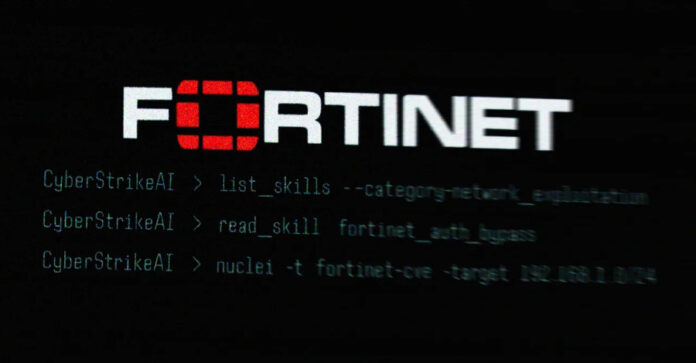
The risk actor behind the just lately disclosed synthetic intelligence (AI)-assisted marketing campaign focusing on Fortinet FortiGate home equipment leveraged an open-source, AI-native security testing platform known as CyberStrikeAI to execute the assaults.
The brand new findings come from Workforce Cymru, which detected its use following an evaluation of the IP handle (“212.11.64[.]250”) that was utilized by the suspected Russian-speaking risk actor to conduct automated mass scanning for weak home equipment.
CyberStrikeAI is an “open-source synthetic intelligence (AI) offensive security instrument (OST) developed by a China-based developer who we assess has some ties to the Chinese language authorities,” security researcher Will Thomas (aka @BushidoToken) stated.
Particulars of the AI-powered exercise got here to mild final month when Amazon Menace Intelligence stated it detected the unknown attacker systematically focusing on FortiGate gadgets utilizing generative synthetic intelligence (AI) companies like Anthropic Claude and DeepSeek, compromising over 600 home equipment in 55 nations.
In accordance with the outline in its GitHub repository, CyberStrikeAI is inbuilt Go and integrates greater than 100 security instruments to allow vulnerability discovery, attack-chain evaluation, data retrieval, and outcome visualization. It is maintained by a Chinese language developer who goes by the net alias Ed1s0nZ.
Workforce Cymru stated it noticed 21 distinctive IP addresses working CyberStrikeAI between January 20 and February 26, 2026, with servers primarily hosted in China, Singapore, and Hong Kong. Extra servers associated to the instrument have been detected within the U.S., Japan, and Switzerland.
The Ed1s0nZ account, apart from internet hosting CyberStrikeAI, has printed a number of different instruments that reveal their curiosity in exploitation and jailbreaking AI fashions –
- watermark-tool, so as to add invisible digital watermarks to paperwork.
- banana_blackmail, a Golang-based ransomware,
- PrivHunterAI, a Golang-based instrument that makes use of Kimi, DeepSeek, and GPT fashions to detect privilege escalation vulnerabilities.
- ChatGPTJailbreak, which accommodates a README.md file with prompts to jailbreak OpenAI ChatGPT by tricking it into getting into a Do Something Now (DAN) mode or asking it to behave as ChatGPT with Developer Mode enabled.
- InfiltrateX, a Golang-based scanner for detecting privilege escalation vulnerabilities.
- VigilantEye, a Golang-based instrument that displays the disclosure of delicate info, akin to telephone numbers and ID card numbers, in databases. It is configured to ship an alert by way of a WeChat Work bot if a possible data breach is detected.
“Additional, Ed1s0nZ’s GitHub actions point out they work together with organisations that assist probably Chinese language authorities state-sponsored cyber operations,” Thomas stated. “This consists of Chinese language non-public sector corporations which have identified ties to the Chinese language Ministry of State Safety (MSS).”
One such firm the developer has interacted with is Knownsec 404, a Chinese language security vendor that suffered a significant leak of greater than 12,000 inner paperwork late final 12 months, exposing the agency’s worker information, authorities clientele, hacking instruments, giant volumes of stolen information akin to South Korean name logs and data associated to Taiwan’s important infrastructure organizations, and the inside workings of ongoing cyber operations focusing on different nations.

“Ostensibly, KnownSec gave the impression to be simply one other security firm, however that is solely a half fact,” DomainTools famous in an evaluation printed this January, describing it as a “state-aligned cyber contractor” able to supporting Chinese language nationwide security, intelligence, and navy goals.
“In actuality, […] it has a shadow group that works for the PLA, MSS, and the organs of the Chinese language security state. This leak exposes an organization that operates far past the function of a typical cybersecurity vendor. Instruments like ZoomEye and the Crucial Infrastructure Goal Library give China a worldwide reconnaissance system that catalogs hundreds of thousands of international IPs, domains, and organizations mapped by sector, geography, and strategic worth.”
Ed1s0nZ has additionally been noticed making lively modifications to a README.md file situated in an eponymous repository, eradicating references to them having been honored with the Stage 2 Contribution Award to the China Nationwide Vulnerability Database of Info Safety (CNNVD). The developer has additionally claimed that “every little thing shared right here is solely for analysis and studying.”
In accordance with analysis printed by Bitsight final month, China maintains two completely different vulnerability databases: CNNVD and the Chinese language Nationwide Vulnerability Database (CNVD). Whereas CNNVD is overseen by the Ministry of State Safety, CNVD is managed by CNCERT. Earlier findings from Recorded Future have revealed that CNNVD takes longer to publish vulnerabilities with greater CVSS scores than vulnerabilities with decrease ones.
“The developer’s current try to clean references to the CNNVD from their GitHub profile factors to an lively effort to obscure these state ties, prone to defend the instrument’s operational viability as its recognition grows,” Thomas stated. “The adoption of CyberStrikeAI is poised to speed up, representing a regarding evolution within the proliferation of AI-augmented offensive security instruments.”