The U.S. Cybersecurity and Infrastructure Safety Company (CISA) ordered federal businesses to safe FortiClient Enterprise Administration Server (EMS) situations in opposition to an actively exploited vulnerability by Friday.
Tracked as CVE-2026-35616, this security flaw was found by cybersecurity agency Defused, which described it as a pre-authentication API entry bypass that may enable attackers to bypass authentication and authorization controls fully.
Fortinet launched emergency hotfixes over the weekend to handle the vulnerability and mentioned the security subject stems from an improper entry management weak point that unauthenticated attackers can exploit to execute code or instructions through specifically crafted requests.
The corporate additionally warned that menace actors had been exploiting it in zero-day assaults and warned IT directors to safe their EMS situations as quickly as doable by making use of the hotfixes or upgrading to FortiClient EMS model 7.4.7 when it turns into obtainable.
“Fortinet has noticed this to be exploited within the wild and urges susceptible prospects to put in the hotfix for FortiClient EMS 7.4.5 and seven.4.6,” the corporate mentioned.
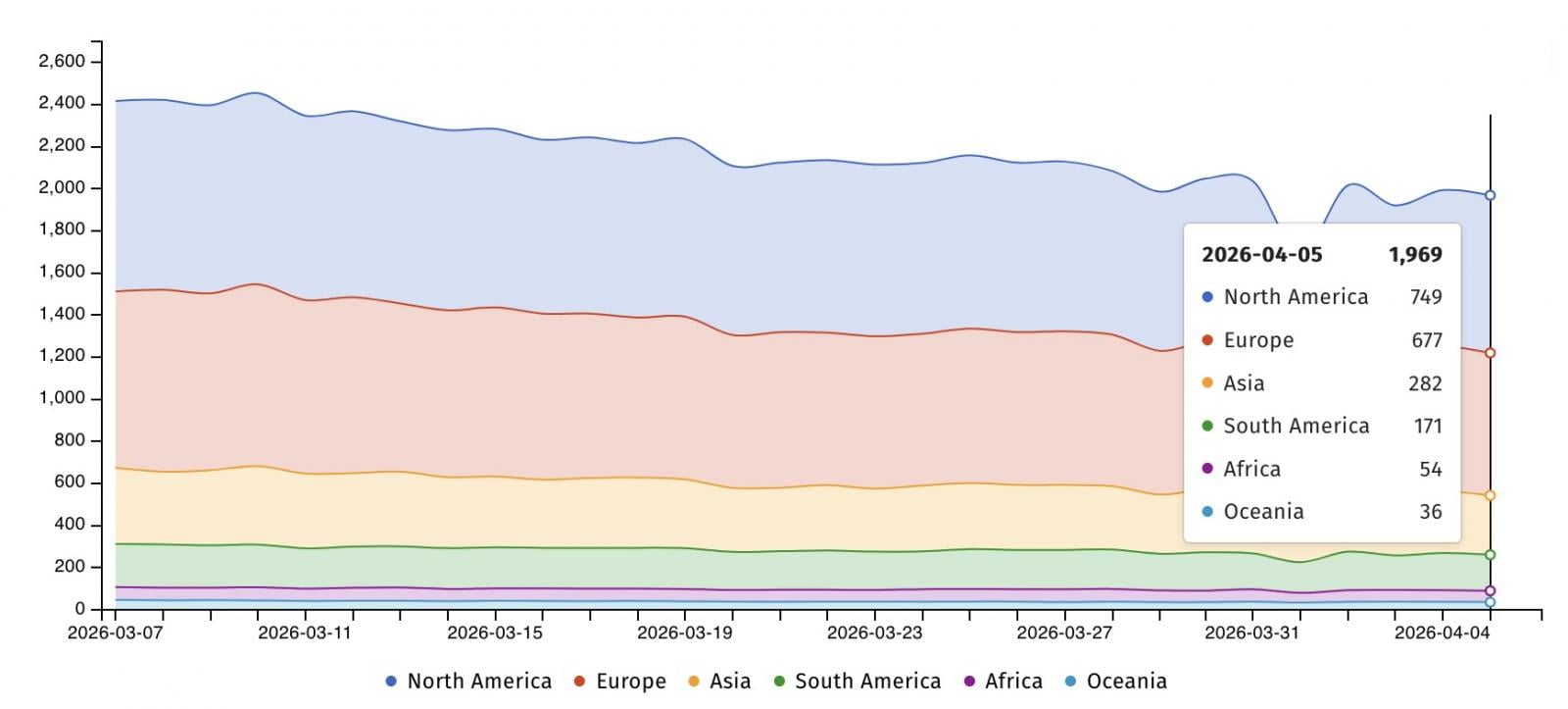
Web security watchdog group Shadowserver presently tracks almost 2,000 FortiClient EMS situations uncovered on-line, with greater than 1,400 IPs in the US and in Europe. Nonetheless, there are not any particulars on what number of have already been patched or have susceptible configurations.
On Monday, CISA added CVE-2026-35616 to its Identified Exploited Vulnerabilities (KEV) Catalog and ordered Federal Civilian Government Department (FCEB) businesses to patch FortiClient EMS situations by Thursday midnight, April 9, as mandated by Binding Operational Directive (BOD) 22-01.
“The sort of vulnerability is a frequent assault vector for malicious cyber actors and poses important dangers to the federal enterprise,” the cybersecurity company warned.
“Apply mitigations per vendor directions, observe relevant BOD 22-01 steerage for cloud providers, or discontinue use of the product if mitigations are unavailable.”
Regardless that BOD 22-01 applies solely to U.S. federal businesses, CISA urged all defenders (together with these within the personal sector) to prioritize patching for CVE-2026-35616 and safe their organizations’ networks as quickly as doable.
Fortinet patched one other crucial FortiClient EMS flaw (CVE-2026-21643) in February, which was additionally flagged lower than two weeks in the past as exploited in assaults.
Fortinet vulnerabilities are sometimes exploited in cyber espionage campaigns and ransomware assaults (typically as zero-day bugs) to breach company networks. Most not too long ago, Fortinet blocked FortiCloud SSO connections from units working susceptible firmware variations to mitigate CVE-2026-24858 zero-day assaults.

Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, exhibits the place protection ends, and supplies practitioners with three diagnostic questions for any instrument analysis.




