Taiwan networking supplier Zyxel has launched security updates to deal with a crucial vulnerability affecting over a dozen router fashions that may permit unauthenticated attackers to realize distant command execution on unpatched gadgets.
Tracked as CVE-2025-13942, this command injection security flaw was discovered within the UPnP operate of Zyxel 4G LTE/5G NR CPE, DSL/Ethernet CPE, Fiber ONTs, and wi-fi extenders.
Zyxel says that unauthenticated distant attackers can exploit it to execute working system (OS) instructions on an affected machine utilizing maliciously crafted UPnP SOAP requests.

Nevertheless, CVE-2025-13942 assaults will possible be extra restricted than the severity ranking suggests, as profitable exploitation requires UPnP and WAN entry to be enabled, with the latter disabled by default.
“It is very important notice that WAN entry is disabled by default on these gadgets, and the assault might be carried out remotely provided that each WAN entry and the weak UPnP operate have been enabled,” Zyxel stated. “Customers are strongly suggested to put in the patches to keep up optimum safety.”
On Tuesday, Zyxel additionally patched two high-severity post-authentication command-injection vulnerabilities (CVE-2025-13943 and CVE-2026-1459) that permit risk actors to execute OS instructions utilizing compromised credentials.
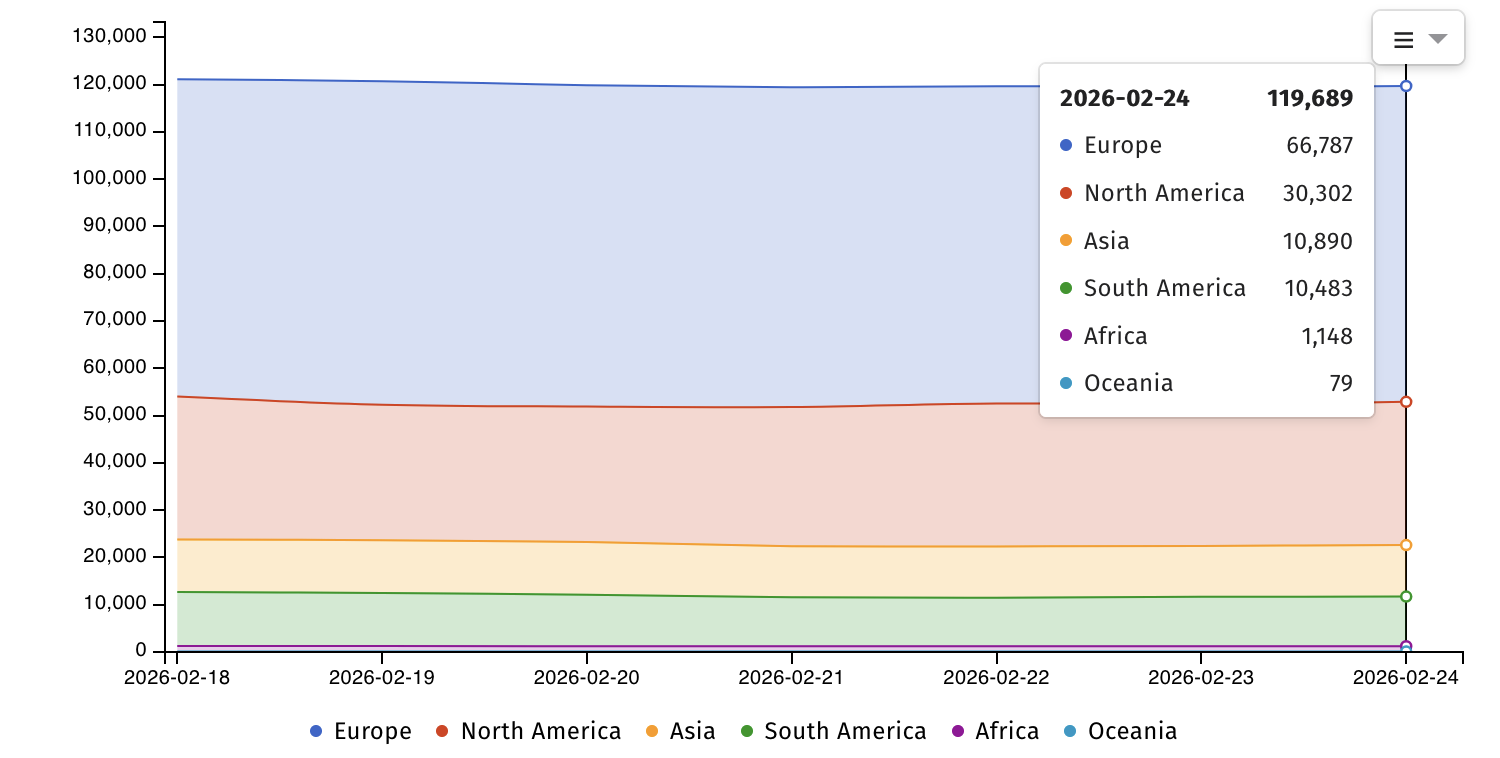
Web security watchdog Shadowserver at present tracks practically 120,000 Web-exposed Zyxel gadgets, together with over 76,000 routers.
Zyxel gadgets are sometimes focused in assaults since they’re supplied by many web service suppliers worldwide because the default out-of-the-box gear when activating a brand new web service contract.
The U.S. Cybersecurity and Infrastructure Safety Company (CISA) is at present monitoring 12 Zyxel vulnerabilitiesimpacting the corporate’s routers, firewalls, and NAS gadgets which were or are nonetheless actively exploited within the wild.
Earlier this month, Zyxel warned that it has no plans to patch a pair of zero-day security vulnerabilities (CVE-2024-40891 and CVE-2024-40891) which can be actively exploited in assaults and have an effect on end-of-life routers nonetheless obtainable on the market on-line. As an alternative, the corporate “strongly” suggested clients to interchange their routers with newer merchandise whose firmware has already been patched.
“VMG1312-B10A, VMG1312-B10B, VMG1312-B10E, VMG3312-B10A, VMG3313-B10A, VMG3926-B10B, VMG4325-B10A, VMG4380-B10A, VMG8324-B10A, VMG8924-B10A, SBG3300, and SBG3500, are legacy merchandise which have reached end-of-life (EOL) for years,” stated Zyxel. “Due to this fact, we strongly suggest that customers change them with newer-generation merchandise for optimum safety.”
Zyxel claims that greater than 1 million companies use its networking merchandise throughout 150 markets.

Fashionable IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, learn the way your workforce can cut back hidden handbook delays, enhance reliability by automated response, and construct and scale clever workflows on high of instruments you already use.




