Cybersecurity researchers are warning {that a} command-and-control (C&C) framework known as Winos is being distributed inside gaming-related purposes like set up instruments, velocity boosters, and optimization utilities.
“Winos 4.0 is a sophisticated malicious framework that offers complete performance, a secure structure, and environment friendly management over quite a few on-line endpoints to execute additional actions,” Fortinet FortiGuard Labs stated in a report shared with The Hacker Information. “Rebuilt from Gh0st RAT, it contains a number of modular elements, every dealing with distinct capabilities.”
Campaigns distributing Winos 4.0 have been documented again in June by Development Micro and the KnownSec 404 Crew. The cybersecurity firms are monitoring the exercise cluster beneath the names Void Arachne and Silver Fox.

Attacks have been noticed focusing on Chinese language-speaking customers, leveraging black hat Search Engine Optimization (search engine marketing) techniques, social media, and messaging platforms like Telegram to distribute the malware.
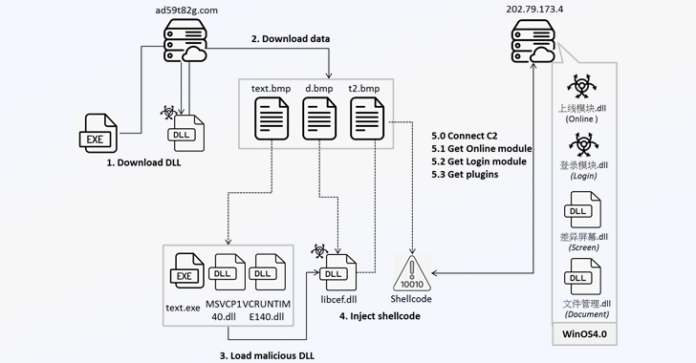
Fortinet’s newest evaluation reveals that customers who find yourself operating the malicious game-related purposes set off a multi-stage an infection course of that begins with retrieving a pretend BMP file from a distant server (“ad59t82g[.]com”) that is then decoded right into a dynamic-link library (DLL).
The DLL file takes care organising the execution setting by downloading three information from the identical server: t3d.tmp, t4d.tmp, and t5d.tmp, the primary two of that are subsequently unpacked to acquire the following set of payloads comprising an executable (“u72kOdQ.exe”) and three DLL information, together with “libcef.dll.”

“The DLL is called ‘学籍系统,’ which means ‘Pupil Registration System,’ suggesting that the menace actor could also be focusing on instructional organizations,” Fortinet stated.
Within the subsequent step, the binary is employed to load “libcef.dll,” which then extracts and executes the second-stage shellcode from t5d.tmp. The malware proceeds to ascertain contact with its command-and-control (C2) server (“202.79.173[.]4” utilizing the TCP protocol and retrieve one other DLL (“上线模块.dll”).
The third-stage DLL, a part of Winos 4.0, downloads encoded knowledge from the C2 server, a recent DLL module (“登录模块.dll”) that is answerable for harvesting system data, copying clipboard content material, gathering knowledge from cryptocurrency pockets extensions like OKX Pockets and MetaMask, and facilitating backdoor performance by awaiting additional instructions from the server.

Winos 4.0 additionally permits the supply of extra plugins from the C2 server that permit it to seize screenshots and add delicate paperwork from the compromised system.
“Winos4.0 is a robust framework, just like Cobalt Strike and Sliver, that may help a number of capabilities and simply management compromised programs,” Fortinet stated. “Menace campaigns leverage game-related purposes to lure a sufferer to obtain and execute the malware with out warning and efficiently deploy deep management of the system.”