Two vulnerabilities in Progress ShareFile, an enterprise-grade safe file switch resolution, will be chained to allow unauthenticated file exfiltration from affected environments.
Progress ShareFile is a doc sharing and collaboration product usually utilized by massive and mid-sized corporations.
Such options are a gorgeous goal for ransomware actors, as beforehand seen in Clop data-theft assaults exploiting bugs in Accellion FTA, SolarWinds Serv-U, Gladinet CentreStack, GoAnywhere MFT, MOVEit Switch, and Cleo.
Researchers at offensive security firm watchTowr found an authentication bypass (CVE-2026-2699) and a distant code execution (CVE-2026-2701) within the Storage Zones Controller (SZC) element current in department 5.x of Progress ShareFile.
SZC offers prospects extra management over their knowledge by permitting them to retailer it on their infrastructure (both on-prem or in a third-party cloud supplier) or on the Progress techniques.
Following watchTowr’s accountable disclosure, the issues have been addressed in Progress ShareFile 5.12.4, launched on March 10.
How the assault works
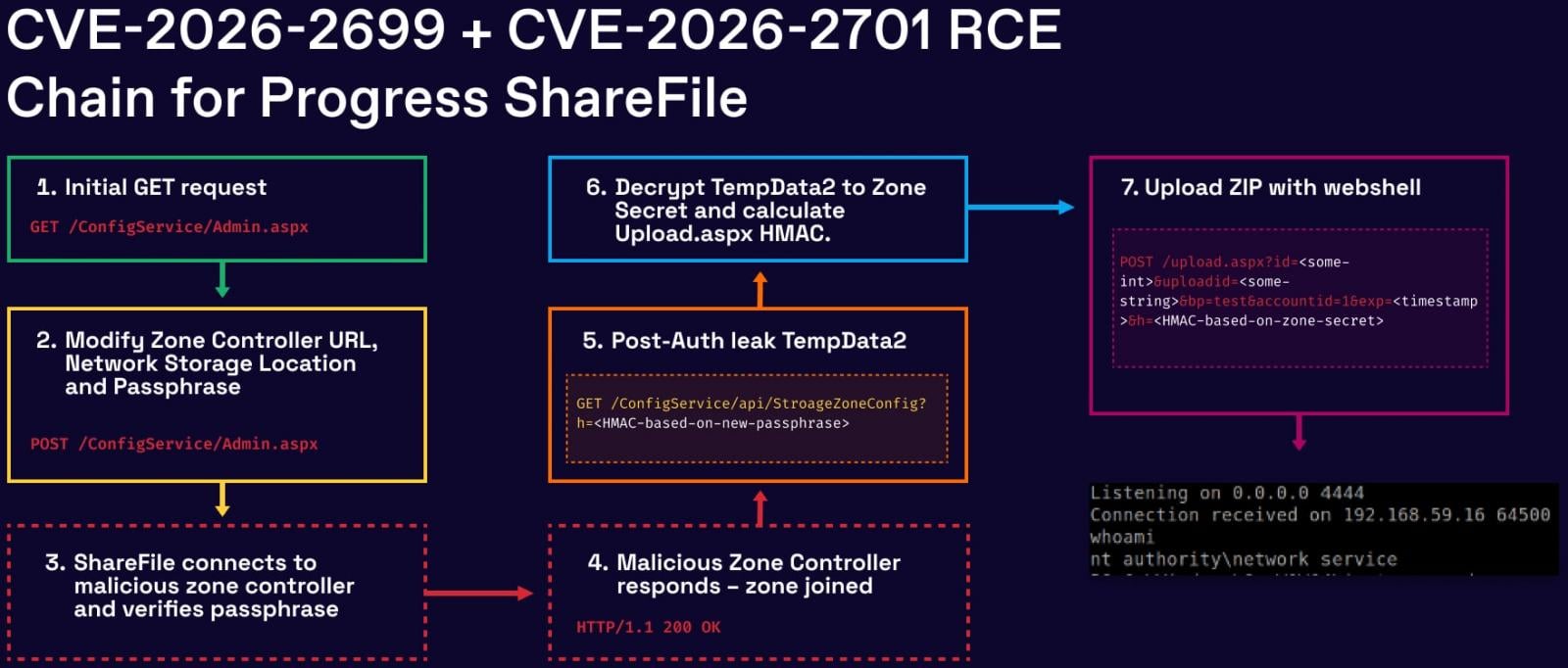
In a report at present, watchTowr researchers clarify that the assault begins by exploiting the authentication bypass subject, CVE-2026-2699, which supplies entry to the ShareFile admin interface resulting from improper dealing with of HTTP redirects.
As soon as inside, an attacker can modify Storage Zone configuration settings, together with file storage paths and security-sensitive parameters such because the zone passphrase and associated secrets and techniques.
By exploiting the second flaw, CVE-2026-2701, attackers can receive distant code execution on the server by abusing file add and extraction performance to position malicious ASPX webshells within the utility’s webroot.
The researchers observe that, for the exploit to work, attackers should generate legitimate HMAC signatures and extract and decrypt inside secrets and techniques. Nevertheless, these are achievable after exploiting CVE-2026-2699 as a result of capability to set or management passphrase-related values.
Supply: WatchTowr
Impression and publicity
By watchTowr’s scans, there are about 30,000 Storage Zone Controller situations uncovered on the general public web.
The ShadowServer Basis at the moment observes 700 internet-exposed situations of Progress ShareFile, most of that are situated in america and Europe.
watchTowr found the 2 flaws and reported them to Progress between February 6 and 13, and the total exploit chain was confirmed on February 18 for Progress ShareFile 5.12.4. The seller launched security updates in model 5.12.4, launched on March 10.
Though no lively exploitation within the wild has been noticed as of writing, techniques working susceptible variations of ShareFile Storage Zone Controller must be patched instantly, as the general public disclosure of the chain is more likely to entice risk actors.

Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, exhibits the place protection ends, and supplies practitioners with three diagnostic questions for any software analysis.




