The kernel exploit for 2 security vulnerabilities used within the not too long ago uncovered Apple iOS exploit package often called Coruna is an up to date model of the identical exploit that was used within the Operation Triangulation marketing campaign again in 2023, based on new findings from Kaspersky.
“When Coruna was first reported, the general public proof wasn’t adequate to hyperlink its code to Triangulation — shared vulnerabilities alone do not show shared authorship,” Boris Larin, principal security researcher at Kaspersky GReAT, advised The Hacker Information in an announcement.
“Coruna shouldn’t be a patchwork of public exploits; it’s a repeatedly maintained evolution of the unique Operation Triangulation framework. The inclusion of checks for current processors just like the M3 and newer iOS builds reveals that the unique builders have actively expanded this codebase. What started as a precision espionage software is now deployed indiscriminately.”
Coruna was first documented by Google and iVerify earlier this month as focusing on Apple iPhone fashions operating iOS variations between 13.0 and 17.2.1.
Though using the package was first utilized by a buyer of an unnamed surveillance firm early final yr, it has since been leveraged by a suspected Russia-aligned nation-state actor in watering gap assaults in Ukraine and in a mass exploitation marketing campaign that employed a cluster of pretend Chinese language playing and cryptocurrency web sites to ship a data-stealing malware often called PlasmaLoader (aka PLASMAGRID).
The exploit package incorporates 5 full iOS exploit chains and a complete of 23 exploits, together with CVE-2023-32434 and CVE-2023-38606, each of which had been first used as zero-days in Operation Triangulation, a classy marketing campaign focusing on iOS units that concerned the exploitation of 4 vulnerabilities in Apple’s cell working system.
The most recent findings from Kaspersky indicated the kernel exploits in each Triangulation and Coruna had been created by the identical writer, with Coruna additionally utilizing 4 further kernel exploits. The Russian security vendor stated all these exploits are constructed on the identical kernel exploitation framework and share frequent code.
Particularly, the code consists of help for Apple’s A17, M3, M3 Professional, and M3 Max processors, together with checks for iOS 17.2 and iOS model 16.5 beta 4, the latter of which patched all 4 vulnerabilities exploited as a part of Operation Triangulation. The examine for iOS 17.2, alternatively, is supposed to take note of the newer exploits, Kaspersky stated.
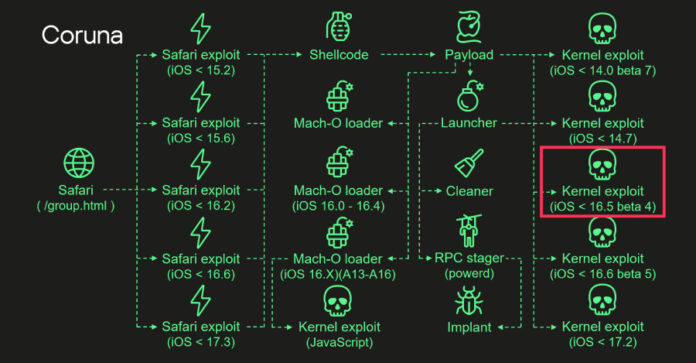
The start line of the assault is when a person visits a compromised web site on Safari, inflicting a stager to fingerprint the browser and serve the suitable exploit primarily based on the browser and working system model. This, in flip, paves the best way for the execution of a payload that triggers the kernel exploit.
“After downloading the mandatory parts, the payload begins executing kernel exploits, Mach-O loaders, and the malware launcher,” Kaspersky stated. “The payload selects an applicable Mach-O loader primarily based on the firmware model, CPU, and presence of the iokit-open-service permission.”
The launcher is the first orchestrator liable for initiating the post-exploitation actions, leveraging the kernel exploit to drop and execute the ultimate implant. It additionally cleans up exploitation artifacts to cowl up the forensic path.
“Initially developed for cyber-espionage functions, this framework is now being utilized by cybercriminals of a broader sort, inserting thousands and thousands of customers with unpatched units in danger,” Larin stated. “Given its modular design and ease of reuse, we count on that different risk actors will start incorporating it into their assaults.”
The event comes as a brand new model of iPhone exploit package DarkSword has been leaked on GitHub, elevating considerations that it might equip extra risk actors with superior capabilities to compromise units, successfully turning what was as soon as an elite hacking software right into a mass exploitation framework. The discharge of the brand new model was first reported by TechCrunch.