Menace actors are actively exploiting a vital vulnerability within the Service Finder WordPress theme that permits them to bypass authentication and log in as directors.
Administrator privileges in WordPress grant full management over content material and settings, permission to create accounts, add PHP information, and export databases.
WordPress plugin security agency Wordfence recorded greater than 13,800 exploitation atempts since August 1st.
Service Finder is a premium WordPress theme designed for service listing and job board web sites. It helps buyer reserving, suggestions, time slot administration, employees administration, bill era, and a fee system.
The theme has extra 6,000 gross sales on Envato Market, and like most premium plugins, it’s sometimes utilized by energetic websites.
The vulnerability exploited within the newest assaults is tracked as CVE-2025-5947 and has a vital severity rating of 9.8. It impacts Service Finder variations 6.0 and older, stemming from an improper validation of the original_user_id cookie within the service_finder_switch_back() operate.
An attacker exploiting CVE-2025-5947 can log in as any person, together with directors, with out authentication.
The problem was found by security researcher ‘Foxyyy,’ who reported it by means of Wordfence’s bug bounty program on June 8.
Aonetheme, the theme’s vendor, addressed the security subject in model 6.1, launched on July 17. On the finish of the month, the difficulty was publicly disclosed and exploitation started the subsequent day.
For a couple of week since September 23, Wordfence noticed a surge of greater than 1,500 assault makes an attempt day by day. General, the researchers noticed greater than 13,800 exploit makes an attempt.
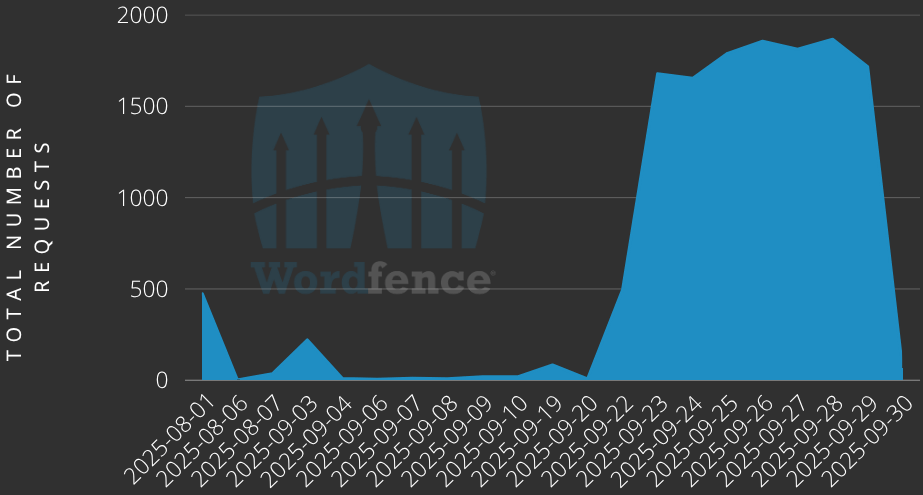
Supply: Wordfence
Primarily based on Wordfence’s observations, a typical assault contains an HTTP GET request to the foundation path with a question parameter (switch_back=1) to impersonate an present person.
The researchers say that there are a number of IP addresses used for launching the assaults. Nevertheless, hundreds of assault requests orginated from simply 5 of them:
- 5.189.221.98
- 185.109.21.157
- 192.121.16.196
- 194.68.32.71
- 178.125.204.198
As a part of protection measures towards these assaults is blocklisting the above IP addresses. Nevertheless, it must be famous that attackers can change to new ones.
The researchers say that there aren’t any clear indicators of compromise to cease these assaults aside from requests that comprise the ‘switch_back’ parameter.
Web site directors ought to overview all logs for suspicious exercise or accounts that menace actors might create for persistence.
Wordfence warns that “the absence of any such log entries doesn’t assure that your web site has not been compromised,” as administrator entry provides attackers the potential to cowl their tracks by deleting logs or different proof.
Given the energetic exploitation standing of CVE-2025-5947, customers of the Service Finder theme are really useful to use the security replace as quickly as attainable or cease utilizing the plugin.

Be a part of the Breach and Attack Simulation Summit and expertise the way forward for security validation. Hear from high specialists and see how AI-powered BAS is reworking breach and assault simulation.
Do not miss the occasion that may form the way forward for your security technique




