The jsPDF library for producing PDF paperwork in JavaScript functions is weak to a vital vulnerability that permits an attacker to steal delicate knowledge from the native filesystem by together with it in generated information.
The flaw is an area file inclusion and path traversal that permits passing unsanitized paths to the file loading mechanism (loadFile) in jsPDF variations earlier than 4.0. It’s tracked as CVE-2025-68428 and obtained a severity rating of 9.2.
The jsPDF library is a extensively adopted package deal with greater than 3.5 million weekly downloads within the npm registry.

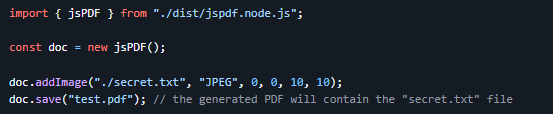
In jsPDF’s Node.js builds, the ‘loadFile’ perform is used for studying the native filesystem. The issue arises when user-controlled enter is handed because the file path, inflicting jsPDF to include into the generated PDF output the content material of the file.
Supply: Parallax
Different file loading strategies are additionally affected, together with ‘addImage’, ‘html’, and ‘addFont’, as all can name the loadFile perform.
In line with the jsPDF security bulletin, the difficulty solely impacts the Node.js builds of the library, particularly the dist/jspdf.node.js and dist/jspdf.node.min.js information.
In an in depth technical report, software security firm Endor Labs says that the exploitation threat is low or nonexistent if file paths are hardcoded, come from a trusted configuration, or strict allowlists are used for inputs.
CVE-2025-68428 was fastened in model 4.0.0 of jsPDF by limiting filesystem entry by default and relying as a substitute on Node.js permission mode.
Nevertheless, Endor Labs researchers notice that this mode is experimental in Node 20, so variations 22.13.0, 23.5.0, or 24.0.0 and later are beneficial.
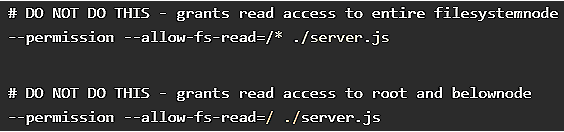
One other caveat to contemplate is that enabling the ‘–permission’ flag, a workaround steered by the builders, impacts all the Node.js course of, not simply jsPDF.
Endor Labs additionally underlines that overly broad filesystem permissions added to the ‘–allow-fs-read’ configuration flag negate the repair.
supply: Endor Labs
The jsPDF crew recommends that older Node variations sanitize user-provided paths earlier than passing them to jsPDF.
Given the broad deployment of jsPDF on quite a few initiatives, CVE-2025-68428 is an efficient candidate for lively exploitation.
It is funds season! Over 300 CISOs and security leaders have shared how they’re planning, spending, and prioritizing for the yr forward. This report compiles their insights, permitting readers to benchmark methods, establish rising traits, and evaluate their priorities as they head into 2026.
Find out how high leaders are turning funding into measurable influence.





