Operational Know-how (OT) refers back to the {hardware} and software program used to alter, monitor, or management the enterprise’s bodily gadgets, processes, and occasions. In contrast to conventional Data Know-how (IT) techniques, OT techniques immediately impression the bodily world. This distinctive attribute of OT brings further cybersecurity concerns not sometimes current in typical IT security architectures.
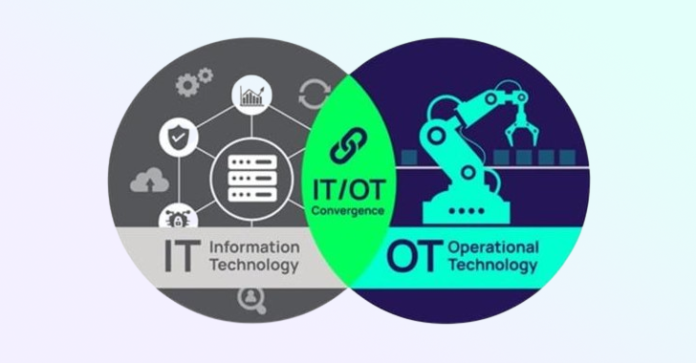
The convergence of IT and OT
Traditionally, IT and Operational Know-how (OT) have operated in separate silos, every with its personal set of protocols, requirements, and cybersecurity measures. Nevertheless, these two domains are more and more converging with the appearance of the Industrial Web of Issues (IIoT). Whereas helpful by way of elevated effectivity and data-driven decision-making, this convergence additionally exposes OT techniques to the identical cyber threats that IT techniques face.
Distinctive Cybersecurity Concerns for OT
Actual-time necessities
Operational Know-how techniques usually function in real-time and can’t afford delays. A delay in an OT system may result in important operational points and even security hazards. Subsequently, OT cybersecurity measures that introduce latency, reminiscent of multi-factor authentication, just-in-time entry request workflows, and session exercise monitoring, is probably not appropriate for OT environments.
Word that the impression of those options on system efficiency can fluctuate primarily based on the precise PAM resolution and the way it’s configured. Subsequently, it is essential to completely take a look at any PAM resolution in a real-time surroundings to make sure it meets efficiency necessities whereas nonetheless offering vital security controls.
Legacy techniques and connectivity
Many Operational Know-how techniques are nonetheless previous within the tooth. They’re proprietary and customised to fulfill the wants of longevity and resilience beneath harsh circumstances. Cybersecurity was not a high-priority consideration for legacy OT techniques, in order that they lack resilience towards up to date OT cybersecurity threats, leading to excessive threat.
They could lack primary security capabilities reminiscent of encryption, authentication, and Multi-Issue Authentication (MFA.) Modernizing these techniques presents important challenges by way of price, operational disruptions, and compatibility points. Individuals with information and expertise is probably not out there, making understanding the design and the code inconceivable.
With the rising integration of those techniques into IT networks and, often, the web, their susceptibility to cyber threats is amplified. Whereas helpful for operational effectivity, this connectivity inadvertently expands their assault floor, thereby escalating their vulnerability.
Some examples of distinctive security challenges embody:
- Outdated {Hardware} and Software program: Out of date {hardware} and software program introduce important security challenges due primarily to incompatibility with trendy off-the-shelf security options and greatest practices. This exposes legacy OT techniques to unauthorized surveillance, data breaches, ransomware assaults, and potential manipulation.
- Lack of Encryption: Encryption is essential for safeguarding delicate information and communications. Nonetheless, older OT techniques may not have the potential to help encryption, which exposes them to assaults that might jeopardize the confidentiality and integrity of knowledge.
- Insecure Communication Protocols: Legacy OT techniques might use insecure communication protocols that attackers can exploit. For instance, Modbus, a extensively used communication protocol in legacy OT techniques, doesn’t embody authentication or encryption, making it weak to assaults.
- Restricted Skill to Implement Cybersecurity Controls: Conventional OT techniques continuously have a restricted capability to use cybersecurity measures. For instance, they may have been supplied earlier than the significance of cybersecurity was acknowledged and managed by OEMs, complicating their security.
- Third-Get together Distant Connections: Older OT techniques would possibly help distant connections from third events to handle OT gadgets linked to an inner community. Intruders can goal a community established by a vendor and exploit it to infect different gadgets.
- Lack of Safety Consciousness: Operators and technicians who handle legacy OT techniques might lack security consciousness and coaching, making them weak to social engineering assaults.
- Embedded or Simple-to-Guess Credentials: Sure OT gadgets, reminiscent of these within the IoT class, would possibly possess inherent or predictable passwords, together with different potential design shortcomings.

Security and reliability
In Operational Know-how environments, the first focus is sustaining the protection and reliability of the bodily processes they management. It is a important departure from conventional IT environments, the place the main target is commonly on the confidentiality and integrity of knowledge.
- Security: OT techniques management bodily processes that may have real-world penalties in the event that they malfunction. For instance, in an influence plant, a failure within the management system may result in a shutdown or perhaps a catastrophic occasion. Subsequently, making certain the protection of those techniques is paramount.
- Reliability: OT techniques have to be out there and performance appropriately to make sure the graceful operation of bodily processes. Any downtime can result in important operational disruptions and monetary losses.
In distinction, in OT environments, confidentiality (stopping unauthorized entry to data) and integrity (making certain that information stays correct and unaltered) usually take a backseat. Whereas these parts are important, they often do not maintain as a lot weight as security and reliability.
This order of precedence can have an effect on the implementation of cybersecurity measures. A cybersecurity motion that safeguards information (boosting confidentiality and integrity) however jeopardizes the dependability of an OT system may not be deemed appropriate. As an illustration, a security patch may rectify a recognized vulnerability (enhancing integrity), however you would possibly contemplate it unsuitable if it leads to system instability (undermining reliability).
Whereas many cybersecurity greatest practices and frameworks concentrate on conventional IT environments, OT may also profit. For instance, OWASP Prime 10 addresses internet software cybersecurity considerations reminiscent of injection, damaged authentication, delicate information publicity, and security misconfigurations, that are frequent vulnerabilities that can be present in OT environments. OWASP additionally has a separate record for the Web of Issues (IoT), which is commonly a significant factor of OT environments.
Cybersecurity methods in OT environments have to be rigorously designed to steadiness the necessity for security and reliability with the necessity for information confidentiality and integrity
Thus, cybersecurity methods in OT environments should be rigorously designed to steadiness the necessity for security and reliability with the necessity for information confidentiality and integrity. This usually requires a distinct strategy than conventional IT security, focusing extra on minimizing disruptions to bodily processes. It is a delicate balancing act that requires deep information of operational processes and potential cyber threats.
Securing OT environments requires a distinct strategy in comparison with conventional data know-how security. It requires understanding OT techniques’ distinctive traits and necessities, in addition to designing cybersecurity measures that may defend them with out compromising their operation.
As IT and OT proceed to converge, the significance of OT cybersecurity will solely improve. Using encryption is essential for safeguarding delicate information and communications. Nonetheless, older OT techniques may not have the potential to help encryption, which exposes them to assaults that might jeopardize the confidentiality and integrity of knowledge.
What does cybersecurity like this price? Not as a lot as you assume. Get a quote for the easiest-to-use enterprise-grade PAM resolution out there each within the cloud and on-premise.