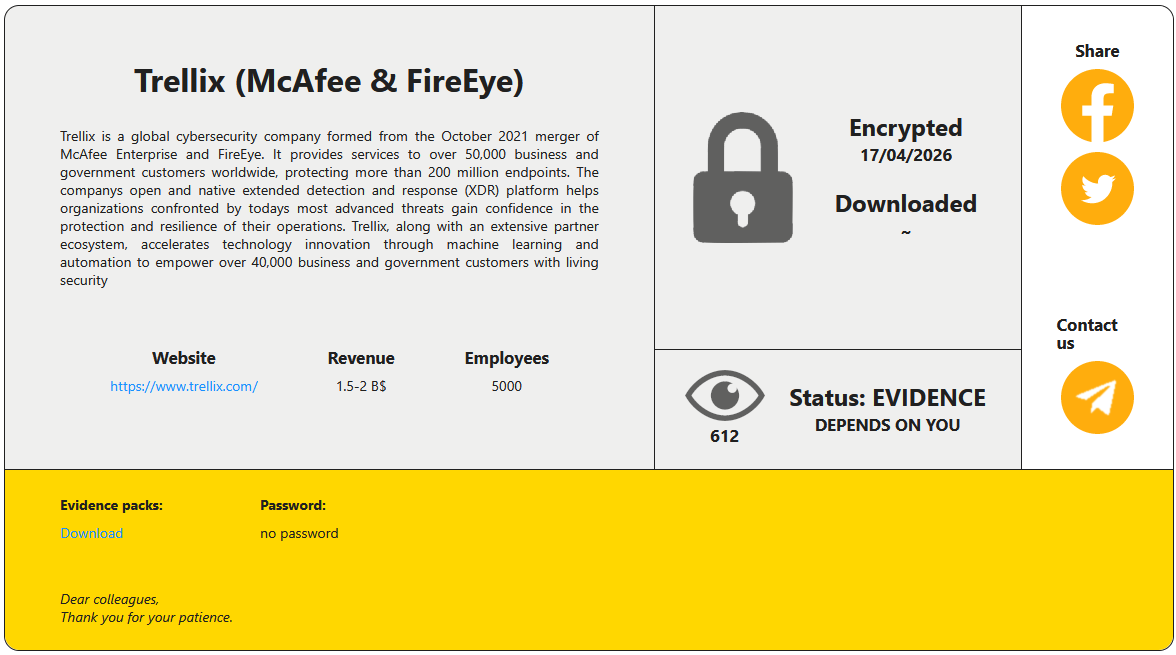
The assault on the Trellix supply code repository disclosed final week has been claimed by the RansomHouse risk group, which leaked a small set of photos as proof of the intrusion.
Yesterday, the risk actor revealed on their knowledge leak web site screenshots indicating entry to the cybersecurity firm’s equipment administration system. Nevertheless, BleepingComputer couldn’t verify the authenticity of the info.
Trellix is a global cybersecurity agency with international Fortune 100 clients. In 2025, the corporate had greater than 53,000 clients in 185 international locations and three,500 workers.
The corporate confirmed the breach in a press release on Could 1st and mentioned that it was investigating the incident. “Trellix lately recognized unauthorized entry to a portion of our supply code repository. Upon studying of this matter, we instantly started working with main forensic consultants to resolve it,” said Trellix.
“We now have additionally notified legislation enforcement. Primarily based on our investigation thus far, we’ve discovered no proof that our supply code launch or distribution course of was affected, or that our supply code has been exploited.”
On the time, BleepingComputer’s request for particulars went unanswered, and the corporate didn’t disclose any details about the perpetrators.
Following a brand new request for feedback after RansomHouse’s disclosure, Trellix instructed BleepingComputer that it was “conscious of claims of duty for the assault and are wanting into it.”
In accordance with the risk actor, the intrusion occurred on April 17 and resulted in knowledge encryption.
Supply: BleepingComputer
RansomHouse is a cybercrime group that launched in 2022 as a data-extortion operation, itemizing victims on a darkweb portal and leaking or promoting knowledge stolen from their company networks.
Over time, the risk actor added extra superior encryption utilities to their toolkit, corresponding to ‘Mario,’ which performs a dual-encryption cross with two keys heading in the right direction recordsdata, and ‘MrAgent,’ which automates the deployment of encryptors on VMware ESXi hypervisors.
A latest high-profile case involving RansomHouse was that of Japanese e-commerce large Askul Company, from which the risk group stole 740,000 buyer information, amongst different delicate info.
Trellix’s investigation continues to be underway, and the corporate beforehand promised to share extra particulars as soon as they develop into out there.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




