Cisco says that personal recordsdata lately downloaded by a risk actor from a misconfigured public-facing DevHub portal do not comprise data that could possibly be exploited in future breaches of the corporate’s programs.
Whereas analyzing the uncovered paperwork, the corporate discovered that their contents embody information that Cisco publishes for patrons and different DevHub customers. Nonetheless, recordsdata that should not have been made public had been additionally obtainable, some belonging to CX Skilled Companies prospects.
“To this point, in our analysis, we have decided {that a} restricted set of CX Skilled Companies prospects had recordsdata included and we notified them straight,” Cisco stated.
“Our groups have listed and proceed assessing the content material of these recordsdata, and we proceed to make regular progress. Now we have not recognized any data within the content material that an actor might have used to entry any of our manufacturing or enterprise environments.”
Cisco has since corrected the configuration, restored public entry to the DevHub web site, and says that net engines like google didn’t index the uncovered paperwork.
This replace comes after Cisco confirmed final month that it took its public DevHub web site offline (a useful resource heart for patrons the place it publishes software program code, templates, and scripts) after a risk actor leaked what the corporate described on the time as “personal” information.
The corporate added that it discovered no proof that any monetary information or private data had been uncovered or stolen from the general public DevHub portal earlier than it was taken offline.
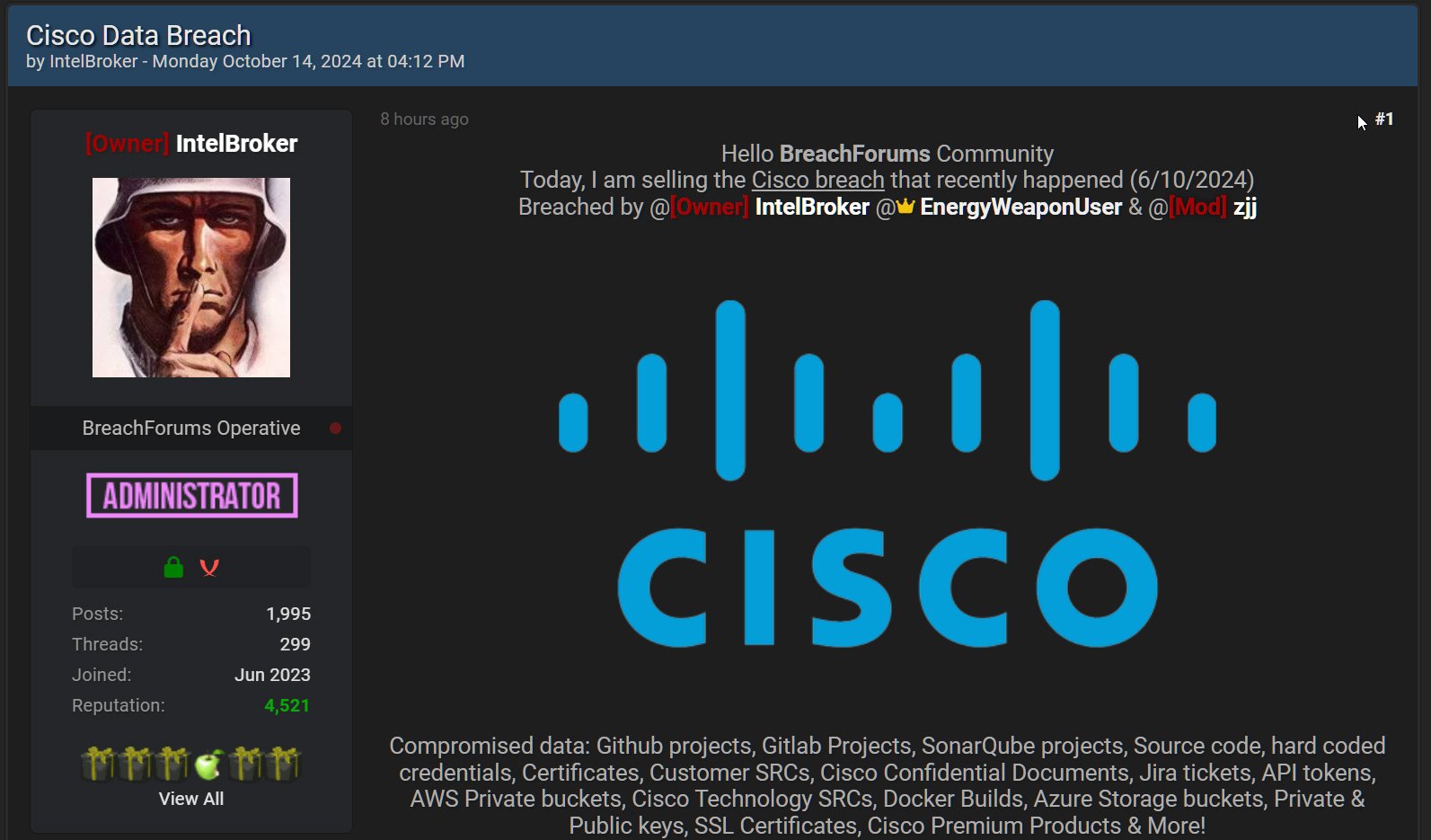
IntelBroker (the risk actor behind the leak) instructed BeelpingComputer additionally they allegedly gained entry to a Cisco JFrog developer surroundings by means of an uncovered API token.
Screenshots and recordsdata the risk actor shared with BeelpingComputer confirmed they gained entry to supply code, configuration recordsdata with database credentials, technical documentation, and SQL recordsdata.
Whereas Cisco says its programs have not been breached, data shared by the risk actor signifies that additionally they breached a third-party improvement surroundings, permitting them to steal information.
BleepingComputer contacted Cisco with additional questions on IntelBroker’s claims, however the firm has not replied.




