A vital security flaw impacting the LayerSlider plugin for WordPress may very well be abused to extract delicate info from databases, similar to password hashes.
The flaw, designated as CVE-2024-2879, carries a CVSS rating of 9.8 out of a most of 10.0. It has been described as a case of SQL injection impacting variations from 7.9.11 by way of 7.10.0.
The difficulty has been addressed in model 7.10.1 launched on March 27, 2024, following accountable disclosure on March 25. “This replace consists of essential security fixes,” the maintainers of LayerSlider stated of their launch notes.
LayerSlider is a visible internet content material editor, a graphic design software program, and a digital visible results that enables customers to create animations and wealthy content material for his or her web sites. In response to its personal website, the plugin is utilized by “hundreds of thousands of customers worldwide.”

The flaw found within the software stems from a case of inadequate escaping of consumer equipped parameters and the absence of wpdb::put together(), enabling unauthenticated attackers to append further SQL queries and glean delicate info, Wordfence stated.
The event follows the invention of an unauthenticated saved cross-site scripting (XSS) flaw within the WP-Members Membership Plugin (CVE-2024-1852, CVSS rating: 7.2) that might facilitate the execution of arbitrary JavaScript code. It has been resolved in model 3.4.9.3.
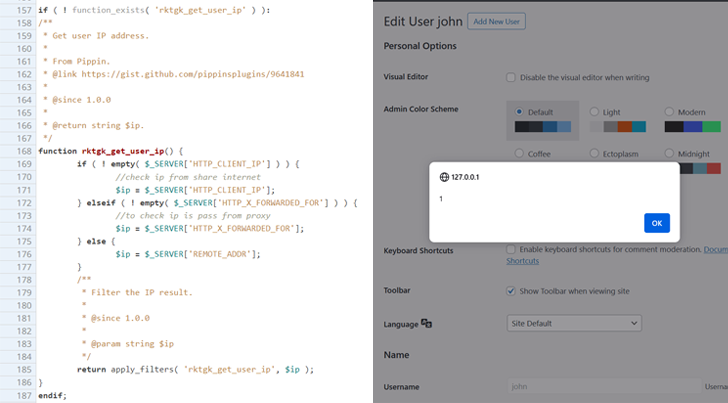
The vulnerability, as a result of inadequate enter sanitization and output escaping, “makes it attainable for unauthenticated attackers to inject arbitrary internet scripts in pages that may execute every time a consumer accesses an injected web page which is the edit customers web page,” the WordPress security firm stated.
Ought to the code be executed within the context of an administrator’s browser session, it may be used to create rogue consumer accounts, redirect website guests to different malicious websites, and perform different assaults, it added.
Over the previous few weeks, security vulnerabilities have additionally been disclosed in different WordPress plugins similar to Tutor LMS (CVE-2024-1751, CVSS rating: 8.8) and Contact Kind Entries (CVE-2024-2030, CVSS rating: 6.4) that may very well be exploited for info disclosure and inject arbitrary internet scripts, respectively.




