Safety flaws in Telit Cinterion mobile modems, broadly utilized in sectors together with industrial, healthcare, and telecommunications, might permit distant attackers to execute arbitrary code by way of SMS.
A set of eight separate points, seven of them with identifiers CVE-2023-47610 by CVE-2023-47616 and one other that has but to be registered, have been disclosed final November by security researchers at Kaspersky’s ICS CERT division.
Earlier than publishing the security points, the security firm had reported them to the seller in February 2023.
On Saturday, on the OffensiveCon convention in Berlin, Alexander Kozlov and Sergey Anufrienko shall be offering low stage technical particulars concerning the security points and the way a risk actor might exploit them to take management of susceptible Telit Cinterion units.
SMS to gadget takeover
Probably the most extreme of the vulnerabilities is CVE-2023-47610, a heap overflow downside that impacts the modem’s Consumer Aircraft Location (SUPL) message handlers.
Kaspersky, in collaboration with Telit and primarily based on a radical evaluation of the technical particulars, assigned it a severity rating of 8.8 out of the utmost 10. Nonetheless, NIST’s evaluation is that the problem has essential influence and obtained a severity rating of 9.8.
Attackers exploiting the flaw by way of specifically crafted SMS messages might set off the vulnerability and execute arbitrary code remotely on the modem with out requiring authentication.
In a report shared with BleepingComputer, the researchers say that the SMS messaging interface is current on all modems and that accessing it’s potential if the subscriber variety of the goal modem within the mobile operator’s community is thought.
They clarify that operator restrictions might generally forestall sending binary SMS however a faux base station ought to bypass this limitation.
“In keeping with the transmission protocol, the ULPSizeFromPacket and wapTpduLen variables are calculated independently,” the researchers be aware within the technical report.
“These variables are interrelated solely within the a part of WAP messages reception algorithm: the sum of the sizes of all obtained WAP messages in a UPL message should not exceed ULPSizeFromPacket.”
“However the algorithm used to obtain WAP messages doesn’t examine it. Subsequently, a obtained WAP packet of measurement wapTpduLen shall be copied to a buffer of measurement ULPSizeFromPacket.”
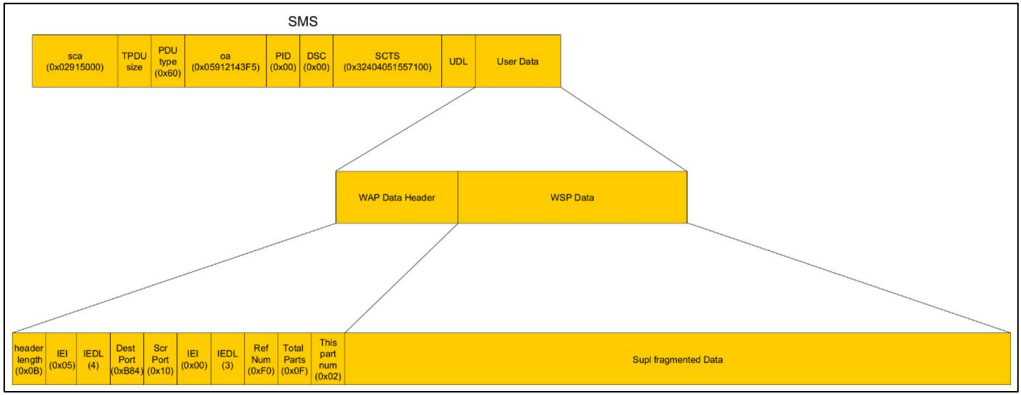
Supply: Kaspersky
By exploiting CVE-2023-47610 to execute arbitrary code by way of SMS, an attacker can get deep-level entry to the modem’s working system.
“This entry additionally facilitates the manipulation of RAM and flash reminiscence, rising the potential to grab full management over the modem’s functionalities—all with out authentication or requiring bodily entry to the gadget” – Kaspersky
Though the remainder of the vulnerabilities that Kaspersky researchers found obtained a decrease severity rating, they can be utilized to compromise the integrity of MIDlets – Java-based functions with numerous capabilities.
In keeping with Kaspersky, an attacker might obtain code execution with elevated privileges (producer stage) by circumventing digital signature checks (CVE-2023-47611). This may pose a risk not simply to information confidentiality and integrity but additionally to broader community security and gadget integrity.
Though the analysis focused the Cinterion EHS5-E sequence modem, as a result of different merchandise from the seller have comparable software program and {hardware} structure extra variants are additionally impacted:
- Cinterion BGS5
- Cinterion EHS5/6/7
- Cinterion PDS5/6/8
- Cinterion ELS61/81
- Cinterion PLS62
Telit fastened a few of the disclosed vulnerabilities however some stay unpatched, Kaspersky advised BleepingComputer.
“The vulnerabilities we discovered, coupled with the widespread deployment of those units in numerous sectors, spotlight the potential for intensive international disruption,” says Evgeny Goncharov, head of Kaspersky ICS CERT.
Goncharov notes that as a result of the modems are embedded in different options, it’s a problem to find out which merchandise are impacted.
The security firm has some suggestions to mitigate the threats, which is many of the instances potential by working with the telecom operator. One technique is to disable SMS sending to impacted units and utilizing a securely configured non-public APN.
Kaspersky additionally recommends imposing utility signature verification to stop the set up of untrusted MIDIets on the modem and take measures to stop unauthorized bodily entry to the units.




