as soon as the analysis interval had concluded.
Sadly, this simply additional compounds the truth. Predicting whether or not this stage of enhance will probably be maintained is troublesome. Cy-X could have reached a saturation level, the place we’d see the Cy-X menace persevering with on the 2023 ranges. However, if we do comply with the sufferer depend patterns of the final years (decrease numbers to start with of the yr, rising all year long), which might have the other impact, offering us with an ever-growing sufferer depend as soon as extra. Nevertheless, we consider that the Cy-X sufferer depend ranges will stay regular for now, and if we’re lucky, it might chance level to a lower in extortion victims. Nonetheless, we’re a good distance off from claiming victory.

Six months have handed for the reason that finish of the SN24 Cy-X dataset was mentioned within the report, and loads has occurred throughout that point. The whole variety of victims for This fall 2023 and Q1 2024 tallies to 2,141 – almost all of the victims recorded for the entire of 2022, which was 2,220 victims. The amount of this sufferer depend is exceptional on condition that two of probably the most lively Cy-X teams had been (tried) to be disrupted throughout this time. Legislation Enforcement (LE) aimed to disrupt ALPHV in December 2023, the place they confirmed resistance by “unseizing” themselves simply days after. LE then took down LockBit’s infrastructure in February 2024, nonetheless, this solely meant just a few days’ downtime for LockBit since additionally they managed to get again on-line just a few days after the preliminary takedown. Despite the fact that the 2 Cy-X operations appeared very resistant on the time, ALPHV (BlackCat) went offline at first of March 2024, “exiting” the sport with almost certainly a so-called exit rip-off.
Efforts to disrupt this risky ecosystem – challenges as a result of brief lifespans of Cy-X manufacturers
Irrespective of its impact, earlier LE actions render vital insights into Cy-X operations. One instance is the darkish variety of the Cy-X crime, which is the variety of victims we do not find out about as a result of they don’t seem to be uncovered on the leak websites that we monitor. Understanding the darkish quantity would assist us full the image of the present Cy-X menace. Thus, the entire image would come with the precise variety of victims that embrace our partial view of the victims that had been uncovered on the leak websites (our information) and the sufferer organizations we are going to by no means find out about (the darkish quantity). The takedown of Hive in 2023 revealed the next variety of victims than what we had recorded from their information leak website, the place the precise quantity was 5 to six instances greater. If we use the multiplier of six with the recorded sufferer depend – 11,244 – from the beginning of January 2020 to finish of March 2024, then the true sufferer depend could possibly be as excessive as 67,000 victims throughout all Cy-X teams.
Cl0p, who’s probably the most persistent menace actor in our dataset, was very busy throughout 2023 and was answerable for 11% of all victims. Nevertheless, for the final six months since that evaluation solely 7 victims had been noticed on the Cy-X group’s information leak website. Cl0p has flickered up previously, mass exploiting vulnerabilities, solely to drag again into the shadows, therefore this would possibly simply be Cl0p’s modus operandi.
Safety Navigator 2024 is Right here – Obtain Now
The newly launched Safety Navigator 2024 provides essential insights into present digital threats, documenting 129,395 incidents and 25,076 confirmed breaches. Greater than only a report, it serves as a information to navigating a safer digital panorama.
What’s Inside?#
- 📈 In-Depth Evaluation: Discover traits, assault patterns, and predictions. Be taught from case research in CyberSOC and Pentesting.
- 🔮 Future-Prepared: Equip your self with our security predictions and analysis abstract.
- 👁️ Actual-Time Data: From Darkish Web surveillance to industry-specific statistics.
Keep one step forward in cybersecurity. Your important information awaits!
🔗 Get Your Copy Now
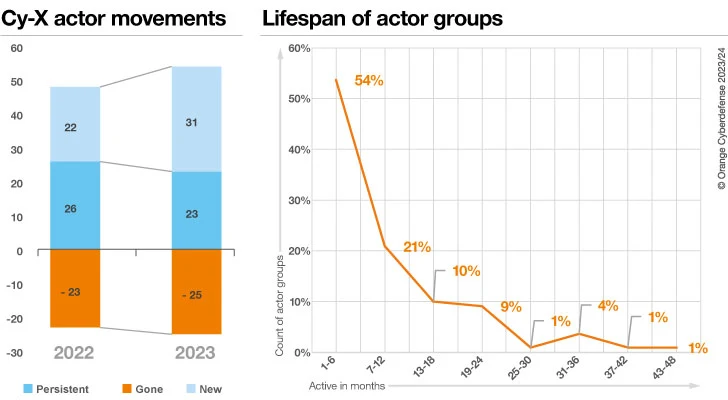
The whole variety of lively Cy-X teams fluctuates over time, and sure teams persist longer than others. The Safety Navigator 2024 report addressed this query by analyzing the year-on-year adjustments. Total, 2023 did see a internet enhance within the variety of lively Cy-X teams in contrast with 2022. Typically, it is a very risky ecosystem with a variety of motion in it. Our analysis discovered that 54% of Cy-X ‘manufacturers’ disappear after 1 to six months of operation. There have been fewer Cy-X teams carried over to 2023, however the enhance within the variety of new Cy-X teams resulted in a internet acquire in exercise. Additional affirmation of the ephemeral nature of those teams. Mockingly, LockBit3 and ALPHV had been listed underneath the grouping of “Persistent” for 2023.
This analysis was carried out as a part of the examination of the effectiveness in defending towards Cy-X. LE and authorities businesses from throughout the globe are working arduous at eliminating Cyber Extortion as it’s actually a worldwide downside. Within the final two and a half years we’ve seen a gradual enhance in LE exercise, recording 169 actions combating cybercrime.
Of all documented LE actions, we noticed Cyber Extortion addressed probably the most. 14% of all actions had been attributed to be associated to the crime of Cyber Extortion, adopted by Hacking and Fraud with 11% every respectively. Crypto-related crimes claimed a share of 9%. Virtually half of LE actions concerned arrests and the sentencing of people or teams.

In our newest Safety Navigator report, we wrote that “in 2023, we particularly famous elevated efforts to take down or disrupt the infrastructure and internet hosting providers menace actors (mis-)used.” With our up to date dataset from the final 6 months, we do see a good greater proportion of the class “Legislation Enforcement disrupts”. Right here, we collected actions corresponding to bulletins on kicking off worldwide taskforces to fight Ransomware, LE tricking menace actors in offering them decryption keys, seizing infrastructure, infiltrating cybercrime markets, and so forth. Whereas we’ve beforehand argued whether or not the actions that we do see executed most steadily, e.g. arrest and seizures won’t be as efficient, the 2 newest LE actions have been very fascinating to comply with.
In ALPHV’s case, who in first response appeared very resilient towards the LE’s efforts to disrupt it, has fled the scene and (almost certainly) carried out an exit rip-off. This could enormously undermine “the belief” throughout the Ransomware-as-a-Service (RaaS) ecosystem, there could possibly be a short-term lower within the variety of victims as associates and different actors assess their dangers. On the similar time, there’s a void to fill, and traditionally it doesn’t take lengthy for a brand new (re-)model to fill this hole.
Just like ALPHV, LockBit has claimed to have survived the preliminary takedown, however on the earth of Cyber Extortion, status is all the things. Would associates proceed to do enterprise with the “revived” LockBit not surprise if that could be a LE honeypot?
Re-victimization of Cy-X victims in type of desperation or affiliate crossovers
We all know by now that the cybercrime ecosystem is a posh one, together with many alternative kind of actors, roles and actions. That is very true for the kind of cybercrime we’re monitoring – Cyber Extortion. Over the previous decade, the ecosystem of Cybercrime-as-a-Service (CaaS) has actually advanced and added a number of challenges to watch this crime. One such problem is that not one single menace actor executes one assault from starting to finish (the total assault chain).

As we see within the graph above, many alternative roles play an element in a Cy-X ecosystem, most notably the associates aka ‘Affiliate Ransomware Operator’. Associates are a essential a part of the Cyber Extortion ecosystem as they allow the size and attain of those cyber-attacks. This construction additionally provides a layer of separation between the Ransomware creators (Malware Creator) and the attackers (Affiliate), which might present a level of authorized and operational manoeuvrability for the builders. The affiliate mannequin has contributed to the proliferation of Ransomware, making it a major cybersecurity menace at the moment. The character of those associations doesn’t lend itself to the peace of mind of exclusivity. In some circumstances, plainly sufferer information propagates via the cybercrime ecosystem in methods that aren’t at all times clear.
When analyzing the sufferer listings on Cy-X information leak websites, we observe the re-appearance of victims. That is nothing new, we’ve been observing this phenomenon since 2020. However we lastly have a sufficiently big dataset to make an evaluation on the sightings of re-occurrences to research whether or not these are certainly re-victimizations or different dynamics of the ecosystem that even the ecosystem itself shouldn’t be conscious of. We discover, for instance, that some victims are listed months or years aside, whereas others are reposted inside days or even weeks. We don’t obtain the stolen information and study the content material of the listings as that is an moral concern of ours the place we don’t need to obtain and retailer stolen sufferer information. Therefore, we base our observations on matching the sufferer names.
Certainly one of our most pressing questions when doable re-victimization is why we see some victims re-appearing.
We have now some simplified hypotheses about it:
- One other cyber-attack: An precise re-victimization and thus a second spherical of Cyber Extortion / cyber-attack towards the identical sufferer has occurred. Both via doubtlessly utilizing the identical level of entry or backdoor; or fully unrelated to the primary incidence.
- Re-use of entry or information: The sufferer information has ‘travelled’ (leaked or offered to the underground) and is getting used as leverage to attempt to extort the sufferer as soon as extra. Or the entry has been offered to totally different consumers. Nonetheless, information or entry is being re-used.
- Affiliate crossover: An affiliate has reused sufferer information between totally different Cy-X operations.
The final speculation would possibly present how financially pushed menace actors are and the way determined they may have turn out to be. We’re certain that there is likely to be different variations of our hypotheses, however we needed to maintain it so simple as doable for the next evaluation. We needed to discover whether or not we see patterns of re-victimizations between actors. We discovered over 100 occurrences the place victims had been re-posted, both to the identical or one other group’s leak website.
We created a community graph and added some color coding to the nodes. The inexperienced nodes symbolize actors who had been the second to put up a few explicit sufferer. They spotlight the re-victimization. The blue nodes symbolize actors that act because the origin or first poster of a sufferer. When a Cy-X actor has been each, a first-time poster and second time poster, the node is by default inexperienced. The arrows are a further indicator. Taking a look at a directed community graph of sufferer appearances we will see the path of the re-victimization. Some Cy-X actors with round references repost victims on their very own information leak website. The evaluation beneath is an summary from our present analysis, we’re planning to publish a extra in depth evaluation in our upcoming Cy-Xplorer, our annual Ransomware report.
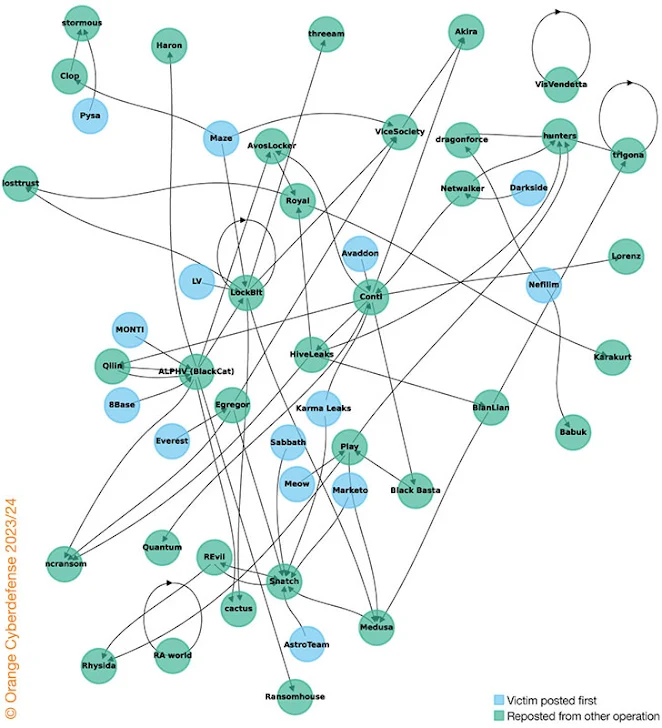
As may be seen above within the community graph, a number of clusters catch one’s eye. The Snatch group for instance demonstrates re-victimization exercise by constantly re-posting victims from different Cy-X operations corresponding to from AstroTeam, Meow, Sabbath, Karma Leaks, cactus, Quantum, Egregor and Marketo. Please keep in mind, re-victimization refers back to the phenomenon the place a sufferer of a crime experiences further hurt or victimization sooner or later. In our consideration that signifies that victims expertise the re-occurrence of for instance unauthorized entry and/or information exfiltration and/or information theft and/or extortion and/or encryption and/or harm to status, and/or monetary loss and psychological hurt and so forth.
Within the three hypotheses, the sufferer will probably be victimized as soon as extra, experiencing one, a number of or all the harms simply listed. This isn’t in regards to the technical sophistication of the assault itself however by purely being listed as soon as once more on a darkweb leak website, the sufferer group is uncovered once more to a number of extreme types of hurt.
If we proceed learning the graph, we see one other cluster, ALPHV’s, the place we see that ALPHV re-posted victims from MONTI, 8Base and Qilin (within the latter the sufferer group was posted in the identical day at each leak websites, ALPHV and Qilin). And on the similar time, sufferer organizations that appeared first on ALPHV’s leak website, had been re-posted by varied different operations corresponding to AvosLocker, LockBit, Ransomhouse, incransom, Haron, cactus, and so forth. The arrows assist to point directionality of the connection, e.g. who acted first. Different clusters present very related patterns that we’ll not dive into on this exploration. Nonetheless, the community graph and the above (partial) evaluation present us the relationships and patterns of re-posting sufferer organizations. Extra particularly, this propagation of the identical sufferer (not similar incident) via the Cyber Extortion panorama reaffirms one other concept that we’ve talked about in prior work, particularly the “opportunistic nature” of Cyber Extortion. Cyber Extortion is a quantity recreation and a method to make sure monetary acquire is to ‘play on totally different fronts’ so as to safe a minimum of some type of funds. Moreover, on a excessive stage, it exhibits how messy this ecosystem has turn out to be. All three of our hypotheses additional shine gentle onto the unpredictability of the cybercrime ecosystem.
Consequently, re-victimization shouldn’t be one thing that adjustments how Cyber Extortion works but it surely does present us the potential for various types of re-victimizations, and thus sadly will increase the struggling of sufferer organizations which have been experiencing a Cyber Extortion assault. And eventually, these sorts of analyses assist us to grasp the dynamics of a cybercrime ecosystem, on this case the Cyber Extortion / Ransomware menace panorama and its menace actors.
As with a first-time cyber-attack, for sufferer organizations you will need to handle your sufferer variables that decide the result of your victimhood. In brief, your cyber practices, your digital footprint, the worth your group’s information has to you, the time a menace actor has entry to your surroundings, the security controls you might need in place to extend the “noisiness” of knowledge exfiltration; are all variables that affect the attractiveness of your group to the opportunistic menace actors on the market in cyber area.
It is a pattern of our evaluation. A extra in depth evaluate of the menace potential of Cyber Extortion, its essential actors and the impact of legislation enforcement (in addition to a ton of different fascinating analysis matters like an evaluation of the information obtained from our in depth vulnerability administration operations and Hacktivism) may be discovered within the Safety Navigator. Simply fill within the kind and get your obtain. It is value it!




