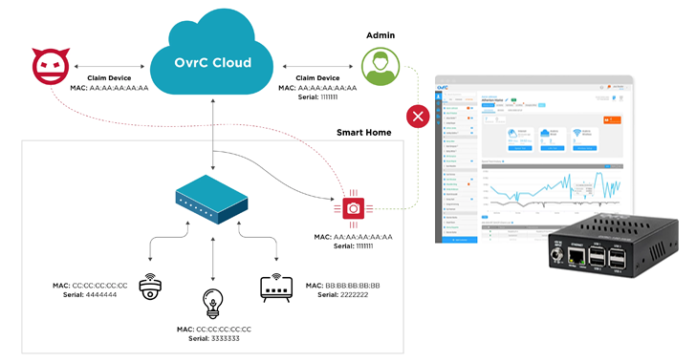
A security evaluation of the OvrC cloud platform has uncovered 10 vulnerabilities that may very well be chained to permit potential attackers to execute code remotely on related units.
“Attackers efficiently exploiting these vulnerabilities can entry, management, and disrupt units supported by OvrC; a few of these embrace sensible electrical energy provides, cameras, routers, residence automation methods, and extra,” Claroty researcher Uri Katz mentioned in a technical report.
Snap One’s OvrC, pronounced “oversee,” is marketed as a “revolutionary help platform” that permits owners and companies to remotely handle, configure, and troubleshoot IoT units on the community. In keeping with its web site, OvrC options are deployed at over 500,000 end-user places.

In keeping with a coordinated advisory issued by the U.S. Cybersecurity and Infrastructure Safety Company (CISA), profitable exploitation of the recognized vulnerabilities may permit an attacker to “impersonate and declare units, execute arbitrary code, and disclose details about the affected system.”
The failings have been discovered to affect OvrC Professional and OvrC Join, with the corporate releasing fixes for eight of them in Could 2023 and the remaining two on November 12, 2024.
“Many of those points we discovered come up from neglecting the device-to-cloud interface,” Katz mentioned. “In lots of of those instances, the core problem is the power to cross-claim IoT units due to weak identifiers or related bugs. These points vary from weak entry controls, authentication bypasses, failed enter validation, hardcoded credentials, and distant code execution flaws.”
Consequently, a distant attacker may abuse these vulnerabilities to bypass firewalls and achieve unauthorized entry to the cloud-based administration interface. Even worse, the entry may very well be subsequently weaponized to enumerate and profile units, hijack units, elevate privileges, and even run arbitrary code.

Essentially the most extreme of the failings are listed beneath –
- CVE-2023-28649 (CVSS v4 rating: 9.2), which permits an attacker to impersonate a hub and hijack a tool
- CVE-2023-31241 (CVSS v4 rating: 9.2), which permits an attacker to assert arbitrary unclaimed units by bypassing the requirement for a serial quantity
- CVE-2023-28386 (CVSS v4 rating: 9.2), which permits an attacker to add arbitrary firmware updates leading to code execution
- CVE-2024-50381 (CVSS v4 rating: 9.1), which permits an attacker to impersonate a hub and unclaim units arbitrarily and subsequently exploit different flaws to assert it
“With extra units coming on-line day-after-day and cloud administration turning into the dominant technique of configuring and accessing companies, greater than ever, the impetus is on producers and cloud service suppliers to safe these units and connections,” Katz mentioned. “The damaging outcomes can affect related energy provides, enterprise routers, residence automation methods and extra related to the OvrC cloud.”

The disclosure comes as Nozomi Networks detailed three security flaws impacting EmbedThis GoAhead, a compact internet server utilized in embedded and IoT units, that would result in a denial-of-service (DoS) below particular circumstances. The vulnerabilities (CVE-2024-3184, CVE-2024-3186, and CVE-2024-3187) have been patched in GoAhead model 6.0.1.
In current months, a number of security shortcomings have additionally been uncovered in Johnson Controls’ exacqVision Net Service that may very well be mixed to take management of video streams from surveillance cameras related to the applying and steal credentials.