Attackers are continuously on the prowl, scoping out vulnerabilities of network-connected units in your techniques. These units—laptops, desktops, servers, IoT, and extra—are like unlocked doorways ready for risk actors to walk via. And right here’s the kicker: many of those vulnerabilities are shockingly frequent and simply preventable.
Let’s break down the weaknesses we most continuously observe throughout three million endpoints (not a nasty pattern dimension!) and what you are able to do to patch these holes earlier than a risk actor sneaks in and wreaks havoc.
Distant Desktop Protocol (RDP): The open again door
Distant Desktop Protocol is a prolific protocol used for distant connectivity, but it surely’s additionally one of the vital frequent methods risk actors achieve entry to endpoint units. Actually, as much as 70% of organizations have RDP uncovered to the general public web. Consider an uncovered RDP connection as leaving a spare key beneath the doormat—whereas not fairly in plain sight, it’s a fairly apparent place to look if you wish to get inside.
Right here’s an instance of what occurs:
Attackers usually use brute pressure assaults on RDP, biking via password choices till they unlock a login session. As soon as the preliminary intrusion is established, they normally don’t waste time dropping malware and attempting to maneuver laterally throughout your community.
An instance of occasion logs displaying a profitable use of brute pressure.
What you are able to do:
- Don’t expose RDP to the general public web until you really want to.
- Be a stickler with admin rights. Take into consideration who truly wants entry to do their job.
- Don’t depend on passwords—it’s old-fashioned (and method too dangerous). Implement multi-factor authentication (MFA) for RDP classes.
- Don’t slack on Home windows security configurations. Defaults received’t lower it in opposition to attackers who desire a piece of your community.
- Be vigilant for suspicious exercise, like logins from unknown IP addresses.
Phishing assaults: Don’t take the bait
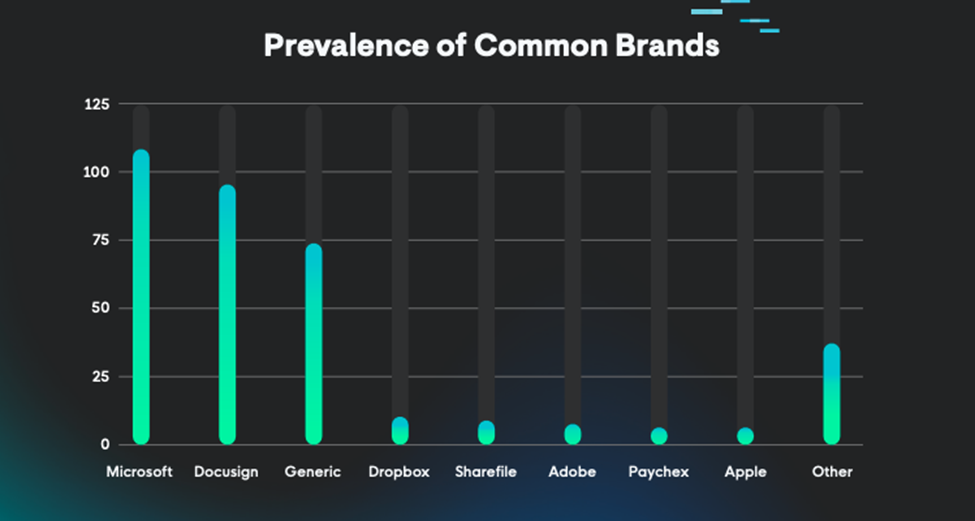
E mail phishing is a traditional cybercrime technique, and a few issues simply by no means exit of fashion. Each day, phishing emails land in inboxes and a staggering variety of victims nonetheless fall for social engineering scams. This isn’t a brand new tactic by any stretch of the creativeness, however risk actors proceed to depend on it as a result of it really works—phishing accounts for 15% of all data breaches. However what’s extra alarming about phishing assaults lately is that they’re getting craftier, particularly as risk actors flip to generative AI instruments to fast-track their social engineering techniques. From expertly mimicked branding to pretend invoices with pressing requests, hackers have leveled up their recreation to trick victims into clicking malicious hyperlinks or giving up private particulars to “customer support” over the telephone. Phishing isn’t simply e mail anymore—hackers will use any sort of communication mechanism: e mail, textual content, telephone calls, voicemail, QR codes, or any mixture of those approaches.
Right here’s an instance of what occurs:
Let’s check out e mail phishing. When an worker clicks on a malicious hyperlink in a phishing e mail, they could unknowingly hand over delicate credentials to an attacker or set up malware on their system. Or, even worse, they might detonate a ransomware assault. Phishing usually makes use of stress techniques to prey on victims’ feelings to get a fast response. The attackers stroll away with entry to your community and delicate information whereas leaving you with the mess. It might change into an excellent greater mess than you’ve bargained for if the attacker positive aspects persistence to endpoints and also you don’t instantly discover the harm.
Bought an e mail asking for delicate information? Don’t reply on to the sender to keep away from falling into the attacker’s lure.
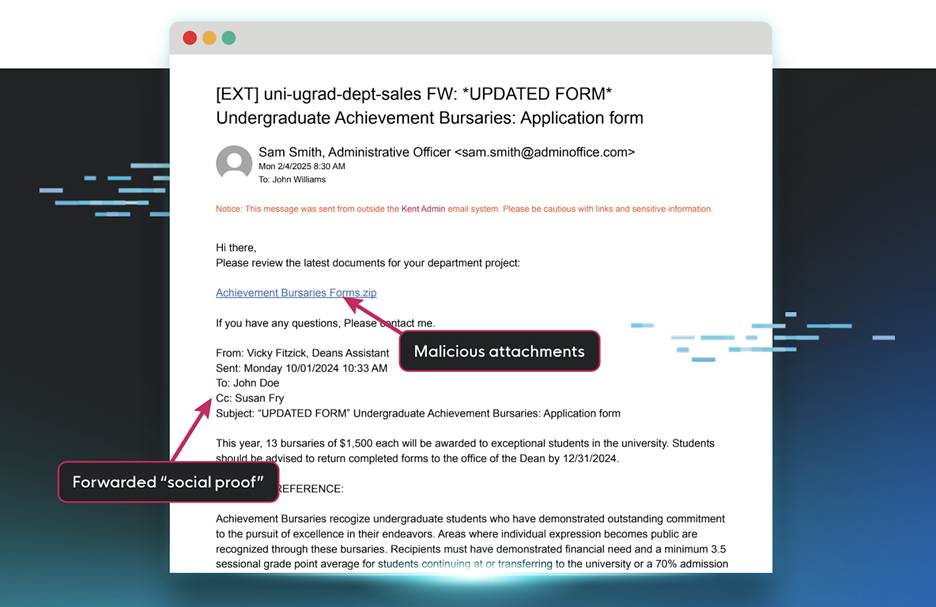
An instance of a malicious pretend thread e mail phishing try.
What you are able to do:
- Get your group good on phishing techniques! Often scheduled security consciousness coaching (SAT) could make customers much less prone to soar on sketchy requests. You need their “spidey senses” tingling when bizarre emails present up!
- Use MFA as a result of it could actually scale back the harm if (when) credentials are compromised.
For extra on how attackers use phishing to entry your endpoints, take a look at Tradecraft Tuesday: “Phishing within the Quick Lane.”
Distant monitoring and administration (RMM) instruments: The double-edged sword
RMM instruments are double-edged swords. On the one hand, they assist IT admins, managed service suppliers (MSPs), and system admins monitor, handle, and troubleshoot fleets of computer systems with ease. However, when left unsecured (as they usually are), RMM instruments are a simple entry level for attackers to hit your endpoints onerous. In line with Huntress’ 2025 Cyber Menace Report, 17.3% of all distant entry strategies originated from RMM abuse. Menace actors wish to mix in and conceal in plain sight, and legit RMM instruments are a simple method to do that.
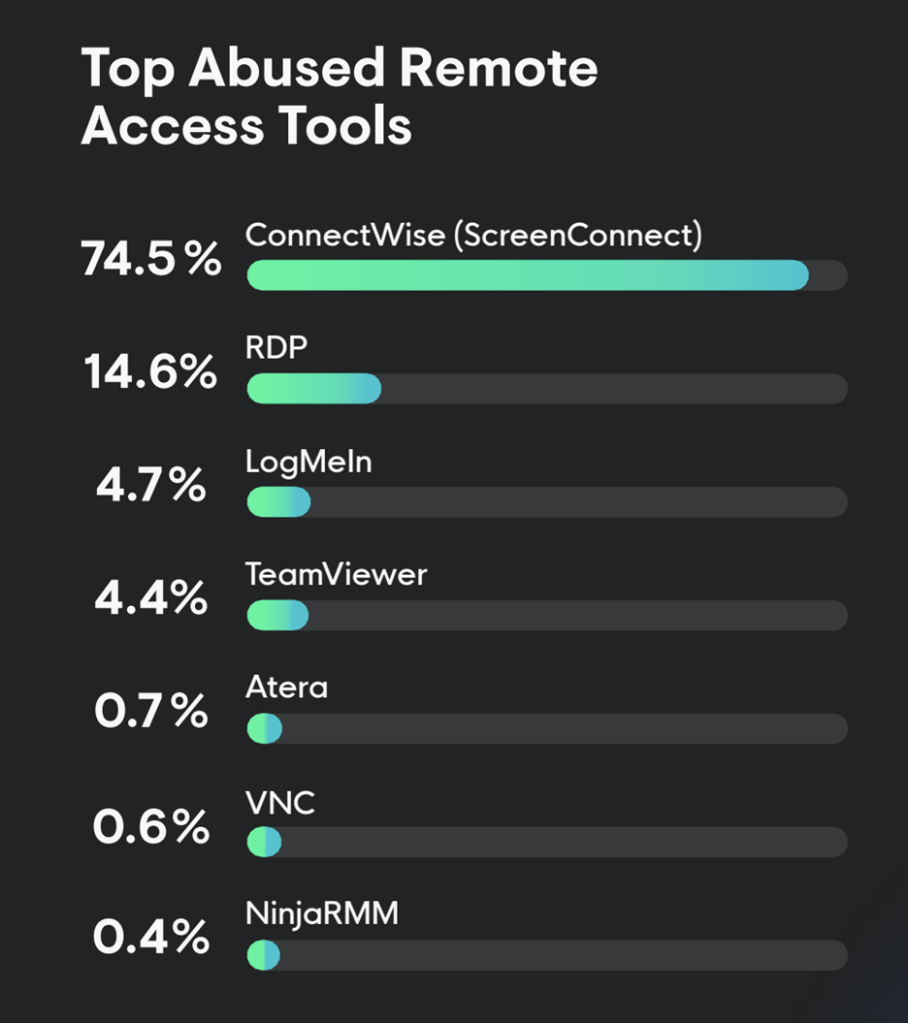
High abused distant entry instruments. Supply.
Right here’s an instance of what occurs:
Attackers abuse RMM software program and instruments to achieve unauthorized distant entry to compromise units. Whether or not they use pre-existing RMMs or set up their very own, they will doubtlessly management each linked machine throughout your group, lurking beneath the auspices of reputable software program. RMM assaults are harmful as a result of there’s all the time a danger that attackers will fly beneath the radar of your detection techniques, shifting laterally and gaining persistence with out even dropping malware.
There are typically two methods attackers abuse RMMs. First, they will hijack or abuse current software program by exploiting outdated, unpatched, or misconfigured instruments, or by stealing credentials to log in remotely to RMM instruments. Second, they will deploy and set up the attacker’s most well-liked RMM software by way of social engineering or moveable executables.
Transportable executables are notable for his or her skill to skirt round admin privileges and full software program set up, giving attackers native person entry. Even when a danger administration management is meant to dam or audit the RMM software program on the community, it doesn’t matter as a result of moveable executables don’t require admin privileges, giving the risk actor a free go into your community. That’s the stuff of nightmares as a result of risk actors drop into your atmosphere undetected with out utilizing malware.
Your RMM instruments ought to make endpoints safer, not much less. Tighten up these settings and maintain potential unhealthy actors out.
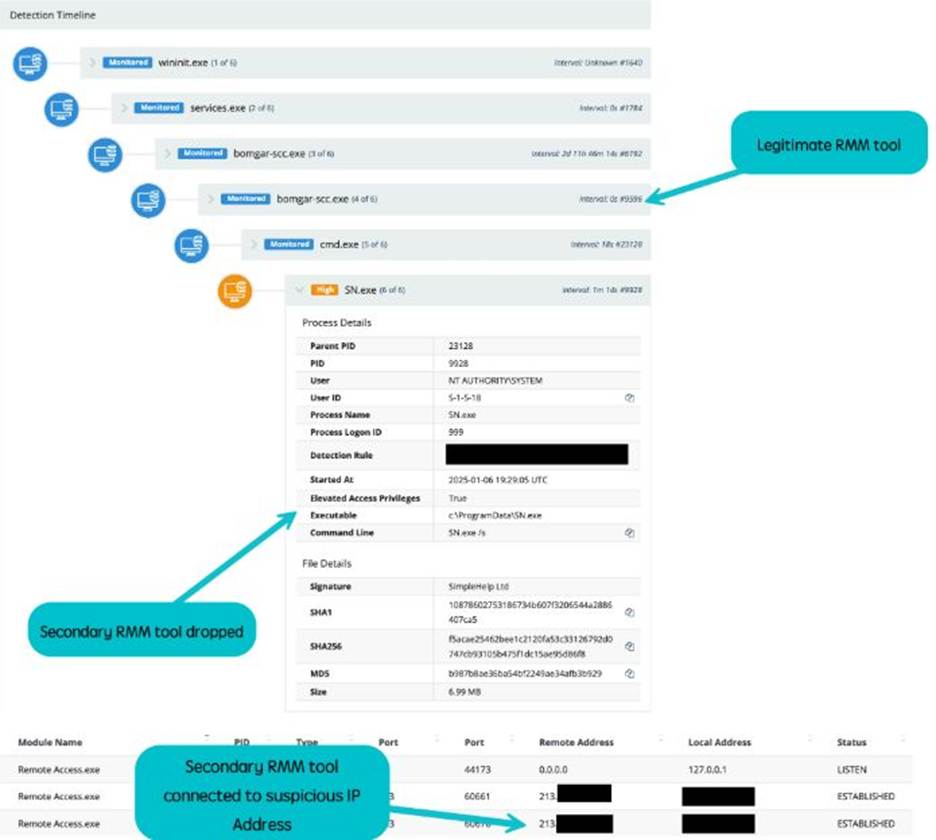
Instance of reputable RMM software compromise.
What you are able to do:
- Use role-based permissions. They’re king. In the event you’re not on the visitor listing, you don’t get entry to the RMM software program occasion.
- Replace and apply patches to RMM software program to handle vulnerabilities and bug fixes.
- Monitor exercise logs for uncommon exercise. Unauthorized installs or funky logins ought to be a crimson flag.
- Know what kinds of RMM instruments are presupposed to be in your community. Audit, observe, and monitor in order that an unauthorized occasion stands out.
For extra on conserving RMM instruments safe, take a look at:
Unpatched software program: An open door to your community
Unpatched software program is the cybersecurity equal of leaving your entrance door open. Sure, the breeze may be good, however you most likely wouldn’t go away it extensive open more often than not. It’s too dangerous. Your pets or children can get free, outside critters could make themselves at house (who desires raccoons of their kitchen?), and worse, thieves can simply stroll in.
In the event you wouldn’t expose your bodily atmosphere to one of these danger, why would you enable it nearly?
Right here’s what occurs:
Software program distributors launch patches for various causes, however usually to repair publicly recognized security vulnerabilities, normally known as CVEs. Attackers use this public data to focus on outdated software program and techniques. A single occasion of an unpatched flaw is a chance for an attacker to drop ransomware or malware, or to tug off data breaches. When a brand new vulnerability drops, you’re up in opposition to the clock to get your techniques patched earlier than a risk actor takes benefit of you.
In the event you’re not updating your software program often, your endpoints are at pointless danger. The door is extensive open for undesirable visitors. It’s that straightforward.
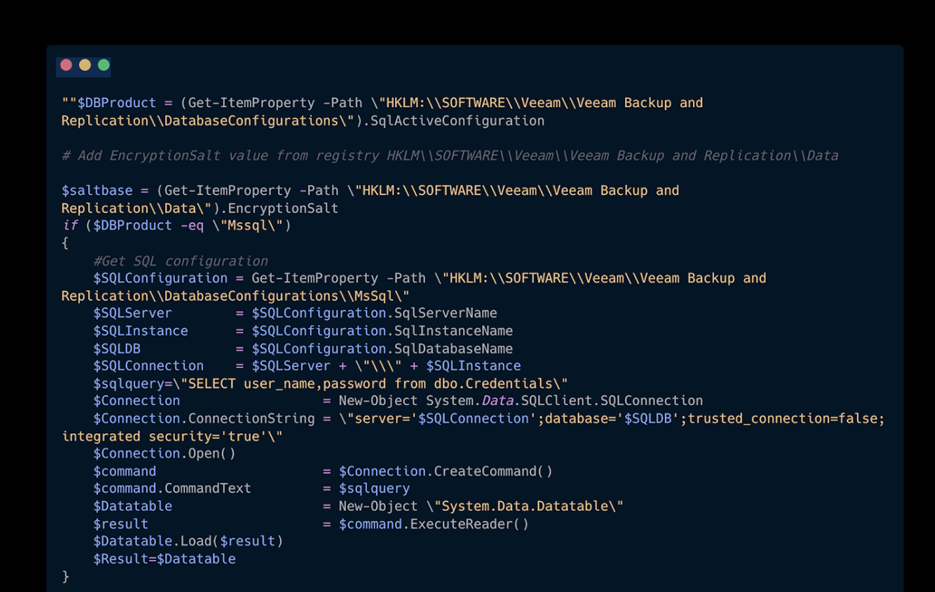
Instance of PowerShell script exploiting CVE-2023-27532 in outdated Veeam software program.
Patch it up:
- Arrange computerized updates wherever doable. No excuses.
- Preserve a daily patch administration schedule and follow it.
- Have a battle plan for patching prioritization, since not all vulnerabilities are created equally.
Keep proactive, keep protected
Endpoint vulnerabilities don’t need to be your Achilles’ heel—they’re manageable with the fitting methods and instruments. Phishing coaching, endpoint detection and response (EDR) options, RMM audits, patch schedules, and robust authentication measures are simply the beginning.
It’s time to take motion and safe your techniques earlier than attackers goal them. Don’t go away it to likelihood. Study your cybersecurity instruments, prepare your workforce, and implement endpoint safety options that suit your setup.
To be taught extra about staying protected with Huntress, go to right here.




