North Korean menace actors are actively exploiting a important security flaw in JetBrains TeamCity to opportunistically breach susceptible servers, in accordance with Microsoft.
The assaults, which entail the exploitation of CVE-2023-42793 (CVSS rating: 9.8), have been attributed to Diamond Sleet (aka Labyrinth Chollima) and Onyx Sleet (aka Andariel or Silent Chollima).
It is price noting that each the menace exercise clusters are a part of the notorious North Korean nation-state actor generally known as Lazarus Group.
In one of many two assault paths employed by Diamond Sleet, a profitable compromise of TeamCity servers is adopted by the deployment of a identified implant known as ForestTiger from professional infrastructure beforehand compromised by the menace actor.
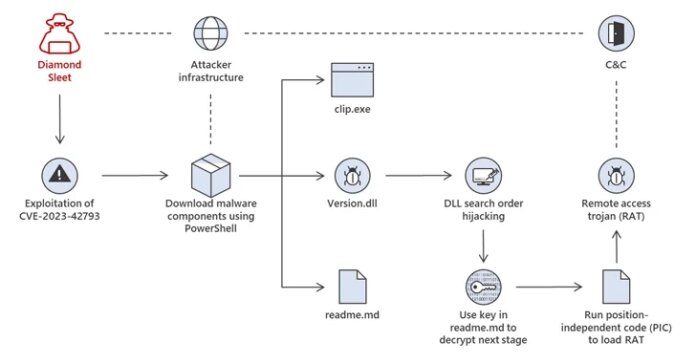
A second variant of the assaults leverages the preliminary foothold to retrieve a malicious DLL (DSROLE.dll aka RollSling or Model.dll or FeedLoad) that is loaded by way of a method known as DLL search-order hijacking to both execute a next-stage payload or a distant entry trojan (RAT).
Microsoft stated it witnessed the adversary leveraging a mixture of instruments and methods from each assault sequences in sure situations.
The intrusions mounted by Onyx Sleet, alternatively, use the entry afforded by the exploitation of the JetBrains TeamCity bug to create a brand new consumer account named krtbgt that is seemingly supposed to impersonate the Kerberos Ticket Granting Ticket.
“After creating the account, the menace actor provides it to the Native Directors Group via internet use,” Microsoft stated. “The menace actor additionally runs a number of system discovery instructions on compromised techniques.”
The assaults subsequently result in the deployment of a customized proxy instrument dubbed HazyLoad that helps set up a persistent connection between the compromised host and attacker-controlled infrastructure.
One other notable post-compromise motion is using the attacker-controlled krtbgt account to signal into the compromised machine through distant desktop protocol (RDP) and terminating the TeamCity service in a bid to forestall entry by different menace actors.
Through the years, the Lazarus group has established itself as some of the pernicious and complicated superior persistent menace (APT) teams at present lively, orchestrating monetary crime and espionage assaults in equal measure through cryptocurrency heists and provide chain assaults.
“We actually consider that North Korean hacking of cryptocurrency round infrastructure, all over the world – together with in Singapore, Vietnam, and Hong Kong – is a significant income for the regime that is used to finance the advancing of the missile program and the far larger variety of launches we now have seen within the final 12 months,” U.S. Deputy Nationwide Safety Advisor, Anne Neuberger, stated.
The event comes because the AhnLab Safety Emergency Response Heart (ASEC) detailed the Lazarus Group’s use of malware households reminiscent of Volgmer and Scout that act as a conduit for serving backdoors for controlling the contaminated techniques.
“The Lazarus group is likely one of the very harmful teams which are extremely lively worldwide, utilizing varied assault vectors reminiscent of spear-phishing and provide chain assaults,” the South Korean cybersecurity agency stated, implicating the hacking crew to a different marketing campaign codenamed Operation Dream Magic.
This entails mounting watering gap assaults by inserting a rogue hyperlink inside a selected article on an unspecified information web site that weaponizes security flaws in INISAFE and MagicLine merchandise to activate the infections, a tactic beforehand related to the Lazarus Group.
In an extra signal of North Korea’s evolving offensive applications, ASEC has attributed one other menace actor generally known as Kimsuky (aka APT43) to a contemporary set of spear-phishing assaults that make the most of the BabyShark malware to put in a motley slate of distant desktop instruments and VNC software program (i.e., TightVNC and TinyNuke) to commandeer sufferer techniques and exfiltrate data.