The North Korea-linked risk actor often called Lazarus Group employed its time-tested fabricated job lures to ship a brand new distant entry trojan known as Kaolin RAT.
The malware might, “apart from commonplace RAT performance, change the final write timestamp of a specific file and cargo any obtained DLL binary from [command-and-control] server,” Avast security researcher Luigino Camastra stated in a report printed final week.
The RAT acts as a pathway to ship the FudModule rootkit, which has been just lately noticed leveraging a now-patched admin-to-kernel exploit within the appid.sys driver (CVE-2024-21338, CVSS rating: 7.8) to acquire a kernel learn/write primitive and in the end disable security mechanisms.
The Lazarus Group’s use of job provide lures to infiltrate targets is just not new. Dubbed Operation Dream Job, the long-running marketing campaign has a monitor file of utilizing numerous social media and instantaneous messaging platforms to ship malware.

These preliminary entry vectors trick targets into launching a malicious optical disc picture (ISO) file bearing three recordsdata, one in every of which masquerades as an Amazon VNC consumer (“AmazonVNC.exe”) that, in actuality, is a renamed model of a reputable Home windows software known as “alternative.exe.”
The 2 different recordsdata are named “model.dll” and “aws.cfg.” The executable “AmazonVNC.exe” is used to side-load “model.dll,” which, in flip, spawns an IExpress.exe course of and injects into it a payload residing inside “aws.cfg.”
The payload is designed to obtain shellcode from a command-and-control (C2) area (“henraux[.]com”), which is suspected to be an actual-but-hacked web site belonging to an Italian firm that makes a speciality of excavating and processing marble and granite.
Whereas the precise nature of the shellcode is unclear, it is stated for use to launch RollFling, a DLL-based loader that serves to retrieve and launch the next-stage malware named RollSling, which was disclosed by Microsoft final yr in reference to a Lazarus Group marketing campaign exploiting a crucial JetBrains TeamCity flaw (CVE-2023-42793, CVSS rating: 9.8).
RollSling, executed instantly in reminiscence in a probable try and evade detection by the security software program, represents the following part of the an infection process. Its major perform is to set off the execution of a 3rd loader dubbed RollMid that is additionally run within the system’s reminiscence.
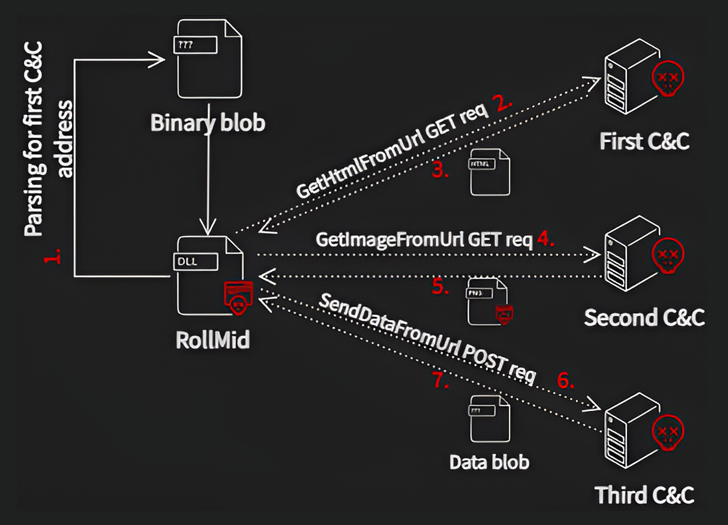
RollMid comes fitted with capabilities to set the stage for the assault and set up contact with a C2 server, which entails a three-stage strategy of its personal as follows –
- Talk with the primary C2 server to fetch a HTML containing the tackle of the second C2 server
- Talk with the second C2 server to fetch a PNG picture that embeds a malicious part utilizing a way known as steganography
- Transmit information to the third C2 server utilizing the tackle specified within the hid information inside the picture
- Retrieve an extra Base64-encoded information blob from the third C2 server, which is the Kaolin RAT
The technical sophistication behind the multi-stage sequence, whereas little doubt advanced and complex, borders on overkill, Avast opined, with the Kaolin RAT paving the way in which for the deployment of the FudModule rootkit after establishing communications with the RAT’s C2 server.

On high of that, the malware is provided to enumerate recordsdata; perform file operations; add recordsdata to the C2 server; alter a file’s final modified timestamp; enumerate, create, and terminate processes; execute instructions utilizing cmd.exe; obtain DLL recordsdata from the C2 server; and hook up with an arbitrary host.
“The Lazarus group focused people by way of fabricated job presents and employed a complicated toolset to attain higher persistence whereas bypassing security merchandise,” Camastra stated.
“It’s evident that they invested vital sources in growing such a posh assault chain. What is for certain is that Lazarus needed to innovate constantly and allocate monumental sources to analysis numerous facets of Home windows mitigations and security merchandise. Their means to adapt and evolve poses a major problem to cybersecurity efforts.”




