Microsoft has make clear an ongoing phishing marketing campaign that focused the hospitality sector by impersonating on-line journey company Reserving.com utilizing an more and more common social engineering method known as ClickFix to ship credential-stealing malware.
The exercise, the tech large mentioned, began in December 2024 and operates with the tip objective of conducting monetary fraud and theft. It is monitoring the marketing campaign underneath the moniker Storm-1865.
“This phishing assault particularly targets people in hospitality organizations in North America, Oceania, South and Southeast Asia, and Northern, Southern, Jap, and Western Europe, which are probably to work with Reserving.com, sending faux emails purporting to be coming from the company,” Microsoft mentioned in a report shared with The Hacker Information.
The ClickFix method has change into widespread in current months, because it methods customers into executing malware underneath the guise of fixing a supposed (i.e., non-existent) error by copying, pasting, and launching misleading directions that activate the an infection course of. It was first detected within the wild in October 2023.
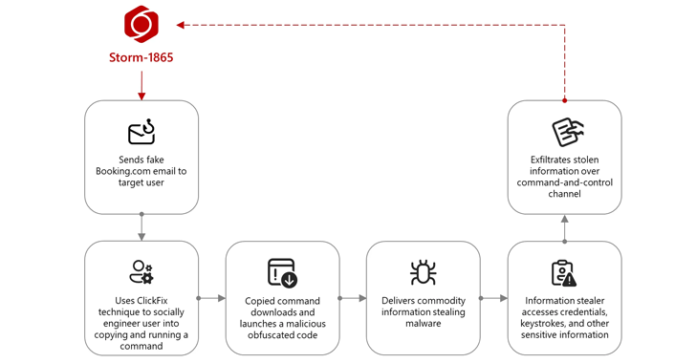
The assault sequence begins with Storm-1865 sending a malicious e mail to a focused particular person a few destructive evaluate left by a purported visitor on Reserving.com, and asking them for his or her “suggestions.” The message additionally embeds a hyperlink, or a PDF attachment containing one which seemingly directs the recipients to the reserving web site.

Nevertheless, in actuality, clicking on it leads the sufferer to a faux CAPTCHA verification web page that is overlaid on a “subtly seen background designed to imitate a reliable Reserving.com web page.” In doing so, the thought is to lend a false sense of security and improve the chance of a profitable compromise.
“The faux CAPTCHA is the place the webpage employs the ClickFix social engineering method to obtain the malicious payload,” Microsoft mentioned. “This system instructs the person to make use of a keyboard shortcut to open a Home windows Run window, then paste and launch a command that the webpage provides to the clipboard.”
The command, in a nutshell, makes use of the reliable mshta.exe binary to drop the next-stage payload, which contains varied commodity malware households like XWorm, Lumma stealer, VenomRAT, AsyncRAT, Danabot, and NetSupport RAT.
Redmond mentioned it beforehand noticed Storm-1865 concentrating on patrons utilizing e-commerce platforms with phishing messages resulting in fraudulent fee internet pages. The incorporation of the ClickFix method, subsequently, illustrates a tactical evolution designed to slide previous typical security measures in opposition to phishing and malware.
“The menace actor that Microsoft tracks as Storm-1865 encapsulates a cluster of exercise conducting phishing campaigns, resulting in fee knowledge theft and fraudulent costs,” it added.
“These campaigns have been ongoing with elevated quantity since at the least early 2023 and contain messages despatched by means of vendor platforms, resembling on-line journey companies and e-commerce platforms, and e mail providers, resembling Gmail or iCloud Mail.”

Storm-1865 represents simply one of many many campaigns which have embraced ClickFix as a vector for malware distribution. Such is the effectiveness of this system that even Russian and Iranian nation-state teams like APT28 and MuddyWater have adopted it to lure their victims.
“Notably, the strategy capitalizes on human conduct: by presenting a believable ‘resolution’ to a perceived downside, attackers shift the burden of execution onto the person, successfully sidestepping many automated defenses,” Group-IB mentioned in an impartial report revealed at present.
One such marketing campaign documented by the Singaporean cybersecurity firm entails using ClickFix to drop a downloader named SMOKESABER, which then serves as a conduit for Lumma Stealer. Different campaigns have leveraged malvertising, search engine marketing poisoning, GitHub points, and spamming boards or social media websites with hyperlinks to ClickFix pages.
“The ClickFix method marks an evolution in adversarial social engineering methods, leveraging person belief and browser performance for malware deployment,” Group-IB mentioned. “The fast adoption of this methodology by each cybercriminals and APT teams underscores its effectiveness and low technical barrier.”
Among the different ClickFix campaigns which were documented are listed under –
The varied an infection mechanisms of Lumma Stealer is additional exemplified by the invention of one other marketing campaign that makes use of bogus GitHub repositories that includes synthetic intelligence (AI)-content to ship the stealer by way of a loader known as SmartLoader.

“These malicious repositories are disguised as non-malicious instruments, together with sport cheats, cracked software program, and cryptocurrency utilities,” Pattern Micro mentioned in an evaluation revealed earlier this week. “The marketing campaign entices victims with guarantees of free or illicit unauthorized performance, prompting them to obtain ZIP information (e.g., Launch.zip, Software program.zip).”
The operation serves to spotlight how menace actors are abusing the belief related to common platforms like GitHub for malware propagation.

The findings come as Trustwave detailed an e mail phishing marketing campaign that makes use of invoice-related decoys to distribute an up to date model of one other stealer malware known as StrelaStealer, which is assessed to be operated by a single menace actor dubbed Hive0145.
“StrelaStealers samples embody customized multi-layer obfuscation and code-flow flattening to complicate its evaluation,” the corporate mentioned. “It has been reported that the menace actor probably developed a specialised crypter known as ‘Stellar loader,’ particularly, for use with the StrelaStealer.”