At the very least two completely different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security flaws in Ivanti Join Safe VPN home equipment.
UNC5325 abused CVE-2024-21893 to ship a variety of recent malware referred to as LITTLELAMB.WOOLTEA, PITSTOP, PITDOG, PITJET, and PITHOOK, in addition to tried to take care of persistent entry to compromised home equipment, Mandiant mentioned.
The Google-owned risk intelligence agency has assessed with reasonable confidence that UNC5325 is related to UNC3886 owing to supply code overlaps in LITTLELAMB.WOOLTEA and PITHOOK with malware utilized by the latter.
It is price stating that UNC3886 has a monitor file of leveraging zero-day flaws in Fortinet and VMware options to deploy quite a lot of implants like VIRTUALPITA, VIRTUALPIE, THINCRUST, and CASTLETAP.
“UNC3886 has primarily focused the protection industrial base, know-how, and telecommunication organizations situated within the U.S. and [Asia-Pacific] areas,” Mandiant researchers mentioned.
The lively exploitation of CVE-2024-21893 – a server-side request forgery (SSRF) vulnerability within the SAML element of Ivanti Join Safe, Ivanti Coverage Safe, and Ivanti Neurons for ZTA – by UNC5325 is alleged to have occurred as early as January 19, 2024, focusing on a restricted variety of units.
The assault chain entails combining CVE-2024-21893 with a beforehand disclosed command injection vulnerability tracked as CVE-2024-21887 to achieve unauthorized entry to vulnerable home equipment, finally resulting in the deployment of a brand new model of BUSHWALK.
Some situations have additionally concerned the misuse of official Ivanti elements, equivalent to SparkGateway plugins, to drop extra payloads. This consists of the PITFUEL plugin to load a malicious shared object codenamed LITTLELAMB.WOOLTEA, which comes with capabilities to persist throughout system improve occasions, patches, and manufacturing facility resets.
“Whereas the restricted makes an attempt noticed to take care of persistence haven’t been profitable up to now as a result of an absence of logic within the malware’s code to account for an encryption key mismatch, it additional demonstrates the lengths UNC5325 will go to take care of entry to precedence targets and highlights the significance of making certain community home equipment have the most recent updates and patches,” the corporate identified.
It additional acts as a backdoor that helps command execution, file administration, shell creation, SOCKS proxy, and community site visitors tunneling.
Additionally noticed is one other malicious SparkGateway plugin dubbed PITDOG that injects a shared object referred to as PITHOOK to be able to persistently execute an implant known as PITSTOP that is designed for shell command execution, file write, and file learn on the compromised equipment.
Mandiant described the risk actor as having demonstrated a “nuanced understanding of the equipment and their capability to subvert detection all through this marketing campaign” and utilizing living-off-the-land (LotL) strategies to fly beneath the radar.
The cybersecurity agency mentioned it expects “UNC5325 in addition to different China-nexus espionage actors to proceed to leverage zero day vulnerabilities on community edge units in addition to appliance-specific malware to achieve and keep entry to focus on environments.”
Hyperlinks Discovered Between Volt Storm and UTA0178
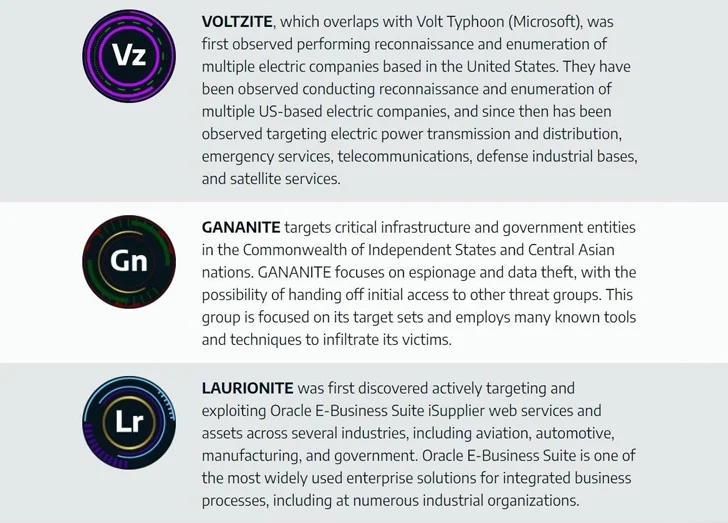
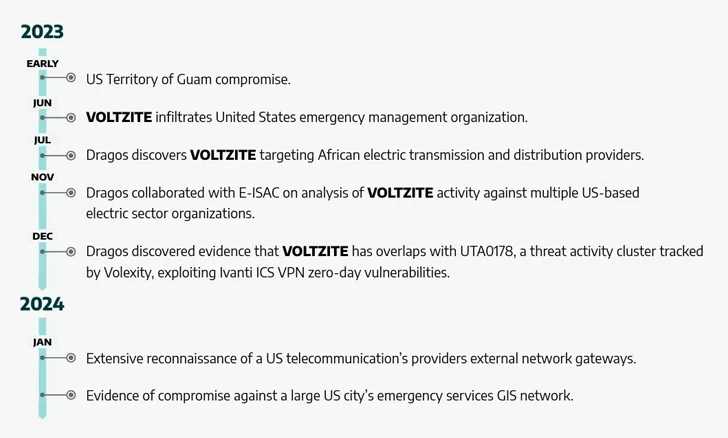
The disclosure comes as industrial cybersecurity firm Dragos attributed China-sponsored Volt Storm (aka Voltzite) to reconnaissance and enumeration actions aimed toward a number of U.S.-based electrical corporations, emergency companies, telecommunication suppliers, protection industrial bases, and satellite tv for pc companies.
“Voltzite’s actions in the direction of U.S. electrical entities, telecommunications, and GIS programs signify clear aims to establish vulnerabilities inside the nation’s important infrastructure that may be exploited sooner or later with damaging or disruptive cyber assaults,” it mentioned.
Volt Storm’s victimology footprint has since expanded to incorporate African electrical transmission and distribution suppliers, with proof connecting the adversary to UTA0178, a risk exercise group linked to the zero-day exploitation of Ivanti Join Safe flaws in early December 2023.
The cyber espionage actor, which closely depends on LotL strategies to sidestep detection, joins two different new teams, specifically Gananite and Laurionite, that got here to gentle in 2023, conducting long-term reconnaissance and mental property theft operations focusing on important infrastructure and authorities entities.
“Voltzite makes use of very minimal tooling and prefers to conduct their operations with as little a footprint as attainable,” Dragos defined. “Voltzite closely focuses on detection evasion and long-term persistent entry with the assessed intent of long-term espionage and knowledge exfiltration.”
(The story has been up to date after publication to emphasise that the makes an attempt to attain persistence on the VPN home equipment have been unsuccessful.)




