Clients of eating places utilizing the HungerRush point-of-sale (POS) platform say they acquired emails from a risk actor trying to extort the corporate, warning that restaurant and buyer knowledge might be uncovered if HungerRush fails to reply.
HungerRush is a restaurant expertise supplier that provides point-of-sale (POS), on-line ordering, supply administration, and fee processing software program to assist eating places handle orders, buyer data, and enterprise operations.
The corporate claims to work with over 16,000 eating places, together with Sbarro, Jet’s Pizza, Fajita Pete’s, Hungry Howie’s, and plenty of extra.
Extortion emails despatched to restaurant patrons
The attacker began sending the emails early Wednesday morning, with a number of recipients sharing samples with BleepingComputer.
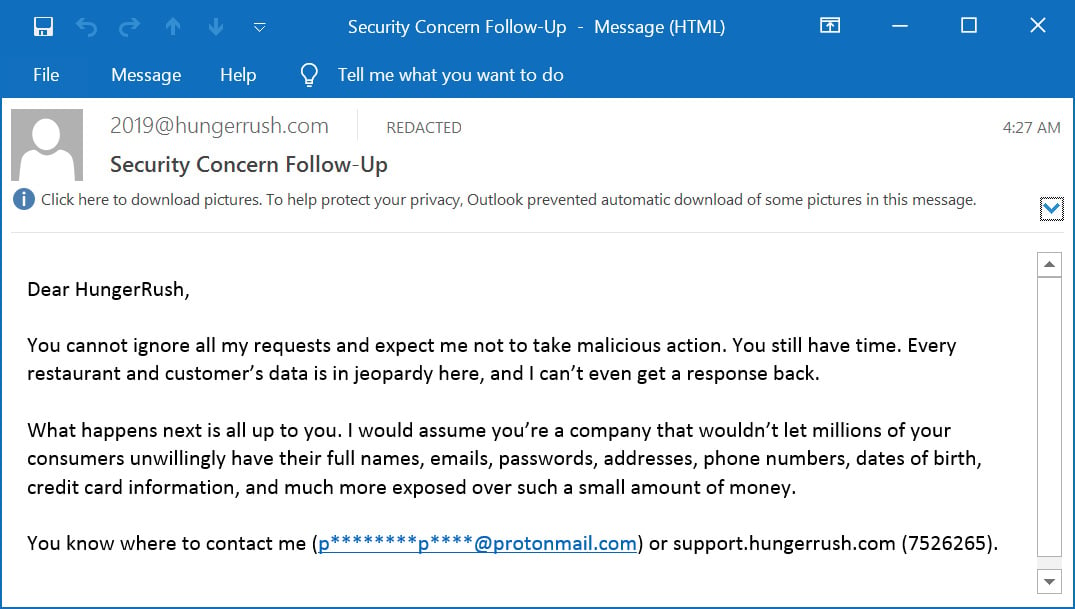
The primary e mail was despatched from assist@hungerrush.com, prompting HungerRush to cease ignoring their extortion emails or it might put buyer knowledge in danger.
“You can not ignore all my requests and count on me to not take malicious actions. You continue to have time,” reads the e-mail.
“Each restaurant and buyer of mentioned eating places’ knowledge which is within the hundreds of thousands is in jeopardy right here and I can not even get a response again. To not fear, there’s nonetheless time left.”
A second e mail, despatched three hours later from “2019@hungerrush.com,” escalates the risk, claiming that the attacker has entry to knowledge data for hundreds of thousands of shoppers that include names, emails, passwords, addresses, cellphone numbers, dates of delivery, and bank card data.
Supply: BleepingComputer
BleepingComputer’s evaluation of the e-mail headers reveals they have been delivered utilizing Twilio SendGrid, which prospects have advised BleepingComputer was beforehand used to ship HungerRush restaurant receipts.
The emails have been despatched from o10.e.hungerrush.com (159.183.129.119), which resolves to infrastructure operated by Twilio SendGrid, a platform generally utilized by corporations to ship transactional and advertising emails.
The e-mail headers additionally affirm that the messages handed SPF, DKIM, and DMARC authentication checks for the hungerrush.com area, as the corporate’s SPF file, proven under, authorizes SendGrid to ship emails on their behalf.
v=spf1 embrace:spf.safety.outlook.com embrace:_spf.salesforce.com embrace:mail.zendesk.com embrace:_spf.psm.knowbe4.com embrace:sendgrid.web embrace:4750273.spf01.hubspotemail.web -all
Quite a few individuals on Reddit have reported receiving the emails, stating that previous digital receipts from eating places confirmed they used HungerRush’s ordering or POS techniques.
Alon Gal, co-founder and CTO of Hudson Rock, posted on LinkedIn that infostealer logs point out a HungerRush worker’s system was allegedly contaminated with an infostealer in October 2025, resulting in the compromise of credentials.
Based on Gal, the malware stole quite a few company credentials, together with these for the corporate’s NetSuite, QuickBooks-related providers, Stripe dashboards, Invoice.com vendor fee techniques, Visa On-line industrial providers, and Salesforce environments.
It’s unclear if these stolen credentials are linked to the claimed breach at HungerRush.
BleepingComputer contacted HungerRush concerning the incident and requested whether or not the emails point out a confirmed breach or unauthorized entry to its techniques.
In the interim, prospects of eating places utilizing the HungerRush POS system ought to be on alert for potential phishing emails and SMS texts that abuse the possibly stolen data.

Malware is getting smarter. The Pink Report 2026 reveals how new threats use math to detect sandboxes and conceal in plain sight.
Obtain our evaluation of 1.1 million malicious samples to uncover the highest 10 strategies and see in case your security stack is blinded.




