A high-severity security flaw in LMDeploy, an open-source toolkit for compressing, deploying, and serving LLMs, has come underneath energetic exploitation within the wild lower than 13 hours after its public disclosure.
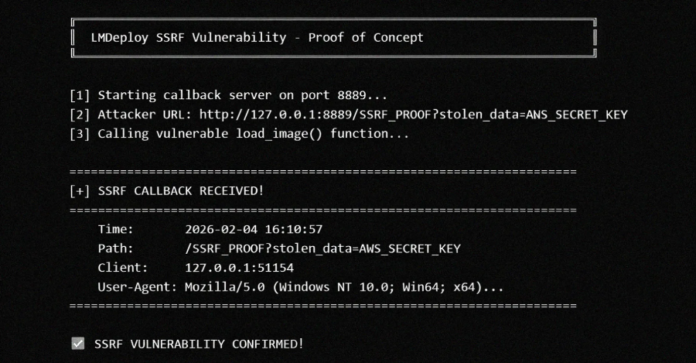
The vulnerability, tracked as CVE-2026-33626 (CVSS rating: 7.5), pertains to a Server-Aspect Request Forgery (SSRF) vulnerability that might be exploited to entry delicate knowledge.
“A server-side request forgery (SSRF) vulnerability exists in LMDeploy’s vision-language module,” in response to an advisory revealed by the venture maintainers final week. “The load_image() perform in lmdeploy/vl/utils.py fetches arbitrary URLs with out validating inner/personal IP addresses, permitting attackers to entry cloud metadata providers, inner networks, and delicate sources.”
The shortcoming impacts all variations of the toolkit (0.12.0 and prior) with imaginative and prescient language assist. Orca Safety researcher Igor Stepansky has been credited with discovering and reporting the bug.
Profitable exploitation of the vulnerability may allow an attacker to steal cloud credentials, attain inner providers that are not uncovered to the web, port scan inner networks, and create lateral motion alternatives.
Cloud security agency Sysdig, in an evaluation revealed this week, mentioned it detected the primary LMDeploy exploitation try in opposition to its honeypot techniques inside 12 hours and 31 minutes of the vulnerability being revealed on GitHub. The exploitation try originates from the IP tackle 103.116.72[.]119.
“The attacker didn’t merely validate the bug and transfer on. As a substitute, over a single eight-minute session, they used the vision-language picture loader as a generic HTTP SSRF primitive to port-scan the interior community behind the mannequin server: AWS Occasion Metadata Service (IMDS), Redis, MySQL, a secondary HTTP administrative interface, and an out-of-band (OOB) DNS exfiltration endpoint,” it mentioned.
The actions undertaken by the adversary, detected on Apr 22, 2026, at 03:35 a.m. UTC, unfolded over 10 distinct requests throughout three phases, with the requests switching between imaginative and prescient language fashions (VLMs) corresponding to internlm-xcomposer2 and OpenGVLab/InternVL2-8B to seemingly keep away from elevating any suspicion –
- Goal AWS IMDS and Redis situations on the server.
- Take a look at egress with an out-of-band (OOB) DNS callback to requestrepo[.]com to substantiate the SSRF vulnerability can attain arbitrary exterior hosts, adopted by enumerating the API floor.
- Port scan the loopback interface (“127.0.0[.]1”)
The findings are yet one more reminder of how risk actors are intently watching new vulnerability disclosures and exploiting them earlier than downstream customers can apply the fixes, even in circumstances the place no proof-of-concept (PoC) exploits exist on the time of the assault.
“CVE-2026-33626 suits a sample that we’ve got noticed repeatedly within the AI-infrastructure house over the previous six months: important vulnerabilities in inference servers, mannequin gateways, and agent orchestration instruments are being weaponized inside hours of advisory publication, whatever the dimension or extent of their set up base,” Sysdig mentioned.
“Generative AI (GenAI) is accelerating this collapse. An advisory as particular as GHSA-6w67-hwm5-92mq, which incorporates the affected file, parameter title, root-cause clarification, and pattern weak code, is successfully an enter immediate for any business LLM to generate a possible exploit.”
WordPress Plugins and Web-Uncovered Modbus Units Focused
The disclosure comes as risk actors have additionally been noticed exploiting vulnerabilities in two WordPress plugins – Ninja Types – File Add (CVE-2026-0740, CVSS rating: 9.8) and Breeze Cache (CVE-2026-3844, CVSS rating: 9.8) – to add arbitrary recordsdata to prone websites, which end in arbitrary code execution and full takeover.
Unknown attackers have additionally been linked to a world marketing campaign focusing on internet-exposed, Modbus-enabled programmable logic controllers (PLCs) from September to November 2025 that spanned 70 international locations and 14,426 distinct focused IPs, most of that are situated within the U.S., France, Japan, Canada, and India. A subset of those requests has been discovered to emanate from sources geolocated to China.

“The exercise blended large-scale automated probing with extra selective patterns that counsel deeper system fingerprinting, disruption makes an attempt, and potential manipulation paths when PLCs are reachable from the general public web,” Cato Networks researchers mentioned. “Many supply IPs had low or zero public fame scores, in step with contemporary or rotating scanning hosts.”