Citrix has patched two vulnerabilities affecting NetScaler ADC networking home equipment and NetScaler Gateway safe distant entry options, one of which is similar to the CitrixBleed and CitrixBleed2 flaws exploited in zero-day assaults lately.
The crucial security bug (tracked as CVE-2026-3055) stems from inadequate enter validation, which may result in a reminiscence overread on Citrix ADC or Citrix Gateway home equipment configured as a SAML identification supplier (IDP), doubtlessly enabling distant attackers with out privileges to steal delicate data akin to session tokens.
“Cloud Software program Group strongly urges affected prospects of NetScaler ADC and NetScaler Gateway to put in the related up to date variations as quickly as attainable,” the corporate warned in a Monday advisory.
Citrix has additionally shared detailed steerage on tips on how to establish and patch NetScaler cases susceptible to CVE-2026-3055.
The corporate additionally patched the CVE-2026-4368 vulnerability affecting home equipment configured as Gateways (SSL VPN, ICA Proxy, CVPN, RDP proxy) or AAA digital servers, which may allow menace actors with low privileges on the focused system to take advantage of a race situation in low-complexity assaults, doubtlessly resulting in consumer session mix-ups.
The 2 flaws have an effect on NetScaler ADC and NetScaler Gateway variations 13.1 and 14.1 (mounted in 13.1-62.23 and 14.1-66.59) and NetScaler ADC 13.1-FIPS and 13.1-NDcPP (addressed in 13.1-37.262).
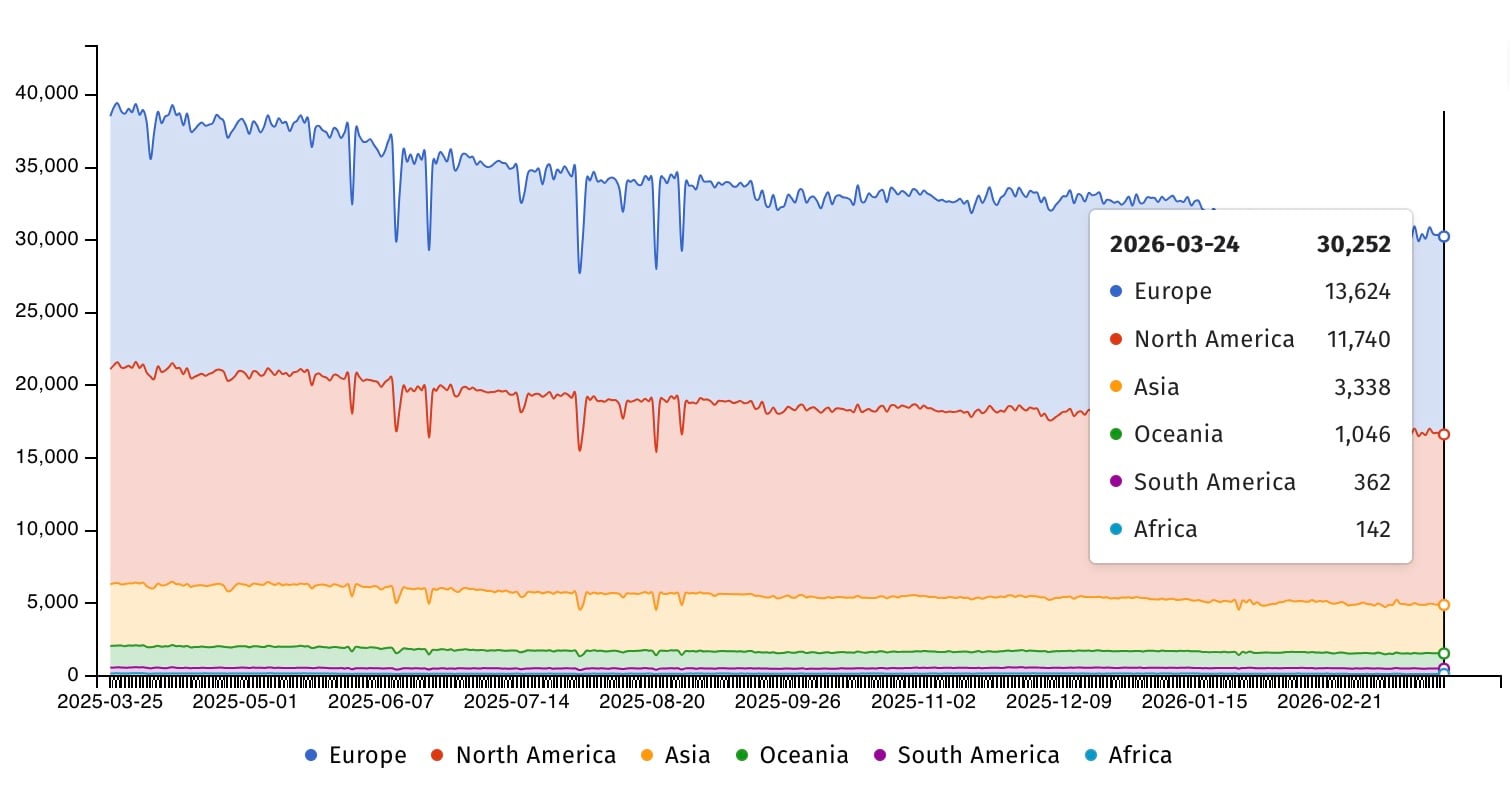
Web security watchdog group Shadowserver is at present monitoring over 30,000 NetScaler ADC cases and greater than 2,300 Gateway cases uncovered on-line. Nevertheless, there may be at present no data relating to what number of of them are utilizing susceptible configurations or have already been patched towards assaults.
Since Citrix launched security updates to handle the vulnerability, a number of cybersecurity corporations have warned that it’s important to safe NetScaler towards assaults concentrating on CVE-2026-3055.
Lots of them have additionally identified apparent similarities to the CitrixBleed and CitrixBleed2 out-of-bounds memory-read vulnerabilities exploited in zero-day assaults lately.
“Sadly, many will recognise this as sounding just like the broadly exploited ‘CitrixBleed’ vulnerability from 2023 and the following ‘CitrixBleed2’ variant disclosed in 2025, each of which have been and proceed to be actively leveraged in real-world assaults,” cybersecurity firm watchTowr mentioned.
“Though Citrix states that the vulnerability was recognized internally, it’s affordable to anticipate that menace actors will try and reverse engineer the patch to develop exploit capabilities.”
“Exploitation of CVE-2026-3055 is more likely to happen as soon as exploit code turns into public. Due to this fact, it’s essential that prospects operating affected Citrix programs remediate this vulnerability as quickly as attainable; Citrix software program has beforehand seen reminiscence leak vulnerabilities broadly exploited within the wild, together with the notorious ‘CitrixBleed’ vulnerability, CVE-2023-4966, in 2023,” Rapid7 added.
In August 2025, CISA flagged CitrixBleed2 as actively exploited and gave federal companies a single day to safe their programs. In whole, the U.S. cybersecurity company has tagged 21 Citrix vulnerabilities as exploited within the wild, seven of which have been utilized in ransomware assaults.

Malware is getting smarter. The Purple Report 2026 reveals how new threats use math to detect sandboxes and conceal in plain sight.
Obtain our evaluation of 1.1 million malicious samples to uncover the highest 10 strategies and see in case your security stack is blinded.




