SolarWinds has launched security updates to patch 4 important Serv-U distant code execution vulnerabilities that might grant attackers root entry to unpatched servers.
Serv-U is the corporate’s self-hosted Home windows and Linux file switch software program that comes with each Managed File Switch (MFT) and FTP server capabilities, enabling organizations to securely change recordsdata through FTP, FTPS, SFTP, and HTTP/S.
Essentially the most extreme of the 4 security flaws patched by SolarWinds in the present day in Serv-U 15.5.4 is tracked as CVE-2025-40538, and it permits attackers with excessive privileges to realize root or admin permissions on susceptible servers.

“A damaged entry management vulnerability exists in Serv-U which, when exploited, offers an attacker the power to create a system admin consumer and execute arbitrary code as root through area admin or group admin privileges,” SolarWinds stated in a Tuesday advisory.
The corporate additionally patched two kind confusion flaws and an Insecure Direct Object Reference (IDOR) vulnerability that may be exploited to realize code execution with root privileges.
Fortunately, all 4 security flaws require attackers to have already got excessive privileges on the focused servers, which can restrict potential exploitation makes an attempt to eventualities the place attackers can chain privilege escalation vulnerabilities or use beforehand stolen admin credentials.
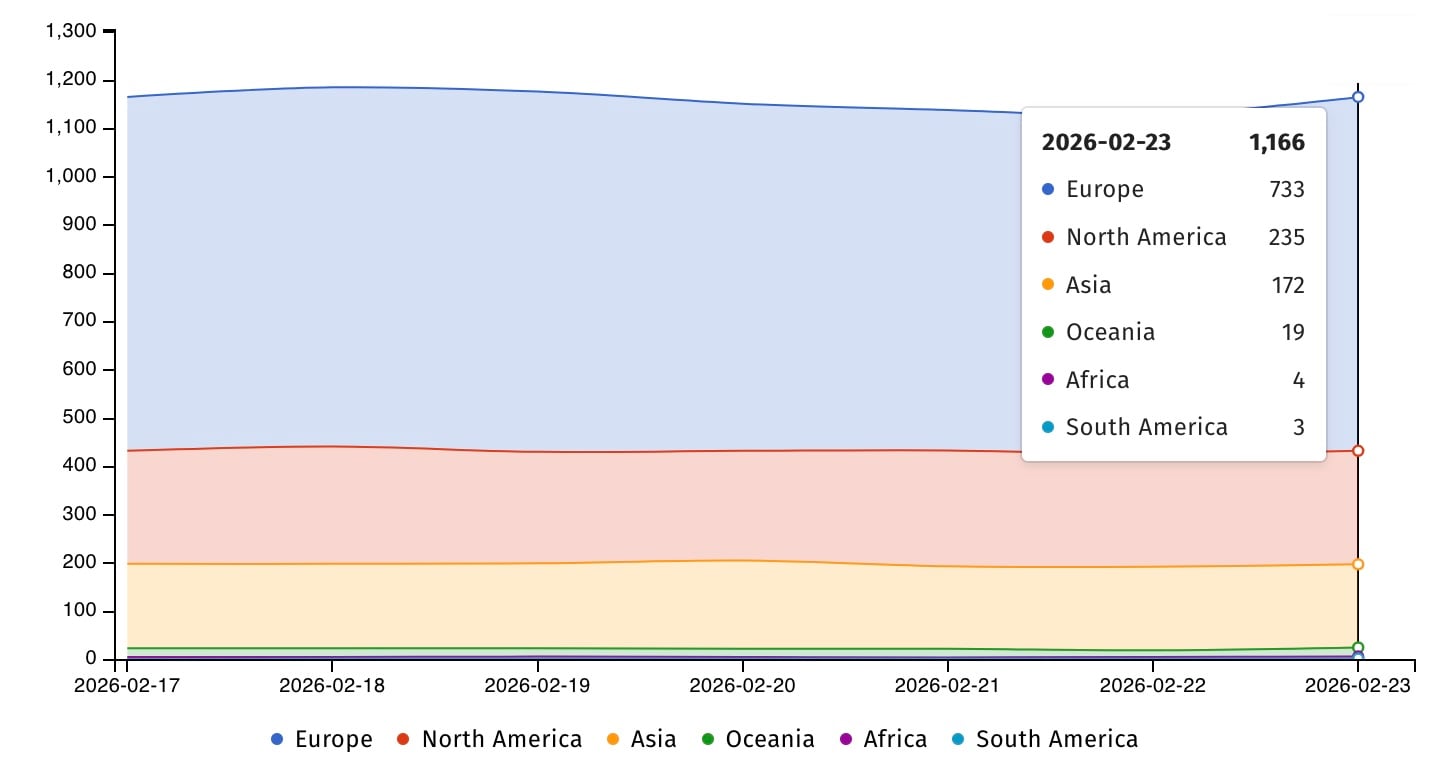
Shodan presently tracks over 12,000 Web-exposed Serv-U servers, whereas Shadowserver estimates the quantity to be lower than 1,200.
File switch software program like SolarWinds Serv-U is usually focused in assaults as a result of it gives quick access to paperwork that will include delicate company and buyer knowledge.
During the last 5 years, a number of cybercrime and state-sponsored hacking teams have focused Serv-U vulnerabilities in knowledge theft assaults, with the Clop gang having exploited a Serv-U Safe FTP distant code execution vulnerability (CVE-2021-35211) to breach company networks in ransomware assaults.
China-based hackers (tracked by Microsoft as DEV-0322), identified for primarily focusing on U.S. protection and software program firms, additionally deployed CVE-2021-35211 exploits in zero-day assaults beginning in July 2021.
Extra not too long ago, in June 2024, cybersecurity firms Rapid7 and GreyNoise flagged a SolarWinds Serv-U path-traversal vulnerability (CVE-2024-28995) as actively exploited by risk actors who used publicly accessible proof-of-concept (PoC) exploits.
The U.S. Cybersecurity and Infrastructure Safety Company (CISA) is presently monitoring 9 SolarWinds security flawsthat have both been or are nonetheless actively being exploited within the wild.

Fashionable IT infrastructure strikes quicker than guide workflows can deal with.
On this new Tines information, find out how your staff can cut back hidden guide delays, enhance reliability by way of automated response, and construct and scale clever workflows on prime of instruments you already use.




