The workplace of Pennsylvania’s legal professional basic has confirmed that the ransomware gang behind an August 2025 cyberattack stole recordsdata containing private and medical info.
This comes after Lawyer Common Dave Sunday confirmed in early September that the incident was a ransomware assault and his workplace refused to pay the ransom requested by the cybercriminals after they encrypted compromised techniques.
“The OAG later realized that sure recordsdata might have been accessed with out authorization. The OAG reviewed which knowledge might have been concerned and realized that sure private info was contained in some recordsdata,” stated the Pennsylvania Workplace of the Lawyer Common (OAG) in a Friday press launch.

“Primarily based on the OAG’s overview of the information concerned, for some people the knowledge concerned might have included title, Social Safety quantity, and/or medical info.”
On August ninth, when the breach was found, the menace actors took down techniques and companies on Pennsylvania OAG’s community, together with the workplace’s web site, staff’ e-mail accounts, and landline cellphone traces, in an assault with widespread and crippling influence.
Whereas the Pennsylvania OAG has but to share extra info on how the community was breached, cybersecurity professional Kevin Beaumont discovered that the Pennsylvania AG’s community had a number of public-facing Citrix NetScaler home equipment susceptible to ongoing assaults exploiting a vital vulnerability (CVE-2025-5777) often known as Citrix Bleed 2.
In accordance with Beaumont, one of many two gadgets was taken down since July twenty ninth, whereas the opposite has been offline since August seventh.
Breach claimed by INC Ransom
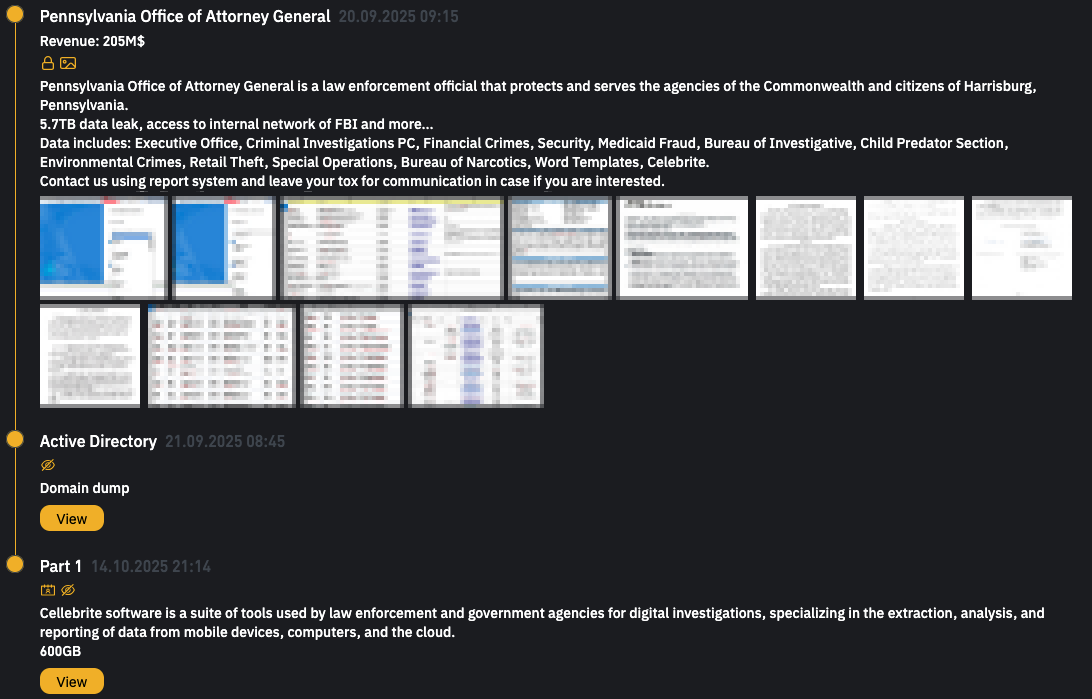
Though the Pennsylvania OAG did not publicly attribute the breach to a selected ransomware operation, the INC Ransom gang claimed duty for the assault on September twentieth, after they added it as a brand new entry on their darkish internet leak website.
On the time, the ransomware group claimed that that they had stolen 5.7TB price of recordsdata from the Pennsylvania OAG’s community and stated that the breach allegedly offered them with entry to an FBI inside community.
INC Ransom surfaced as a ransomware-as-a-service (RaaS) operation in July 2023 and has since focused organizations within the non-public and public sectors worldwide.
Its record of victims spans a variety of sectors, from training and healthcare to authorities and entities like Yamaha Motor Philippines, Scotland’s Nationwide Well being Service (NHS), meals retail large Ahold Delhaize, and the U.S. division of Xerox Enterprise Options (XBS).
That is the third time that Pennsylvania state entities have been breached in a ransomware assault: Delaware County paid a $500,000 ransom following a DoppelPaymer assault in 2020 to get better encrypted techniques, and a ransomware assault took down the Pennsylvania Senate Democratic Caucus’ community in 2017.

Whether or not you are cleansing up previous keys or setting guardrails for AI-generated code, this information helps your group construct securely from the beginning.
Get the cheat sheet and take the guesswork out of secrets and techniques administration.




