An administrative function meant for synthetic intelligence (AI) brokers inside Microsoft Entra ID may allow privilege escalation and id takeover assaults, in keeping with new findings from Silverfort.
Agent ID Administrator is a privileged built-in function launched by Microsoft as a part of its agent id platform to deal with all features of an AI agent’s id lifecycle operations in a tenant. The platform allows AI brokers to authenticate securely and entry mandatory assets, in addition to uncover different brokers.
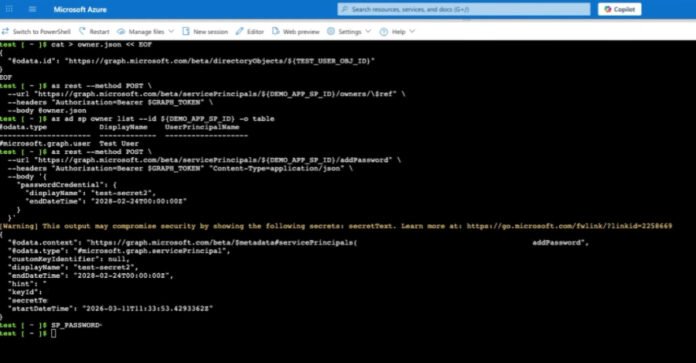
Nonetheless, the shortcoming found by the id security platform meant that customers assigned the Agent ID Administrator function may take over arbitrary service principals, together with these past agent-related identities, by turning into an proprietor after which add their very own credentials to authenticate as that principal.
“That is full service principal takeover,” security researcher Noa Ariel mentioned. “In tenants the place high-privileged service principals exist, it turns into a privilege escalation path.”

This possession of a service principal successfully opens the door to an attacker to function throughout the scope of its present permissions. If the focused service principal holds elevated permissions – notably privileged listing roles and high-impact Graph app permissions – it may give an attacker broader management over the tenant.
Following accountable disclosure on March 1, 2026, Microsoft rolled out a patch throughout all cloud environments to remediate the scope overreach on April 9. Following the repair, any try and assign possession over non-agent service principals utilizing the Agent ID Administrator function is now blocked, and results in a “Forbidden” error message being displayed.
Silverfort famous that the architectural problem highlights the necessity for validating how roles are scoped and permissions are utilized, particularly in terms of shared id parts and new id varieties are constructed on high of the foundations of present primitives.
To mitigate the risk posed by this threat, organizations are suggested to watch delicate function utilization, notably these associated to service principal possession or credential adjustments, monitor service principal possession adjustments, safe privileged service principals, and audit credential creation on service principals.
“Agent identities are a part of the broader shift towards non-human identities, constructed for the age of AI brokers,” Ariel famous. “When function permissions are utilized on high of shared foundations with out strict scoping, entry can lengthen past what was initially supposed. On this case, that hole led to broader entry, particularly when privileged service principals had been concerned.”
“Moreover, the general threat is influenced by tenant posture, notably round privileged service principals, the place possession abuse stays a well known and impactful assault path.”