An 18-year-old flaw within the NGINX open-source net server, found utilizing an autonomous scanning system, could be exploited for denial of service and, underneath sure situations, distant code execution.
The vulnerability is tracked as CVE-2026-42945 and acquired a crucial severity score of 9.2, primarily based on the newest model of the Frequent Vulnerability Scoring System (CVSS).
Three extra reminiscence corruption security points had been found in the identical six-hour code scanning session by researchers at AI-native security firm DepthFirst AI.
NGINX is a massively used net server and reverse proxy platform, powering a 3rd of the highest ranked web sites. It may possibly effectively stability load by distributing incoming community visitors to a number of backend servers and scale back load instances by caching content material.
Owned and maintained by American tech agency F5, the net server is utilized by cloud suppliers, SaaS firms, banks, media platforms, e-commerce websites, and in Kubernetes clusters.
CVE-2026-42945 is a heap buffer overflow in ngx_http_rewrite_module affecting NGINX variations 0.6.27 by 1.30.0, which has been within the mission’s code for roughly 18 years.
Based on DepthFirst, the vulnerability could be triggered when NGINX configurations use each the ‘rewrite’ and ‘set’ directives, a sample the researchers say is widespread in API gateways and reverse proxy setups.
The flaw stems from inconsistent state dealing with in NGINX’s inner script engine, which processes rewrites in two passes: one to calculate the quantity of reminiscence to allocate, and one to repeat the precise knowledge.
An ‘is_args’ flag stays set after a rewrite containing ‘?’, inflicting NGINX to calculate buffer dimension utilizing unescaped URI lengths however later write bigger escaped knowledge like ‘+’ and ‘&’, resulting in a heap buffer overflow.
The researchers demonstrated unauthenticated code execution through specifically crafted HTTP requests that corrupt adjoining NGINX reminiscence pool constructions, overwrite cleanup handler pointers, spray faux constructions into reminiscence through POST request our bodies, and drive NGINX to execute ‘system()’ throughout pool cleanup.
Nonetheless, distant code execution was achieved on a system with the Deal with Area Structure Randomization (ASLR) safety towards memory-based assaults turned off. This protection is energetic by default, however it may be disabled to extend efficiency in some environments, similar to embedded programs and digital machines used for evaluation.
DepthFirst notes that NGINX’s multi-process structure makes exploitation simpler as a result of employee processes inherit almost equivalent reminiscence layouts from the grasp course of, enabling dependable heap manipulation and repeated makes an attempt if a employee crashes.
“If our exploit fails and crashes a employee, the grasp course of merely spawns a brand new one with the very same reminiscence structure,” the researchers clarify.
“This enables us to securely attempt a number of instances till we succeed with out worrying concerning the employee crashing and altering the reminiscence structure.”
“Theoretically, we may leverage this design to leak ASLR (Deal with Area Structure Randomization) by progressively overwriting pointers byte by byte.”
The opposite three flaws uncovered by DepthFirst acquired a medium severity score:
- CVE-2026-42946 — extreme reminiscence allocation in SCGI/UWSGI modules that may crash employees through ~1 TB allocations (excessive severity)
- CVE-2026-40701 — use-after-free in asynchronous OCSP DNS decision dealing with (medium severity)
- CVE-2026-42934 — off-by-one UTF-8 parsing bug inflicting out-of-bounds reads (medium severity)
Affect and fixes
The vulnerabilities had been found on April 18, 2026, and reported to the seller on April 21.
Based on F5’s security advisory, launched yesterday, the failings influence the next NGINX builds:
- NGINX Open Supply variations 0.6.27 by 1.30.0
- NGINX Plus R32 by R36
- NGINX Occasion Supervisor 2.16.0 by 2.21.1
- F5 WAF for NGINX 5.9.0 by 5.12.1
- NGINX App Shield WAF 4.9.0 by 4.16.0 and 5.1.0 by 5.8.0
- F5 DoS for NGINX 4.8.0
- NGINX App Shield DoS 4.3.0 by 4.7.0
- NGINX Gateway Cloth 1.3.0 by 1.6.2 and a couple of.0.0 by 2.5.1
- NGINX Ingress Controller 3.5.0 by 3.7.2, 4.0.0 by 4.0.1, and 5.0.0 by 5.4.1
Fixes had been made obtainable in NGINX Open Supply 1.31.0 and 1.30.1, NGINX Plus R36 P4, and NGINX Plus R32 P6.
For these unable to improve, F5 recommends changing unnamed PCRE seize teams ($1, $2, and so on.) in susceptible ‘rewrite’ guidelines with named captures, which eliminates the principle exploitation prerequisite.
Exploitability in the actual world
Some security researchers have pushed again on the real-world exploitability claims surrounding CVE-2026-42945, arguing that DepthFirst’s proof-of-concept depends on extremely particular situations that aren’t generally current in default deployments.
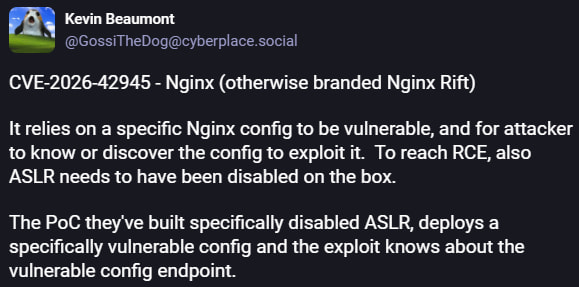
Researcher Kevin Beaumont famous that exploitation requires a susceptible NGINX configuration utilizing explicit rewrite patterns, the attacker should know or uncover the affected endpoint, and the revealed RCE PoC was examined with ASLR disabled.
Beaumont burdened that the researchers’ exploit was constructed towards a intentionally susceptible setup and doesn’t display dependable code execution towards hardened real-world programs
AlmaLinux echoed an identical evaluation of their advisory, after independently reproducing the flaw.
The Linux distribution maintainers confirmed that crashing NGINX employee processes through a crafted request is trivial and dependable, making denial-of-service assaults lifelike.
Nonetheless, they said that turning the heap overflow into reliable distant code execution on programs with ASLR enabled “shouldn’t be trivial,” and they don’t anticipate a generic, dependable exploit to emerge from depthfirst’s work.
On the similar time, AlmaLinux cautioned that “not simple” doesn’t imply unattainable, and the DoS potential is sufficient by itself to deal with the problem as pressing.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




