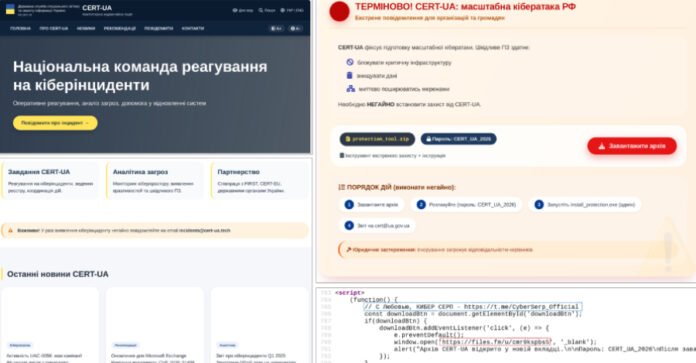
The Laptop Emergency Response Workforce of Ukraine (CERT-UA) has disclosed particulars of a brand new phishing marketing campaign wherein the cybersecurity company itself was impersonated to distribute a distant administration instrument referred to as AGEWHEEZE.
As a part of the assaults, the risk actors, tracked as UAC-0255, despatched emails on March 26 and 27, 2026, posing as CERT-UA to distribute a password-protected ZIP archive hosted on Recordsdata.fm and urged recipients to put in the “specialised software program.”
The targets of the marketing campaign included state organizations, medical facilities, security corporations, academic establishments, monetary establishments, and software program improvement corporations. Among the emails had been despatched from the e-mail tackle “incidents@cert-ua[.]tech.”
The ZIP file (“CERT_UA_protection_tool.zip”) is designed to obtain malware packaged as security software program from the company. The malware, per CERT-UA, is a distant entry trojan codenamed AGEWHEEZE.
A Go-based malware, AGEWHEEZE communicates with an exterior server (“54.36.237[.]92”) over WebSockets and helps a variety of instructions to execute instructions, carry out file operations, modify the clipboard, emulate mouse and keyboard, take screenshots, and handle processes and providers. It additionally creates persistence by utilizing a scheduled job, modifying the Home windows Registry, or including itself to the Startup listing.

The assault is assessed to have been largely unsuccessful. “No various contaminated private gadgets belonging to staff of academic establishments of assorted types of possession had been recognized,” the company mentioned. “The crew’s specialists offered the mandatory methodological and sensible help.”
An evaluation of the bogus web site “cert-ua[.]tech” has revealed that it was seemingly generated with help from synthetic intelligence (AI) instruments, with the HTML supply code additionally together with a remark: “С Любовью, КИБЕР СЕРП,” that means “With Love, CYBER SERP.”
In posts on Telegram, Cyber Serp claims that they’re “cyber-underground operatives from Ukraine.” The Telegram channel was created in November 2025 and has greater than 700 subscribers.
The risk actor additionally mentioned the phishing emails had been despatched to 1 million ukr[.]internet mailboxes as a part of the marketing campaign, and that over 200,000 gadgets have been compromised. “We aren’t bandits – the typical Ukrainian citizen won’t ever endure because of our actions,” it mentioned in a put up.
Final month, Cyber Serp took accountability for an alleged breach of Ukrainian cybersecurity firm Cipher, stating it obtained an entire dump of the servers, together with a shopper database and supply code for his or her line of CIPS merchandise, amongst others.
In an announcement on its web site, Cipher acknowledged that attackers compromised the credentials of an worker at certainly one of its expertise corporations however mentioned its infrastructure was working usually. The contaminated person had entry to a single mission, which didn’t include delicate information, it added.