Risk hunters have disclosed a brand new “widespread timing-based vulnerability class” that leverages a double-click sequence to facilitate clickjacking assaults and account takeovers in virtually all main web sites.
The method has been codenamed DoubleClickjacking by security researcher Paulos Yibelo.
“As a substitute of counting on a single click on, it takes benefit of a double-click sequence,” Yibelo mentioned. “Whereas it’d sound like a small change, it opens the door to new UI manipulation assaults that bypass all recognized clickjacking protections, together with the X-Body-Choices header or a SameSite: Lax/Strict cookie.”

Clickjacking, additionally known as UI redressing, refers to an assault method through which customers are tricked into clicking on a seemingly innocuous internet web page factor (e.g., a button), resulting in the deployment of malware or exfiltration of delicate knowledge.
DoubleClickjacking is a variation of this theme that exploits the hole between the beginning of a click on and the tip of the second click on to bypass security controls and takeover accounts with minimal interplay.
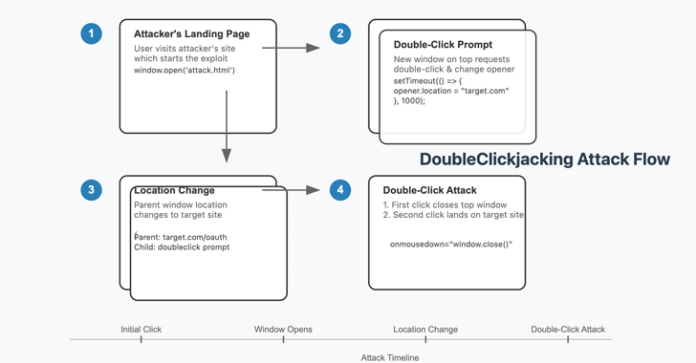
Particularly, it entails the next steps –
- The consumer visits an attacker-controlled web site that both opens a brand new browser window (or tab) with none consumer interplay or on the click on of a button.
- The brand new window, which might mimic one thing innocuous like a CAPTCHA verification, prompts the consumer to double-click to finish the step.
- Because the double-click is underway, the father or mother web site makes use of the JavaScript Window Location object to stealthily redirect to a malicious web page (e.g., approving a malicious OAuth utility)
- On the identical time, the highest window is closed, permitting a consumer to unknowingly grant entry by approving the permission affirmation dialog.
“Most internet apps and frameworks assume that solely a single compelled click on is a threat,” Yibelo mentioned. “DoubleClickjacking provides a layer many defenses have been by no means designed to deal with. Strategies like X-Body-Choices, SameSite cookies, or CSP can not defend in opposition to this assault.”
Web site homeowners can eradicate the vulnerability class utilizing a client-side strategy that disables essential buttons by default until a mouse gesture or key press is detected. Companies like Dropbox already make use of such preventative measures, it has been discovered.
As long-term options, it is really useful that browser distributors undertake new requirements akin to X-Body-Choices to defend in opposition to double-click exploitation.
“DoubleClickjacking is a twist on a widely known assault class,” Yibelo mentioned. “By exploiting the occasion timing between clicks, attackers can seamlessly swap out benign UI components for delicate ones within the blink of a watch.”

The disclosure arrives almost a yr after the researcher additionally demonstrated one other clickjacking variant known as cross window forgery (aka gesture-jacking) that depends on persuading a sufferer to press or maintain down the Enter key or House bar on an attacker-controlled web site to provoke a malicious motion.
On web sites like Coinbase and Yahoo!, it could possibly be abused to realize an account takeover “if a sufferer that’s logged into both web site goes to an attacker web site and holds the Enter/House key.”
“That is doable as a result of each websites enable a possible attacker to create an OAuth utility with vast scope to entry their API, they usually each set a static and / or predictable ‘ID’ worth to the ‘Enable/Authorize’ button that’s used to authorize the applying into the sufferer’s account.”