Risk actors exploited a lately patched distant code execution vulnerability (CVE-2025-20352) in older, unprotected Cisco networking gadgets to deploy a Linux rootkit and acquire persistent entry.
The security difficulty leveraged within the assaults impacts the Easy Community Administration Protocol (SNMP) in Cisco IOS and IOS XE and results in RCE if the attacker has root privileges.
In response to cybersecurity firm Development Micro, the assaults focused Cisco 9400, 9300, and legacy 3750G sequence gadgets that didn’t have endpoint detection response options.
Within the authentic bulletin for CVE-2025-20352, up to date on October 6, Cisco tagged the vulnerability as exploited as a zero day, with the corporate’s Product Safety Incident Response Staff (PSIRT) saying it was “conscious of profitable exploitation.”
Development Micro researchers monitor the assaults below the identify ‘Operation Zero Disco’ as a result of the malware units a common entry password that accommodates the phrase “disco.”
The report from Development Micro notes that the menace actor additionally tried to take advantage of CVE-2017-3881, a seven-year-old vulnerability within the Cluster Administration Protocol code in IOS and IOS XE.
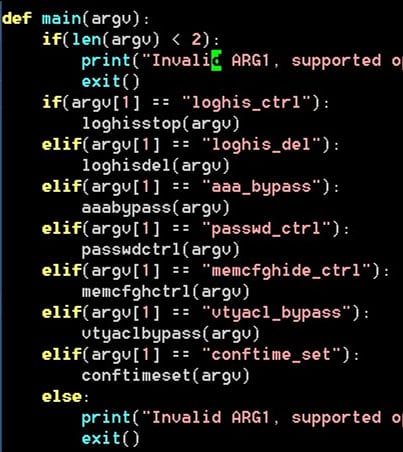
The rootkit planted on weak techniques encompasses a UDP controller that may hear on any port, toggle or delete logs, bypass AAA and VTY ACLs, allow/disable the common password, conceal working configuration objects, and reset the final write timestamp for them.
Supply: Development Micro
In a simulated assault, the researchers confirmed that it’s doable to disable logging, impersonate a waystation IP through ARP spoofing, bypass inside firewall guidelines, and transfer laterally between VLANs.
.jpg)
Supply: Development Micro
Though newer switches are extra resistant to those assaults as a consequence of Handle Area Format Randomization (ASLR) safety, Development Micro says that they aren’t immune and protracted concentrating on may compromise them.
After deploying the rootkit, the malware “installs a number of hooks onto the IOSd, which leads to fileless elements disappearing after a reboot,” the researchers say.
The researchers have been in a position to get well each 32-bit and 64-bit variants of the SNMP exploit.
Development Micro notes that there at the moment exists no instrument that may reliably flag a compromised Cisco swap from these assaults. If there may be suspicion of a hack, the advice is to carry out a low-level firmware and ROM area investigation.
A listing of the indications of compromise (IoCs) related to ‘Operation Zero Disco’ might be discovered right here.

Be part of the Breach and Attack Simulation Summit and expertise the way forward for security validation. Hear from high consultants and see how AI-powered BAS is remodeling breach and assault simulation.
Do not miss the occasion that can form the way forward for your security technique




