Particulars have emerged a few now-patched security vulnerability in a broadly used third-party Android software program improvement equipment (SDK) known as EngageLab SDK that might have put hundreds of thousands of cryptocurrency pockets customers at danger.
“This flaw permits apps on the identical system to bypass Android security sandbox and achieve unauthorized entry to personal information,” the Microsoft Defender Safety Analysis Workforce stated in a report printed as we speak.
EngageLab SDK provides a push notification service, which, in accordance with its web site, is designed to ship “well timed notifications” primarily based on person habits already tracked by builders. As soon as built-in into an app, the SDK provides a method to ship personalised notifications and drive real-time engagement.
The tech large stated a major variety of apps utilizing the SDK are a part of the cryptocurrency and digital pockets ecosystem, and that the affected pockets apps accounted for greater than 30 million installations. When non‑pockets apps constructed on the identical SDK are included, the set up rely surpasses 50 million.
Microsoft didn’t reveal the names of the apps, however famous that each one these detected apps utilizing weak variations of the SDK have been faraway from the Google Play Retailer. Following accountable disclosure in April 2025, EngageLab launched model 5.2.1 in November 2025 to deal with the vulnerability.
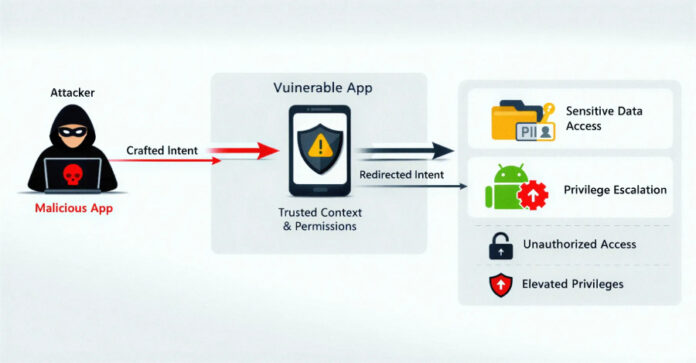
The problem, recognized in model 4.5.4, has been described as an intent redirection vulnerability. Intents in Android refer to messaging objects that are used to request an motion from one other app part.
Intent redirection happens when the contents of an intent {that a} weak app sends are manipulated by taking benefit of its trusted context (i.e., permissions) to realize unauthorized entry to protected parts, expose delicate information, or escalate privileges inside the Android atmosphere.
An attacker might exploit this vulnerability by means of a malicious app put in on the system by means of another means to entry inner directories related to an app that has the SDK built-in, leading to unauthorized entry to delicate information.
There isn’t any proof that the vulnerability was ever exploited in a malicious context. That stated, builders who combine the SDK are beneficial to replace to the newest model as quickly as potential, particularly provided that even trivial flaws in upstream libraries can have cascading impacts and affect hundreds of thousands of units.
“This case reveals how weaknesses in third‑social gathering SDKs can have massive‑scale security implications, particularly in excessive‑worth sectors like digital asset administration,” Microsoft stated. “Apps more and more depend on third‑social gathering SDKs, creating massive and sometimes opaque provide‑chain dependencies. These dangers enhance when integrations expose exported parts or depend on belief assumptions that aren’t validated throughout app boundaries.”